Chapter 8 The Wi-Fi Configuration Screens
User’s Guide
105
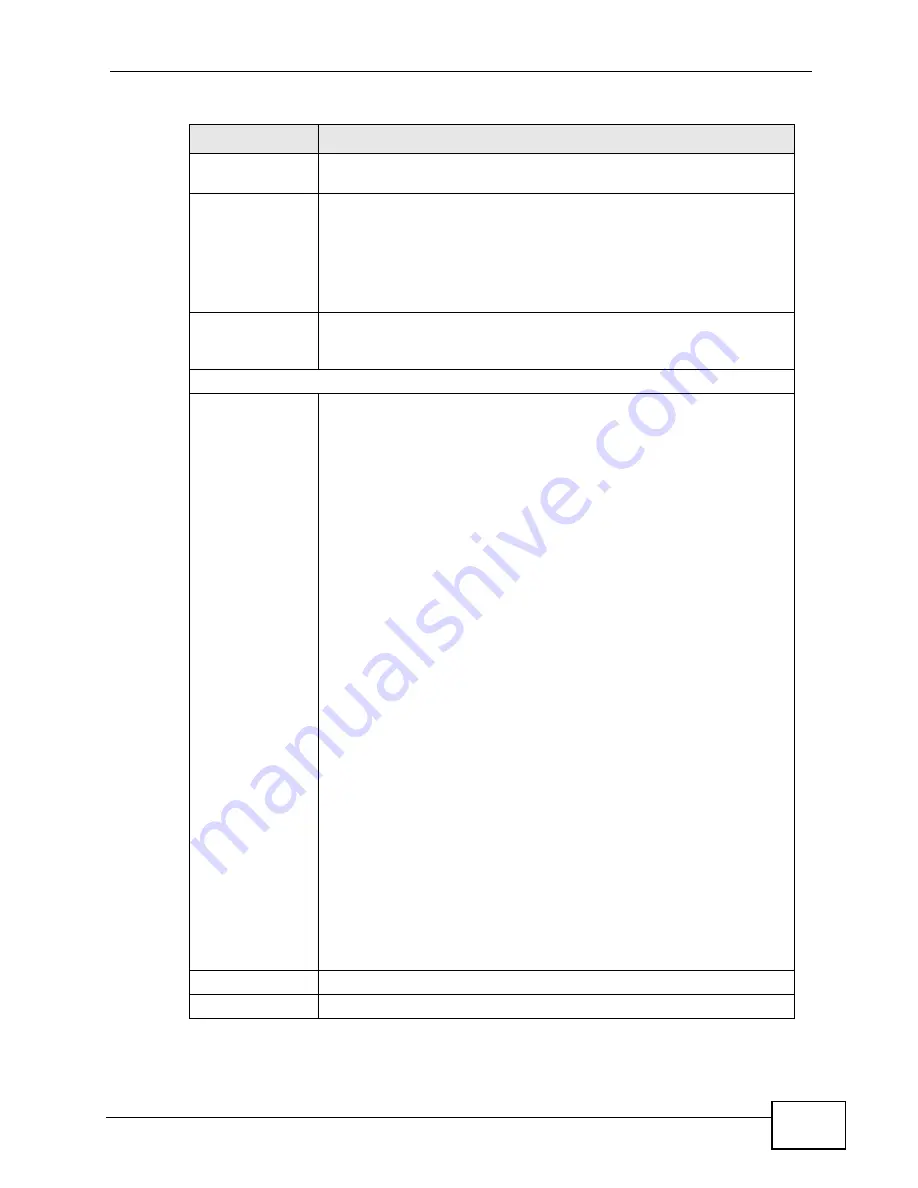
Name (SSID)
Enter the SSID name that the wireless network signal will be listed
as on compatible Wi-Fi clients.
Hide SSID
Select this option to mask your Wi-Fi network signal. While this may
“hide” it from casual scanning programs and devices, it cannot truly
hide it from dedicated signal sniffers.
If you know the SSID, however, you can still connect to it when
prompted to enter an SSID either by your operating system’s
connection mechanism or the Wi-Fi software you use.
Channel
Selection
Select a channel on which to broadcast your Wi-Fi network signal.
Ideally, you should choose a channel that is currently not in use by
other devices within range of this one.
Security
Security Mode
Select a security encryption protocol to protect your Wi-Fi network
from unwanted visitors. The options are:
Security Options are:
• No Security - It is not recommended that you use this setting.
With no security, anyone who has a Wi-Fi device can connect to
your network.
• Static WEP - This is a basic form of encryption. It is not
recommended that you use it as it can be by-passed quite easily.
However, because it is one of the original Wi-Fi encryption
methods, it is the most compatible with older devices. Select this
option if you require maximum compatibility.
• WPA-PSK - This provides both improved data encryption and
user authentication. Using PSK, both the WiMAX Device and the
connecting client share a common password in order to validate
the connection. This type of encryption, while robust, is not as
strong as WPA, WPA2 or even WPA2-PSK. Use this type of
security of you do not use a RADIUS server to authenticate user
credentials.
• WPA - This is a security subset of WPA2. It requires the
presence of a RADIUS server on your network in order to validate
user credentials. This encryption standard is slightly older than
WPA2 and therefore is more compatible with older devices.
• WPA2-PSK - This is a newer, more robust version of the WPA
encryption standard. It offers slightly better security, although
the use of PSK makes it less robust than it could be. Use this
option if you do not have RADIUS server on your network to
verify user credentials.
• WPA2 - This is currently the most robust form of encryption for
wireless networks. It requires a RADIUS server to authenticate
user credentials and is a full implementation the security
protocol. Use this security option for maximum protection of your
network. However, it is the least backwards compatible with
older devices.
The option you select here changes the configuration options on this
screen accordingly. For details on the specific security options, see
subsequent tables.
Apply
Click to save your changes.
Reset
Click to restore your previously saved settings.
Table 32
ADVANCED > Wi-Fi Configuration > General (continued)
LABEL
DESCRIPTION
Summary of Contents for MAX-306
Page 2: ......
Page 8: ...Safety Warnings User s Guide 8...
Page 10: ...Contents Overview User s Guide 10...
Page 30: ...30...
Page 36: ...Chapter 1 Getting Started User s Guide 36...
Page 46: ...Chapter 2 Introducing the Web Configurator User s Guide 46...
Page 64: ...Chapter 4 VoIP Connection Wizard User s Guide 64...
Page 65: ...65 PART II Basic Screens The Main Screen 40 The Setup Screens 67...
Page 66: ...66...
Page 74: ...74...
Page 88: ...Chapter 6 The LAN Configuration Screens User s Guide 88...
Page 112: ...Chapter 8 The Wi Fi Configuration Screens User s Guide 112...
Page 134: ...Chapter 10 The NAT Configuration Screens User s Guide 134...
Page 146: ...146...
Page 164: ...Chapter 12 The Service Configuration Screens User s Guide 164...
Page 180: ...Chapter 14 The Phone Book Screens User s Guide 180...
Page 182: ...182...
Page 202: ...Chapter 15 The Certificates Screens User s Guide 202...
Page 212: ...Chapter 16 The Firewall Screens User s Guide 212...
Page 226: ...Chapter 18 The Remote Management Screens User s Guide 226...
Page 242: ...Chapter 19 The Logs Screens User s Guide 242...
Page 252: ...Chapter 20 The UPnP Screen User s Guide 252...
Page 265: ...265 PART VI Troubleshooting and Specifications Troubleshooting 267 Product Specifications 275...
Page 266: ...266...
Page 274: ...Chapter 22 Troubleshooting User s Guide 274...
Page 278: ...278...
Page 310: ...Appendix B Setting Up Your Computer s IP Address User s Guide 310...
Page 336: ...Appendix D Pop up Windows JavaScripts and Java Permissions User s Guide 336...
Page 380: ...Appendix F Importing Certificates User s Guide 380...
Page 382: ...Appendix G SIP Passthrough User s Guide 382...
Page 398: ...Appendix J Customer Support User s Guide 398...
Page 405: ...Index User s Guide 405...






























