•
When
all-nets
is the destination network, as is the case here, the advanced setting option
Add route statically must also be disabled. This setting is enabled by default.
5.
Define an PPTP/L2TP Server object (let's call this object
l2tp_tunnel
) with the following
parameters:
•
Set Inner IP Address to
lan_ip
.
•
Set Tunnel Protocol to
L2TP
.
•
Set Outer Interface Filter to
ipsec_tunnel
.
•
Set Outer Server IP to
wan_ip
.
•
Set the Microsoft Point-to-Point Encryption setting to
None
only. Since IPsec
encryption is already used, double encryption will degrade throughput.
•
Set IP Pool to
l2tp_pool
.
•
Enable Proxy ARP on the
lan
interface to which the internal network is connected.
•
Under the
Virtual Routing
tab, make this interface a member of a specific routing table so
that routes are automatically added to that table. Normally the
main
table should be
selected.
6.
For user authentication:
•
Define a Local User DB object (let's call this object
TrustedUsers
).
•
Add individual users to
TrustedUsers
. This should consist of at least a username and
password combination.
The Group string for a user can also be specified. This is explained in the same step in
the
IPsec Roaming Clients
section above.
•
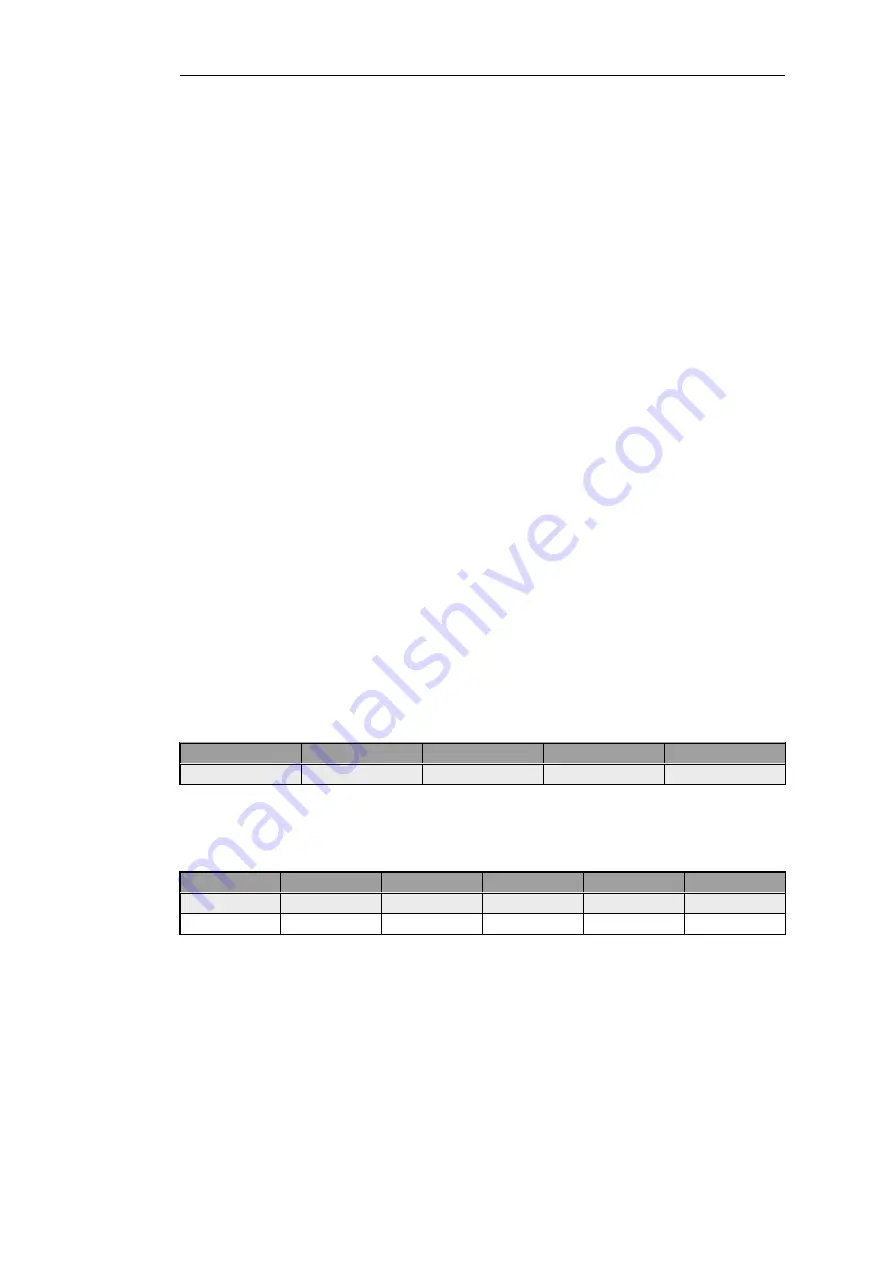
Define a User Authentication Rule:
Agent
Auth Source
Src Network
Interface
Client Source IP
PPP
Local
all-nets
l2tp_tunnel
all-nets (0.0.0.0/0)
7.
To allow traffic through the L2TP tunnel the following rules should be defined in the IP rule
set:
Action
Src Interface
Src Network
Dest Interface
Dest Network
Service
Allow
l2tp_tunnel
l2tp_pool
any
int_net
all_services
NAT
l2tp_tunnel
l2tp_pool
ext
all-nets
all_services
The second rule would be included to allow clients to surf the Internet via the
lan
interface on
the NetDefend Firewall. The client will be allocated a private internal IP address which must be
NATed if connections are then made out to the public Internet via the NetDefend Firewall.
8.
Set up the client. Assuming Windows XP, the Create new connection option in Network
Connections should be selected to start the
New Connection Wizard
. The key information to
enter in this wizard is the resolvable URL of the NetDefend Firewall or alternatively its
wan_ip
IP address.
Then choose Network > Properties. In the dialog that opens choose the L2TP Tunnel and
Chapter 9: VPN
679
Содержание NetDefendOS
Страница 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Страница 32: ...Chapter 1 NetDefendOS Overview 32 ...
Страница 144: ...Chapter 2 Management and Maintenance 144 ...
Страница 220: ... Enable DHCP passthrough Enable L2 passthrough for non IP protocols 4 Click OK Chapter 3 Fundamentals 220 ...
Страница 267: ... SourceNetwork lannet DestinationInterface any DestinationNetwork all nets 4 Click OK Chapter 3 Fundamentals 267 ...
Страница 284: ...Chapter 3 Fundamentals 284 ...
Страница 360: ...The ospf command options are fully described in the separate NetDefendOS CLI Reference Guide Chapter 4 Routing 360 ...
Страница 392: ...Chapter 4 Routing 392 ...
Страница 396: ...Web Interface 1 Go to Network Ethernet If1 2 Select Enable DHCP 3 Click OK Chapter 5 DHCP Services 396 ...
Страница 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Страница 420: ...Chapter 5 DHCP Services 420 ...
Страница 424: ...2 Now enter Name lan_Access Action Expect Interface lan Network lannet 3 Click OK Chapter 6 Security Mechanisms 424 ...
Страница 573: ...Chapter 6 Security Mechanisms 573 ...
Страница 575: ...This section describes and provides examples of configuring NAT and SAT rules Chapter 7 Address Translation 575 ...
Страница 607: ...Chapter 7 Address Translation 607 ...
Страница 666: ...Chapter 8 User Authentication 666 ...
Страница 775: ...Chapter 9 VPN 775 ...
Страница 819: ...Chapter 10 Traffic Management 819 ...
Страница 842: ...Chapter 11 High Availability 842 ...
Страница 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Страница 879: ...Chapter 13 Advanced Settings 879 ...






























