1-19
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring AAA Servers and the Local Database
Configuring AAA
To set up VPN user authorization using LDAP, perform the following steps.
Detailed Steps
Examples
While there are other authorization-related commands and options available for specific requirements,
the following example shows commands for enabling user authorization with LDAP. The example then
creates an IPsec remote access tunnel group named remote-1, and assigns that new tunnel group to the
previously created ldap_dir_1 AAA server group for authorization:
hostname(config)#
tunnel-group remote-1 type ipsec-ra
hostname(config)#
tunnel-group remote-1 general-attributes
hostname(config-general)#
authorization-server-group ldap_dir_1
hostname(config-general)#
After you complete this configuration work, you can then configure additional LDAP authorization
parameters such as a directory password, a starting point for searching a directory, and the scope of a
directory search by entering the following commands:
hostname(config)#
aaa-server ldap_dir_1 protocol ldap
hostname(config-aaa-server-group)#
aaa-server ldap_dir_1 host 10.1.1.4
hostname(config-aaa-server-host)#
ldap-login-dn obscurepassword
hostname(config-aaa-server-host)#
ldap-base-dn starthere
hostname(config-aaa-server-host)#
ldap-scope subtree
hostname(config-aaa-server-host)#
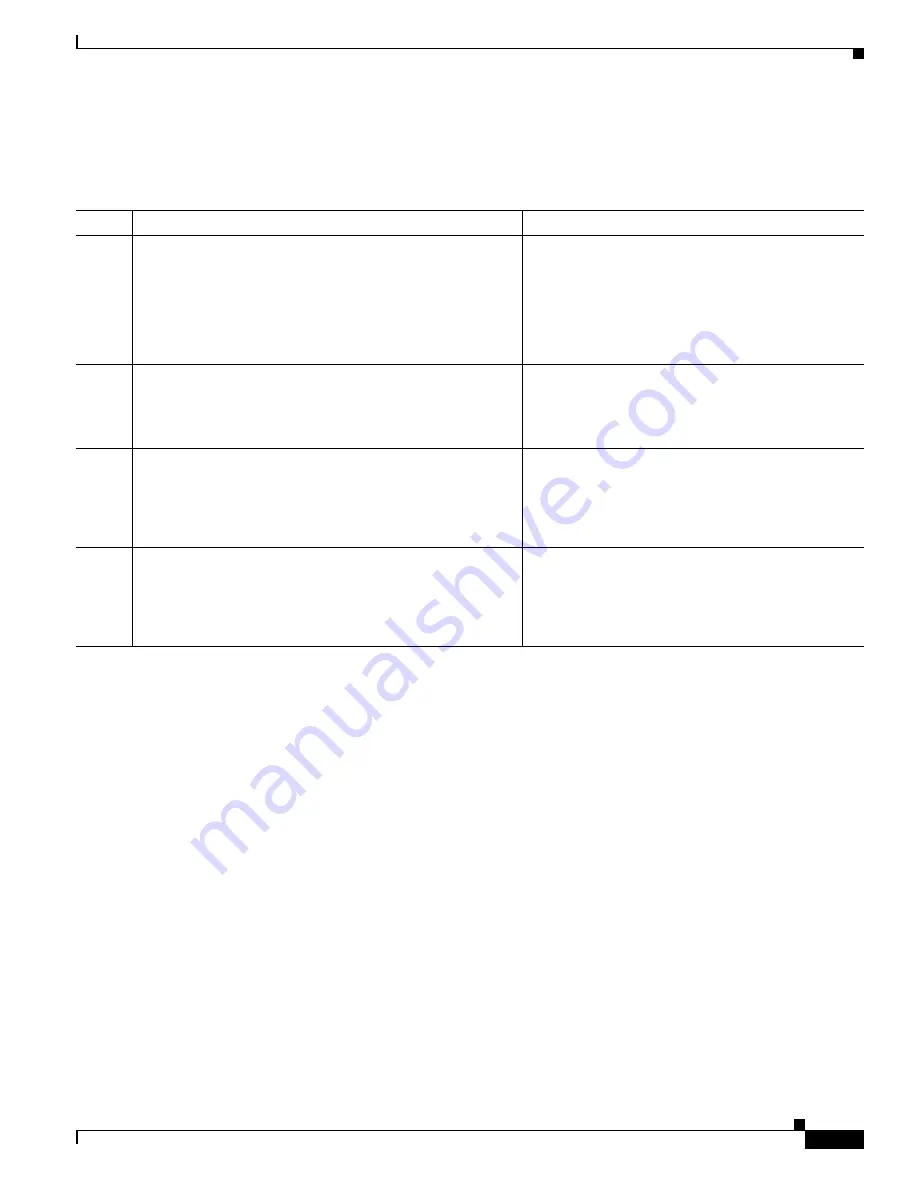
Command
Purpose
Step 1
aaa-server
server_group
protocol
{
kerberos
|
ldap
|
nt
|
radius
|
sdi
|
}
Example:
hostname(config)#
aaa-server servergroup1 protocol
ldap
hostname(config-aaa-server-group)
Creates a AAA server group.
Step 2
tunnel-group
groupname
Example:
hostname(config)#
tunnel-group remotegrp
Creates an IPsec remote access tunnel group named
remotegrp.
Step 3
tunnel-group
groupname
general-attributes
Example:
hostname(config)#
tunnel-group remotegrp
general-attributes
Associates the server group and the tunnel group.
Step 4
authorization-server-group
group-tag
Example:
hostname(config-general)# authorization-server-group
ldap_dir_1
Assigns a new tunnel group to a previously created
AAA server group for authorization.
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......






























