Solution B - Without NAT
The setup steps are as follows:
1.
Define a single SIP ALG object using the options described above.
2.
Define a
Service
object which is associated with the SIP ALG object. The service should have:
•
Destination Port set to
5060
(the default SIP signaling port)
•
Type set to
TCP/UDP
•
When using an
IP Policy
object, the
Protocol
property must also be set to
SIP
.
3.
Define four rules/policies in the IP rule set:
•
An
Allow
rule/policy for outbound traffic from the clients on the internal network to the
proxy located on the DMZ interface.
•
An
Allow
rule/policy for outbound traffic from the proxy behind the DMZ interface to the
remote clients on the Internet.
•
An
Allow
rule/policy for inbound SIP traffic from the SIP proxy behind the DMZ interface
to the clients located on the local, protected network.
•
An
Allow
rule/policy for inbound SIP traffic from clients and proxies on the Internet to
the proxy behind the DMZ interface.
4.
If
Record-Route
is not enabled at the proxy, direct exchange of SIP messages must also be
allowed between clients, bypassing the proxy. The following two additional rules are
therefore needed when
Record-Route
is disabled:
•
An
Allow
rule/policy for outbound traffic from the clients on the local network to the
external clients and proxies on the Internet.
•
An
Allow
rule/policy for inbound SIP traffic from the Internet to clients on the local
network.
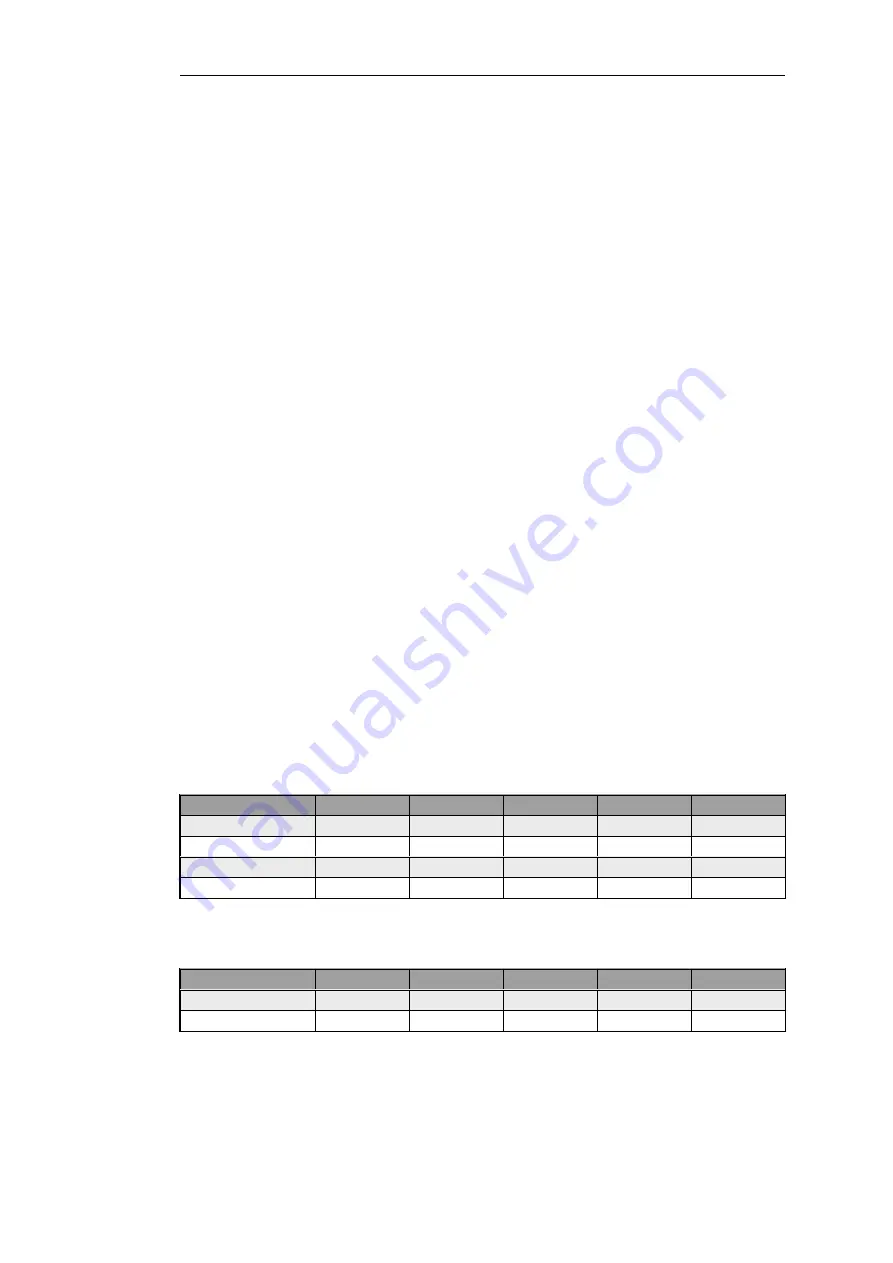
The IP rules/policies with
Record-Route
enabled are as shown below:
Action
Src Interface
Src Network
Dest Interface
Dest Network
OutboundToProxy
Allow
lan
lannet
dmz
ip_proxy
OutboundFromProxy
Allow
dmz
ip_proxy
lan
lannet
InboundFromProxy
Allow
dmz
ip_proxy
core
dmz_ip
InboundToProxy
Allow
wan
all-nets
dmz
ip_proxy
With
Record-Route
disabled, the following IP rules/policies must be added to those above:
Action
Src Interface
Src Network
Dest Interface
Dest Network
OutboundBypassProxy
Allow
lan
lannet
wan
all-nets
InboundBypassProxy
Allow
wan
all-nets
lan
lannet
Chapter 6: Security Mechanisms
478
Summary of Contents for NetDefendOS
Page 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Page 32: ...Chapter 1 NetDefendOS Overview 32 ...
Page 144: ...Chapter 2 Management and Maintenance 144 ...
Page 284: ...Chapter 3 Fundamentals 284 ...
Page 392: ...Chapter 4 Routing 392 ...
Page 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Page 420: ...Chapter 5 DHCP Services 420 ...
Page 573: ...Chapter 6 Security Mechanisms 573 ...
Page 607: ...Chapter 7 Address Translation 607 ...
Page 666: ...Chapter 8 User Authentication 666 ...
Page 775: ...Chapter 9 VPN 775 ...
Page 819: ...Chapter 10 Traffic Management 819 ...
Page 842: ...Chapter 11 High Availability 842 ...
Page 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Page 879: ...Chapter 13 Advanced Settings 879 ...






































