Chapter 15 Certificates
P-2802H(W)(L)-I Series User’s Guide
226
15.11 Trusted Remote Hosts
Click
Security > Certificates > Trusted Remote Hosts
to open the
Trusted Remote Hosts
screen. This screen displays a list of the certificates of peers that you trust but which are not
signed by one of the certification authorities on the
Trusted CAs
screen.
You do not need to add any certificate that is signed by one of the certification authorities on
the
Trusted CAs
screen since the ZyXEL Device automatically accepts any valid certificate
signed by a trusted certification authority as being trustworthy.
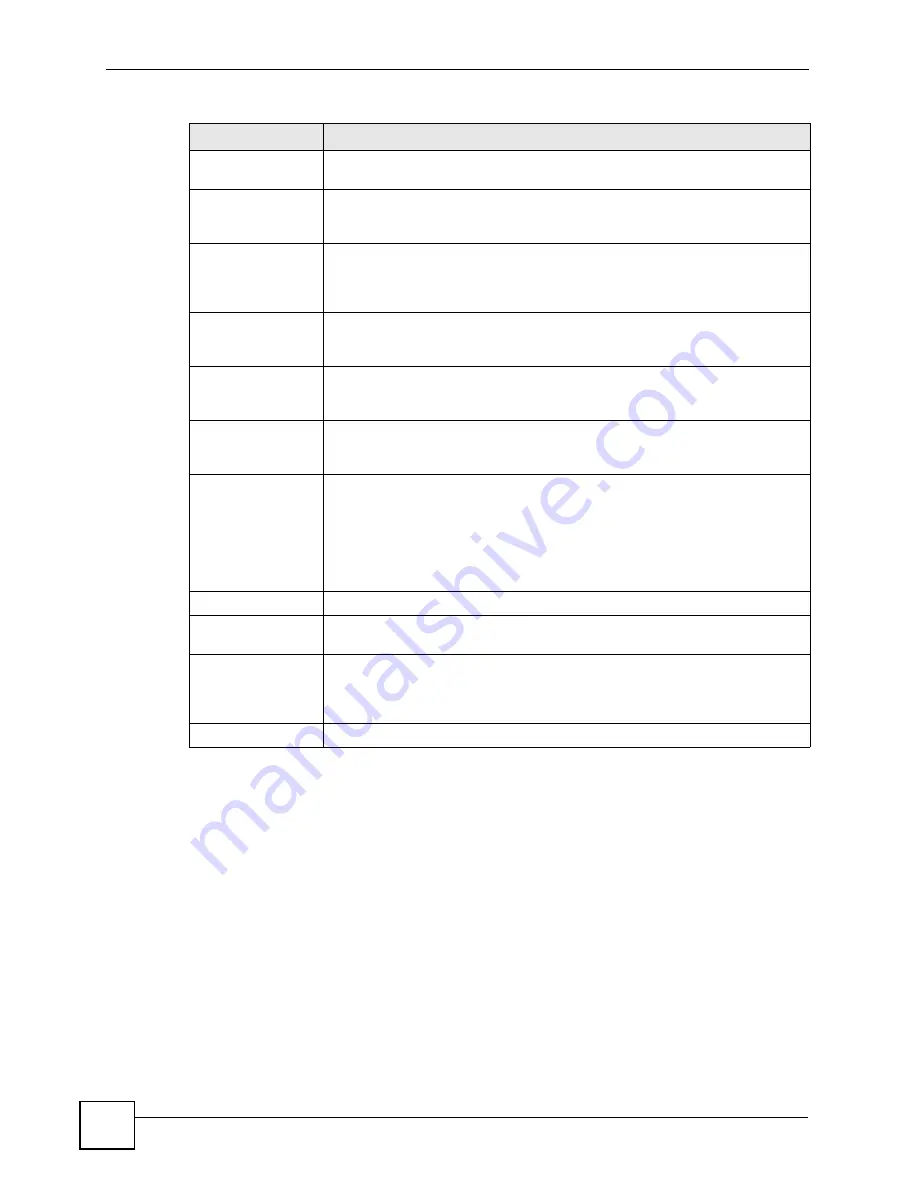
Subject Alternative
Name
This field displays the certificate’s owner‘s IP address (IP), domain name (DNS)
or e-mail address (EMAIL).
Key Usage
This field displays for what functions the certificate’s key can be used. For
example, “DigitalSignature” means that the key can be used to sign certificates
and “KeyEncipherment” means that the key can be used to encrypt text.
Basic Constraint
This field displays general information about the certificate. For example,
Subject Type=CA means that this is a certification authority’s certificate and
“Path Length Constraint=1” means that there can only be one certification
authority in the certificate’s path.
CRL Distribution
Points
This field displays how many directory servers with Lists of revoked certificates
the issuing certification authority of this certificate makes available. This field
also displays the domain names or IP addresses of the servers.
MD5 Fingerprint
This is the certificate’s message digest that the ZyXEL Device calculated using
the MD5 algorithm. You can use this value to verify with the certification
authority (over the phone for example) that this is actually their certificate.
SHA1 Fingerprint
This is the certificate’s message digest that the ZyXEL Device calculated using
the SHA1 algorithm. You can use this value to verify with the certification
authority (over the phone for example) that this is actually their certificate.
Certificate in PEM
(Base-64) Encoded
Format
This read-only text box displays the certificate or certification request in Privacy
Enhanced Mail (PEM) format. PEM uses 64 ASCII characters to convert the
binary certificate into a printable form.
You can copy and paste the certificate into an e-mail to send to friends or
colleagues or you can copy and paste the certificate into a text editor and save
the file on a management computer for later distribution (via floppy disk for
example).
Back
Click
Back
to return to the previous screen.
Export
Click this button and then
Save
in the
File Download
screen. The
Save As
screen opens, browse to the location that you want to use and click
Save
.
Apply
Click
Apply
to save your changes back to the ZyXEL Device. You can only
change the name and/or set whether or not you want the ZyXEL Device to
check the CRL that the certification authority issues before trusting a certificate
issued by the certification authority.
Cancel
Click
Cancel
to quit and return to the
Trusted CAs
screen.
Table 90
Trusted CA Details (continued)
LABEL
DESCRIPTION
Summary of Contents for P-2802H-I Series
Page 1: ...www zyxel com P 2802H W L I Series VDSL VoIP IAD User s Guide Version 3 70 6 2007 Edition 1...
Page 2: ......
Page 7: ...Safety Warnings P 2802H W L I Series User s Guide 7...
Page 8: ...Safety Warnings P 2802H W L I Series User s Guide 8...
Page 10: ...Contents Overview P 2802H W L I Series User s Guide 10...
Page 32: ...List of Tables P 2802H W L I Series User s Guide 32...
Page 33: ...33 PART I Introduction Introducing the ZyXEL Device 35 Introducing the Web Configurator 43...
Page 34: ...34...
Page 50: ...Chapter 2 Introducing the Web Configurator P 2802H W L I Series User s Guide 50...
Page 51: ...51 PART II Wizard Internet and Wireless Setup Wizard 53 VoIP Wizard And Example 65...
Page 52: ...52...
Page 64: ...Chapter 3 Internet and Wireless Setup Wizard P 2802H W L I Series User s Guide 64...
Page 70: ...Chapter 4 VoIP Wizard And Example P 2802H W L I Series User s Guide 70...
Page 72: ...72...
Page 82: ...Chapter 5 Status Screens P 2802H W L I Series User s Guide 82...
Page 88: ...Chapter 6 WAN Setup P 2802H W L I Series User s Guide 88...
Page 116: ...Chapter 8 Wireless LAN P 2802H W L I Series User s Guide 116...
Page 154: ...Chapter 10 Voice P 2802H W L I Series User s Guide 154...
Page 174: ...Chapter 11 Firewalls P 2802H W L I Series User s Guide 174...
Page 178: ...Chapter 12 Content Filtering P 2802H W L I Series User s Guide 178...
Page 184: ...Chapter 13 Introduction to IPSec P 2802H W L I Series User s Guide 184...
Page 238: ...Chapter 16 Static Route P 2802H W L I Series User s Guide 238...
Page 250: ...Chapter 17 Quality of Service QoS P 2802H W L I Series User s Guide 250...
Page 254: ...Chapter 18 Dynamic DNS Setup P 2802H W L I Series User s Guide 254...
Page 282: ...Chapter 20 Universal Plug and Play UPnP P 2802H W L I Series User s Guide 282...
Page 284: ...284...
Page 324: ...Chapter 25 Troubleshooting P 2802H W L I Series User s Guide 324...
Page 334: ...Chapter 26 Product Specifications P 2802H W L I Series User s Guide 334...
Page 336: ...336...
Page 348: ...Appendix A Setting up Your Computer s IP Address P 2802H W L I Series User s Guide 348...
Page 404: ...Appendix G Legal Information P 2802H W L I Series User s Guide 404...
Page 410: ...Appendix H Customer Support P 2802H W L I Series User s Guide 410...






























