80
EPICenter Software Installation and User Guide
Starting EPICenter
Navigating the EPICenter Applications
The EPICenter client consists of two frames:
•
The Navigation Toolbar, from which you can access the EPICenter applets
•
The Main Applet frame, where the currently active applet runs.
The Navigation Toolbar
The Navigation Toolbar, on the left, displays a set of buttons you can use to access various EPICenter
modules. The buttons that appear in this Toolbar may include additional modules, such as the
EPICenter Policy Manager, if you have a license for those modules.
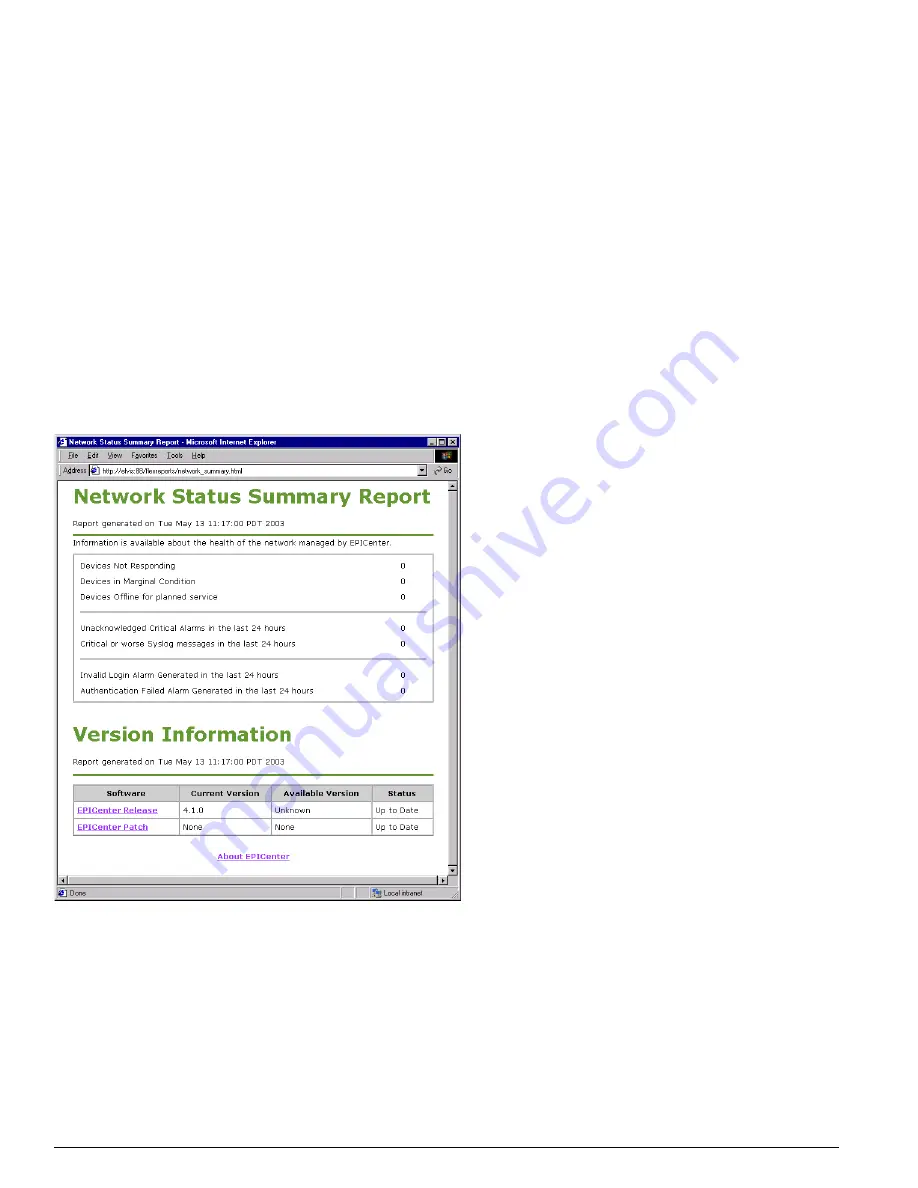
• Home
returns you to the Network Summary Report display shown in Figure 15. From this page, you
can access the About EPICenter page.
Figure 15: The EPICenter Home page
• Inventory
runs the Inventory Manager, where you can discover devices on your network, and set up
device groups and port groups so you can manage network elements in sets rather than individually.
• Alarm
runs the Alarm Manager, where you can view and browse alarms that have occurred on your
network devices, as well as define alarms and the actions that should occur when an alarm happens.
This button also indicates that a new alarm has been received by displaying its label in red text
instead of black text.
Summary of Contents for EPICenter 4.1
Page 20: ...20 EPICenter Software Installation and User Guide Preface ...
Page 46: ...46 EPICenter Software Installation and User Guide EPICenter and Policy Manager Overview ...
Page 190: ...190 EPICenter Software Installation and User Guide Configuration Manager ...
Page 204: ...204 EPICenter Software Installation and User Guide Using the Interactive Telnet Application ...
Page 242: ...242 EPICenter Software Installation and User Guide Using the IP MAC Address Finder ...
Page 266: ...266 EPICenter Software Installation and User Guide Using ExtremeView ...
Page 284: ...284 EPICenter Software Installation and User Guide Real Time Statistics ...
Page 436: ...436 EPICenter Software Installation and User Guide Using the Policy Manager ...
Page 454: ...454 EPICenter Software Installation and User Guide The ACL Viewer ...
Page 468: ...468 EPICenter Software Installation and User Guide Troubleshooting ...
Page 504: ...504 EPICenter Software Installation and User Guide EPICenter External Access Protocol ...
Page 510: ...510 EPICenter Software Installation and User Guide EPICenter Database Views ...
Page 522: ...522 EPICenter Software Installation and User Guide EPICenter Backup ...
Page 526: ...526 EPICenter Software Installation and User Guide Dynamic Link Context System DLCS ...
Page 546: ......






























