96
c.
Click
Add
.
d.
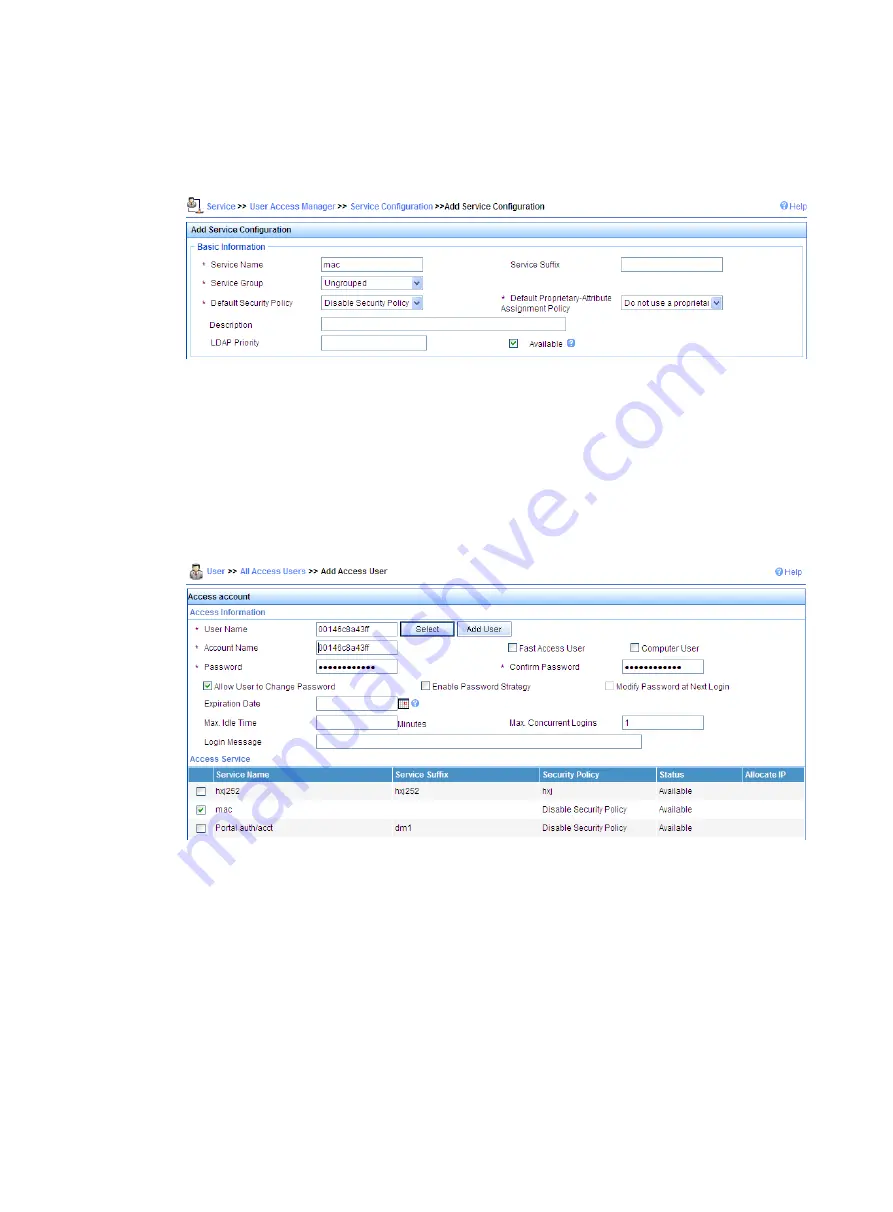
On the page that appears, set the service name as
mac
, keep the default values for other
parameters, and click
OK
.
Figure 79
Adding a service
3.
Add an account:
a.
Click the
User
tab.
b.
Select
User
>
All Access Users
from the navigation tree.
c.
Click
Add
.
d.
On the page that appears, enter username
00146c8a43ff
, set the account name and
password both as
00146c8a43ff
, select the service
mac
, and click
OK
.
Figure 80
Adding an account
Verifying the configuration
During authentication, the user does not need to input the username or password. After passing MAC
authentication, the client can associate with the device and access the WLAN. You can view the online
clients by selecting
Interface Setup
>
Wireless
>
Summary
from the navigation tree and then clicking the
Client
tab.
Remote 802.1X authentication configuration example
Network requirements
Use IMC as a RADIUS server for AAA. On the RADIUS server, configure the client’s username as
user
,
password as
dot1x
, and shared key as
expert
. The IP address of the RADIUS server is 10.18.1.88.
Содержание MSR SERIES
Страница 17: ...xv Documents 835 Websites 835 Conventions 836 Index 838 ...
Страница 20: ...3 Figure 3 Initial page of the Web interface ...
Страница 42: ...25 Figure 13 Firefox Web browser setting ...
Страница 59: ...42 Figure 27 Checking the basic service configuration ...
Страница 73: ...56 Figure 35 Sample interface statistics ...
Страница 156: ...139 Figure 139 Rebooting the 3G modem ...
Страница 168: ...151 Figure 152 Configuring Web server 2 ...
Страница 174: ...157 Figure 158 Configure the URL filtering function ...
Страница 187: ...170 Upon detecting the Land or Smurf attack on Ethernet 0 2 Router outputs an alarm log and drops the attack packet ...
Страница 242: ...225 Figure 233 Enabling the DHCP client on interface Ethernet 0 1 ...
Страница 247: ...230 Figure 236 The page for configuring an advanced IPv4 ACL ...
Страница 255: ...238 Figure 241 Advanced limit setting ...
Страница 298: ...281 e Click Apply 2 Configure Router B in the same way Router A is configured ...
Страница 354: ...337 Figure 339 Configuring a login control rule so Host B cannot access Router through the Web ...
Страница 400: ...383 Figure 387 Verifying the configuration ...
Страница 405: ...388 ...
Страница 523: ...506 Figure 530 Ping configuration page ...
Страница 538: ...521 a Click Device A on the topology diagram b Click Ethernet 0 2 on the panel diagram c Click Port Guard ...
Страница 744: ...727 Verifying the configuration In the case that the IP network is unavailable calls can be made over PSTN ...
Страница 775: ...758 Figure 785 Configuring a jump node ...
Страница 791: ...774 Figure 801 Configuring a jump node ...
















































