Chapter 8 Wireless LAN
P-2802H(W)(L)-I Series User’s Guide
103
Unauthorized wireless devices can still see the information that is sent in the wireless network,
even if they cannot use the wireless network. Furthermore, there are ways for unauthorized
wireless users to get a valid user name and password. Then, they can use that user name and
password to use the wireless network.
8.2.4 Encryption
Wireless networks can use encryption to protect the information that is sent in the wireless
network. Encryption is like a secret code. If you do not know the secret code, you cannot
understand the message.
The types of encryption you can choose depend on the type of authentication. (See
for information about this.)
For example, if the wireless network has a RADIUS server, you can choose
WPA
or
WPA2
. If
users do not log in to the wireless network, you can choose no encryption,
Static WEP
,
WPA-
PSK
, or
WPA2-PSK
.
Usually, you should set up the strongest encryption that every device in the wireless network
supports. For example, suppose you have a wireless network with the ZyXEL Device and you
do not have a RADIUS server. Therefore, there is no authentication. Suppose the wireless
network has two devices. Device A only supports WEP, and device B supports WEP and
WPA. Therefore, you should set up
Static WEP
in the wireless network.
"
It is recommended that wireless networks use
WPA-PSK
,
WPA
, or stronger
encryption. The other types of encryption are better than none at all, but it is
still possible for unauthorized wireless devices to figure out the original
information pretty quickly.
When you select
WPA2
or
WPA2-PSK
in your ZyXEL Device, you can also select an option
(
WPA compatible
) to support WPA as well. In this case, if some of the devices support WPA
and some support WPA2, you should set up
WPA2-PSK
or
WPA2
(depending on the type of
wireless network login) and select the
WPA compatible
option in the ZyXEL Device.
Many types of encryption use a key to protect the information in the wireless network. The
longer the key, the stronger the encryption. Every device in the wireless network must have the
same key.
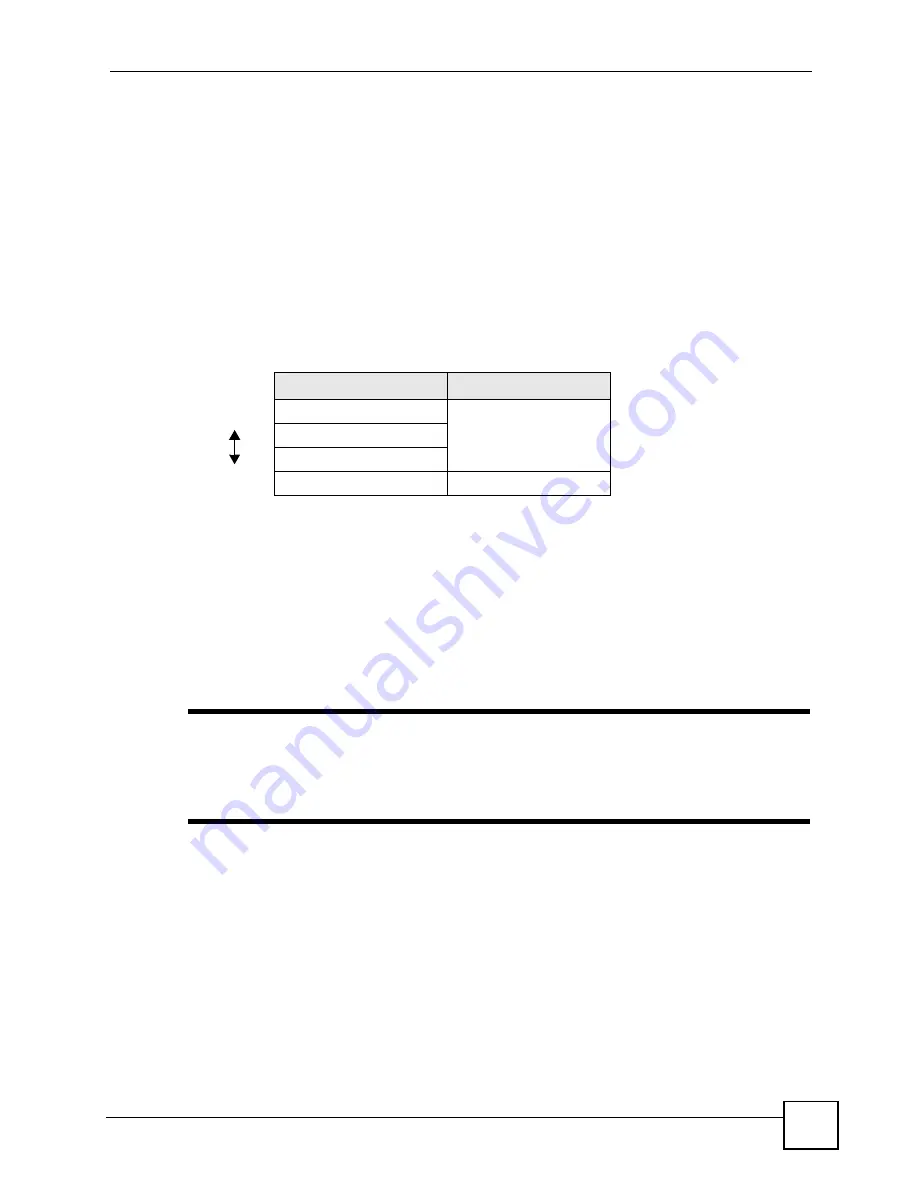
Table 28
Types of Encryption for Each Type of Authentication
NO AUTHENTICATION
RADIUS SERVER
Weakest
No Security
WPA
Static WEP
WPA-PSK
Strongest
WPA2-PSK
WPA2
Summary of Contents for P-2802H-I Series
Page 1: ...www zyxel com P 2802H W L I Series VDSL VoIP IAD User s Guide Version 3 70 6 2007 Edition 1...
Page 2: ......
Page 7: ...Safety Warnings P 2802H W L I Series User s Guide 7...
Page 8: ...Safety Warnings P 2802H W L I Series User s Guide 8...
Page 10: ...Contents Overview P 2802H W L I Series User s Guide 10...
Page 32: ...List of Tables P 2802H W L I Series User s Guide 32...
Page 33: ...33 PART I Introduction Introducing the ZyXEL Device 35 Introducing the Web Configurator 43...
Page 34: ...34...
Page 50: ...Chapter 2 Introducing the Web Configurator P 2802H W L I Series User s Guide 50...
Page 51: ...51 PART II Wizard Internet and Wireless Setup Wizard 53 VoIP Wizard And Example 65...
Page 52: ...52...
Page 64: ...Chapter 3 Internet and Wireless Setup Wizard P 2802H W L I Series User s Guide 64...
Page 70: ...Chapter 4 VoIP Wizard And Example P 2802H W L I Series User s Guide 70...
Page 72: ...72...
Page 82: ...Chapter 5 Status Screens P 2802H W L I Series User s Guide 82...
Page 88: ...Chapter 6 WAN Setup P 2802H W L I Series User s Guide 88...
Page 116: ...Chapter 8 Wireless LAN P 2802H W L I Series User s Guide 116...
Page 154: ...Chapter 10 Voice P 2802H W L I Series User s Guide 154...
Page 174: ...Chapter 11 Firewalls P 2802H W L I Series User s Guide 174...
Page 178: ...Chapter 12 Content Filtering P 2802H W L I Series User s Guide 178...
Page 184: ...Chapter 13 Introduction to IPSec P 2802H W L I Series User s Guide 184...
Page 238: ...Chapter 16 Static Route P 2802H W L I Series User s Guide 238...
Page 250: ...Chapter 17 Quality of Service QoS P 2802H W L I Series User s Guide 250...
Page 254: ...Chapter 18 Dynamic DNS Setup P 2802H W L I Series User s Guide 254...
Page 282: ...Chapter 20 Universal Plug and Play UPnP P 2802H W L I Series User s Guide 282...
Page 284: ...284...
Page 324: ...Chapter 25 Troubleshooting P 2802H W L I Series User s Guide 324...
Page 334: ...Chapter 26 Product Specifications P 2802H W L I Series User s Guide 334...
Page 336: ...336...
Page 348: ...Appendix A Setting up Your Computer s IP Address P 2802H W L I Series User s Guide 348...
Page 404: ...Appendix G Legal Information P 2802H W L I Series User s Guide 404...
Page 410: ...Appendix H Customer Support P 2802H W L I Series User s Guide 410...






























