IP Rules and Policies for Outgoing Ping Messages
When the ICMP ping message is outgoing from NetDefendOS, it does not require any IP rules or
IP policies to allow the traffic since NetDefendOS is always trusted. In the NetDefendOS event
message logs, an outgoing ping will generate a
conn_open
and
conn_close
log event using the
Stock_Allow_All_Rule
. The source interface will always be the
core
interface (meaning
NetDefendOS itself ).
IP Rules and Policies for Incoming Ping Messages
Any ping messages that are incoming require an allowing IP rule or IP policy for NetDefendOS to
respond and these should have the associated
Service
object set to be the predefined service
ping-inbound
. An example IP rule for ping messages arriving on the
wan
interface would be the
following:
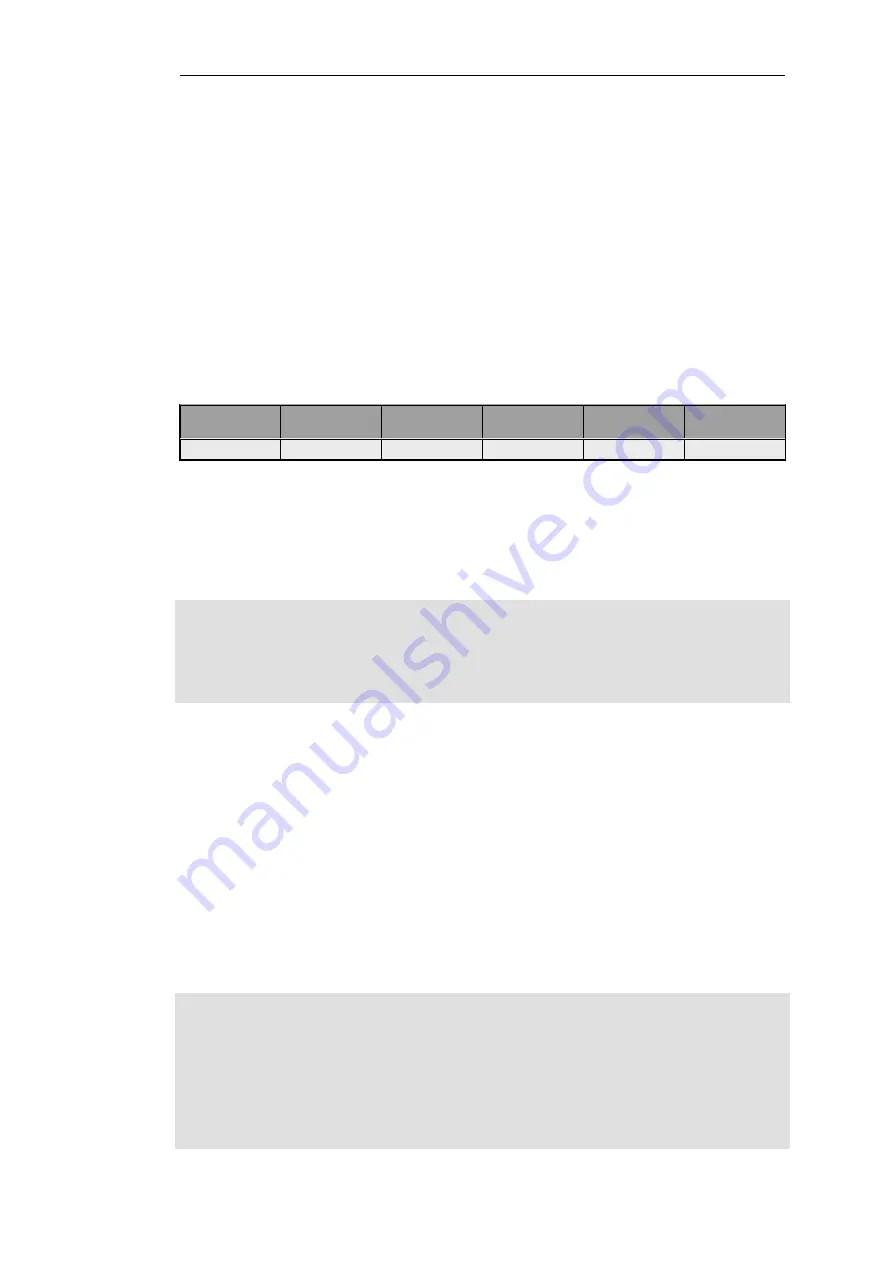
Action
Source
Interface
Source
Network
Destination
Interface
Destination
Network
Service
Allow
wan
all-nets
core
wan_ip
ping-inbound
Using the -verbose Option
The
-verbose
option is recommended to get the maximum amount of information from ping
usage. For example:
gw-world:/> ping 10.6.58.10 -verbose
Sending 1 4-byte ICMP ping to 10.6.58.10 from 192.168.3.20
... using route "192.168.3.20 via lan, gw (Iface IP)" in PBR table "main"
ICMP Reply from 192.168.3.20
seq=0
time=<10 ms
TTL=255
Ping Results:
Sent: 1, Received:1, Avg RTT: 10.0 ms
Here, the IPv4 address
192.168.3.20
is the IP address of the Ethernet interface on the firewall from
which the ping is sent. The output shows the route lookup that was performed to find the correct
interface.
When packet simulation is performed with the
-scrif
option (discussed later), the
-verbose
option
is required in order to show the rules that are triggered.
Testing TCP and UDP Connectivity
ICMP messages are neither UDP or TCP but are considered to be their own third category of IP
traffic. However, the NetDefendOS
ping
command has the ability to send a messages to test
either TCP or UDP connectivity.
To send as TCP, the
-port
option is used along with the
-tcp
option. Successful connectivity then
results in a 3-way TCP handshake taking place with the destination host. For example:
gw-world:/> ping 10.6.58.10 -port=80 -tcp -verbose
Sending 0-byte TCP ping to 10.6.58.10:80 from 192.168.3.20:41207
using PBR table "main"
... using route "10.6.10.0/24 via aux, no gw" in PBR table "main"
TCP Reply from 10.6.58.10:80 to 192.168.3.20:41207 seq=0
SYN+ACK
time=>10 ms
TTL=128
TCP Reply from 10.6.58.10:80 to 192.168.3.20:41207 seq=0
ACK
time=>10 ms
TTL=128
TCP Ping Results:
Sent: 1, RST/ACKs Received:1, Loss: 0%, Avg RTT: 10.0 ms
Chapter 2: Management and Maintenance
119
Summary of Contents for NetDefendOS
Page 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Page 32: ...Chapter 1 NetDefendOS Overview 32 ...
Page 144: ...Chapter 2 Management and Maintenance 144 ...
Page 284: ...Chapter 3 Fundamentals 284 ...
Page 392: ...Chapter 4 Routing 392 ...
Page 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Page 420: ...Chapter 5 DHCP Services 420 ...
Page 573: ...Chapter 6 Security Mechanisms 573 ...
Page 607: ...Chapter 7 Address Translation 607 ...
Page 666: ...Chapter 8 User Authentication 666 ...
Page 775: ...Chapter 9 VPN 775 ...
Page 819: ...Chapter 10 Traffic Management 819 ...
Page 842: ...Chapter 11 High Availability 842 ...
Page 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Page 879: ...Chapter 13 Advanced Settings 879 ...



































