603
Configuring QoS
Configuring QoS
To delete an access list, use the
no access-list
access-list-number
global configuration command.
This example shows how to allow access for only those hosts on the three specified networks. The wildcard bits apply
to the host portions of the network addresses.
Switch(config)#
access-list 1 permit 192.5.255.0 0.0.0.255
Switch(config)#
access-list 1 permit 128.88.0.0 0.0.255.255
Switch(config)#
access-list 1 permit 36.0.0.0 0.0.0.255
Creating IP Extended ACLs
Beginning in privileged EXEC mode, follow these steps to create an IP extended ACL for IP traffic:
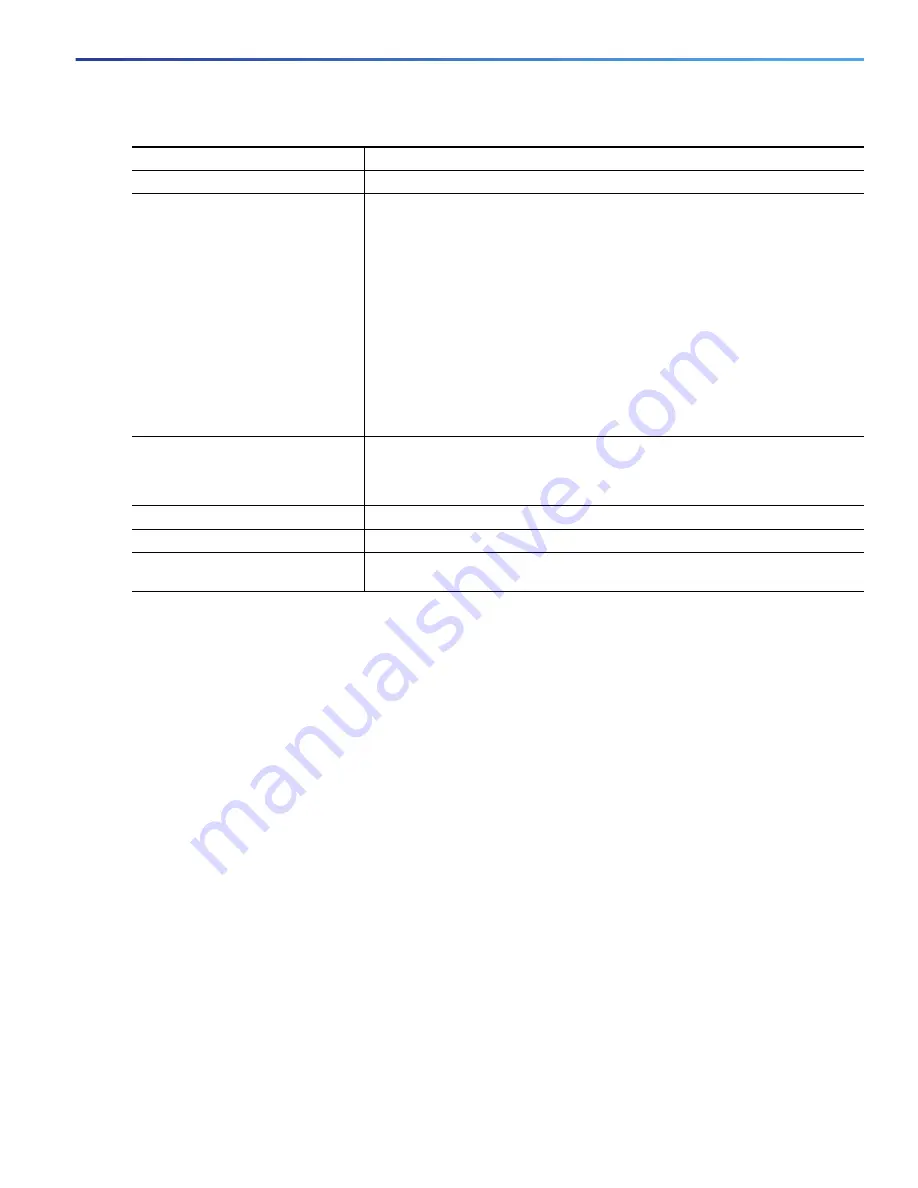
Command
Purpose
1.
configure terminal
Enter global configuration mode.
2.
access-list
access-list-number
permit
source
[
source-wildcard
]
Create an IP standard ACL, repeating the command as many times as
necessary.
For
access-list-number
, enter the access list number. The range is 1 to 99
and 1300 to 1999.
Always use the
permit
keyword for ACLs used as match criteria in QoS
policies. QoS policies do not match ACLs that use the
deny
keyword.
For
source
, enter the network or host from which the packet is being sent.
You can use the
any
keyword as an abbreviation for 0.0.0.0
255.255.255.255.
(Optional) For
source-wildcard
, enter the wildcard bits in dotted decimal
notation to be applied to the source.
or
ip access-list standard
name
Define a standard IPv4 access list using a name, and enter access-list
configuration mode. The name can be a number from 1 to 99.
In access-list configuration mode, enter
permit
source
[
source-wildcard
]
3.
end
Return to privileged EXEC mode.
4.
show access-lists
Verify your entries.
5.
copy running-config
startup-config
(Optional) Save your entries in the configuration file.
Summary of Contents for IE 4000
Page 12: ...8 Configuration Overview Default Settings After Initial Switch Configuration ...
Page 52: ...48 Configuring Interfaces Monitoring and Maintaining the Interfaces ...
Page 108: ...104 Configuring Switch Clusters Additional References ...
Page 128: ...124 Performing Switch Administration Additional References ...
Page 130: ...126 Configuring PTP ...
Page 140: ...136 Configuring CIP Additional References ...
Page 146: ...142 Configuring SDM Templates Configuration Examples for Configuring SDM Templates ...
Page 192: ...188 Configuring Switch Based Authentication Additional References ...
Page 244: ...240 Configuring IEEE 802 1x Port Based Authentication Additional References ...
Page 298: ...294 Configuring VLANs Additional References ...
Page 336: ...332 Configuring STP Additional References ...
Page 408: ...404 Configuring DHCP Additional References ...
Page 450: ...446 Configuring IGMP Snooping and MVR Additional References ...
Page 490: ...486 Configuring SPAN and RSPAN Additional References ...
Page 502: ...498 Configuring Layer 2 NAT ...
Page 770: ...766 Configuring IPv6 MLD Snooping Related Documents ...
Page 930: ...926 Configuring IP Unicast Routing Related Documents ...
Page 976: ...972 Configuring Cisco IOS IP SLAs Operations Additional References ...
Page 978: ...974 Dying Gasp ...
Page 990: ...986 Configuring Enhanced Object Tracking Monitoring Enhanced Object Tracking ...
Page 994: ...990 Configuring MODBUS TCP Displaying MODBUS TCP Information ...
Page 996: ...992 Ethernet CFM ...
Page 1066: ...1062 Using an SD Card SD Card Alarms ...






























