694
Field descriptions
Assets field descriptions
Network Users
All authentication systems require that you define and store the information necessary to authenticate
a user. This normally includes a user name to identify the user and a password, key, or hash to validate
the user’s identity. When using the security gateway’s internal authentication server, alone or in an
authentication scheme, you must first define authentication information.
User Account Properties—General tab
User accounts specify the types of authentication that apply to users when they attempt to connect to
the security gateway.
Associated tasks
The task that you can perform with this tab is:
■
“Configuring users for internal authentication”
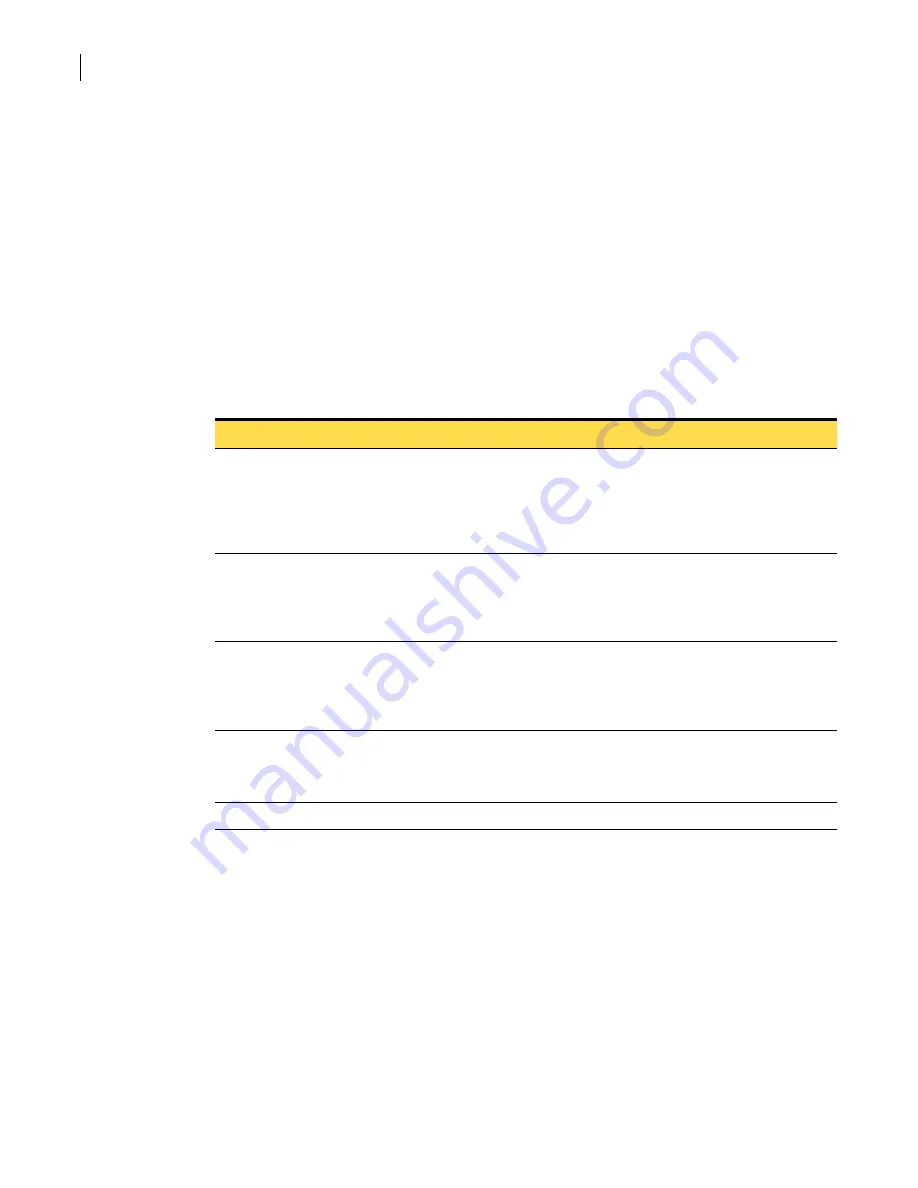
Table D-149
User Account Properties—General tab
Field
Description
User name
A unique name for the user.
The maximum length is 256 characters.
Allowed characters include a-z, A-Z, numerals, periods (.), dashes (-), and underscores (_). Do
not include spaces in the name. The characters @,!,#,$,%,^,&,*,<,> and other reserved
characters are also invalid.
First name
The user’s first name.
In the table on the User Accounts tab, the first name is shown as the given name.
The maximum length is 256 characters and can include any alphanumeric characters,
including spaces.
Last name
The user’s last name.
In the table on the User Accounts tab, the last name is shown as the surname.
The maximum length is 256 characters and can include any alphanumeric characters,
including spaces.
Caption
An optional, brief description of the user.
The maximum is 128 characters.
For longer descriptions, use the Description tab.
UserID
System-generated user ID for this user. This field is read-only.
Summary of Contents for Security 5600 Series, Security 5400 Series,Clientless VPN 4400 Series
Page 76: ...76 Managing administrative access Enabling SSH for command line access to the appliance...
Page 242: ...242 Defining your security environment Controlling full application inspection of traffic...
Page 243: ...243 Defining your security environment Controlling full application inspection of traffic...
Page 269: ...268 Limiting user access Authenticating using Out Of Band Authentication OOBA...
Page 373: ...372 Preventing attacks Enabling protection for logical network interfaces...
Page 509: ...508 Generating reports Upgrade reports...
Page 553: ...552 Advanced system settings Configuring advanced options...
Page 557: ...556 SSL server certificate management Installing a signed certificate...
Page 861: ...860 Index...






























