The NetDefend Firewall cannot act as the end-point in an MTU discovery message exchange.
NetDefendOS will only forward ICMP messages or generate messages indicating the acceptable
MTU of its own outgoing interface.
Path MTU discovery is always enabled by default for IPv6 on all NetDefendOS interfaces and will
not be discussed further in this section. For IPv4, it must be enabled as described next.
Enabling IPv4 MTU Discovery on a Service Object
MTU discovery is not enabled for IPv4 by default. Instead, it must be explicitly enabled on the
Service
object associated with the
IP Rule
or
IP Policy
object that allows the connection. This is
done by enabling the following two properties of the
Service
object:
•
Forward ICMP Errors
•
Enable IPv4 Path MTU Discovery
The second property can only be enabled after the first property is enabled. The IP rule or IP
policy with which the service is used can be of any type except a
FwdFast
rule.
MTU Discovery Processing
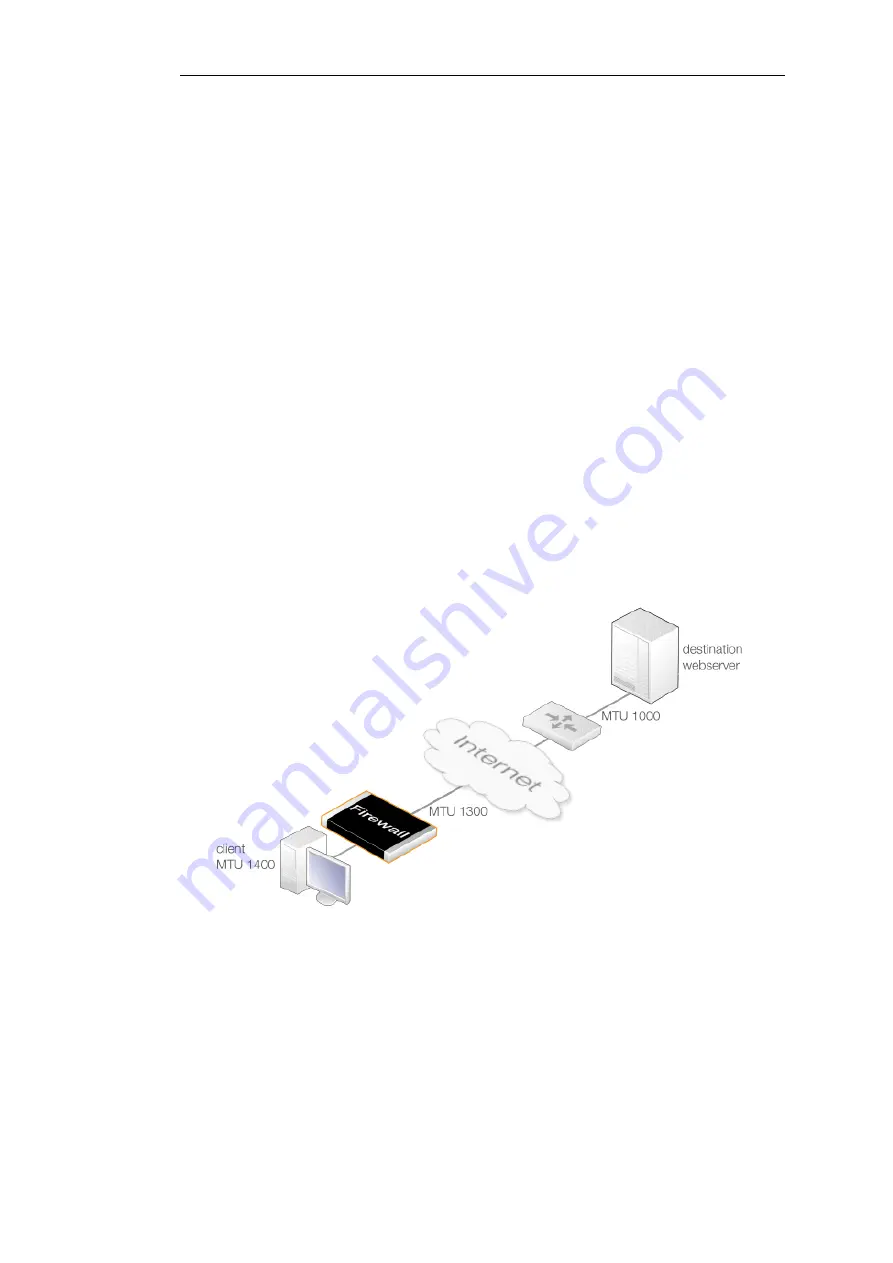
To illustrate a typical path MTU discovery message exchange, consider a client computer trying
to connect to a server via a NetDefend Firewall and the public Internet as well as a router. This is
shown in the diagram below.
Figure 3.1. Path MTU Discovery Processing
Assuming that MTU discovery has been enabled on the relevant NetDefendOS IP rule or IP policy,
the following sequence of events shows how MTU discovery would function:
1.
The client tries to open a connection to the server via the firewall using a packet size of 1400
bytes. The packets sent have the DF (Don't Fragment) flag enabled.
2.
NetDefendOS looks at the MTU property value for the interface object used for the next
hop. This is 1300 so the client's packet MTU is too high and fragmentation cannot be
performed.
Chapter 3: Fundamentals
175
Содержание NetDefendOS
Страница 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Страница 32: ...Chapter 1 NetDefendOS Overview 32 ...
Страница 144: ...Chapter 2 Management and Maintenance 144 ...
Страница 220: ... Enable DHCP passthrough Enable L2 passthrough for non IP protocols 4 Click OK Chapter 3 Fundamentals 220 ...
Страница 267: ... SourceNetwork lannet DestinationInterface any DestinationNetwork all nets 4 Click OK Chapter 3 Fundamentals 267 ...
Страница 284: ...Chapter 3 Fundamentals 284 ...
Страница 360: ...The ospf command options are fully described in the separate NetDefendOS CLI Reference Guide Chapter 4 Routing 360 ...
Страница 392: ...Chapter 4 Routing 392 ...
Страница 396: ...Web Interface 1 Go to Network Ethernet If1 2 Select Enable DHCP 3 Click OK Chapter 5 DHCP Services 396 ...
Страница 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Страница 420: ...Chapter 5 DHCP Services 420 ...
Страница 424: ...2 Now enter Name lan_Access Action Expect Interface lan Network lannet 3 Click OK Chapter 6 Security Mechanisms 424 ...
Страница 573: ...Chapter 6 Security Mechanisms 573 ...
Страница 575: ...This section describes and provides examples of configuring NAT and SAT rules Chapter 7 Address Translation 575 ...
Страница 607: ...Chapter 7 Address Translation 607 ...
Страница 666: ...Chapter 8 User Authentication 666 ...
Страница 775: ...Chapter 9 VPN 775 ...
Страница 819: ...Chapter 10 Traffic Management 819 ...
Страница 842: ...Chapter 11 High Availability 842 ...
Страница 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Страница 879: ...Chapter 13 Advanced Settings 879 ...
































