1-3
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Inspection of Basic Internet Protocols
DNS Inspection
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
dns-guard
protocol-enforcement
nat-rewrite
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
! ...
service-policy global_policy global
(Optional) Configuring a DNS Inspection Policy Map and Class Map
To match DNS packets with certain characteristics and perform special actions, create a DNS inspection
policy map. You can also configure a DNS inspection class map to group multiple match criteria for
reference within the inspection policy map. You can then apply the inspection policy map when you
enable DNS inspection.
Prerequisites
If you want to match a DNS message domain name list, then create a regular expression using one of the
methods below:
•
“Creating a Regular Expression” section on page 1-14
•
“Creating a Regular Expression Class Map” section on page 1-17
.
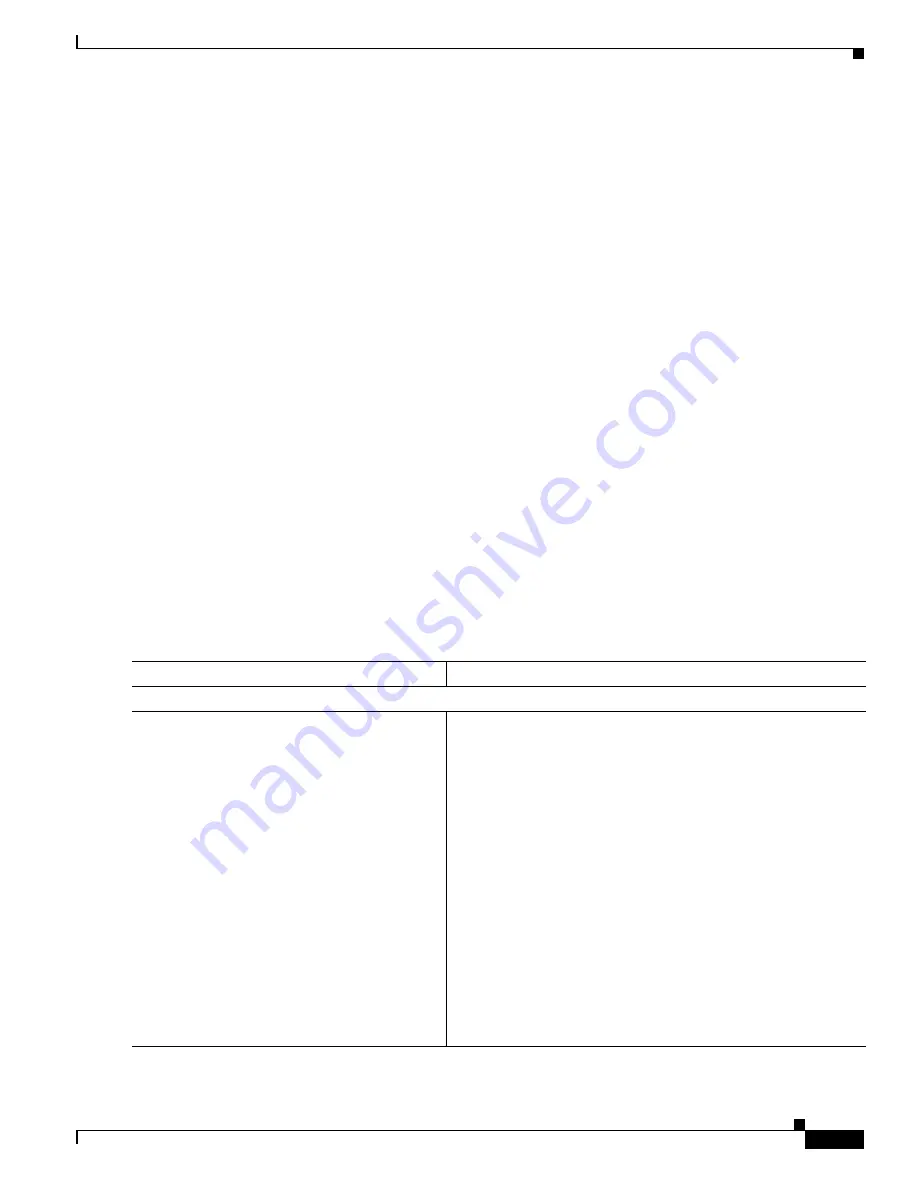
Detailed Steps
Command
Purpose
Step 1
Do one of the following:
class-map type
inspect
dns
[
match-all
|
match-any
]
class_map_name
Example:
hostname(config)# class-map type inspect
dns match-all dns-class-map
Creates a DNS inspection class map, where
class_map_name
is
the name of the class map. The
match-all
keyword is the default,
and specifies that traffic must match
all
criteria to match the class
map. The
match-any
keyword specifies that the traffic matches
the class map if it matches at least one of the criteria.
A class map groups multiple traffic matches. You can
alternatively identify
match
commands directly in the policy
map. The difference between creating a class map and defining
the traffic match directly in the inspection policy map is that the
class map lets you create more complex match criteria, and you
can reuse class maps.
The CLI enters class-map configuration mode, where you can
enter one or more
match
or
match not
commands.
For the traffic that you identify in this class map, you can only
specify actions (such as drop) for the entire class. If you want to
perform different actions for each
match
command, you should
identify the traffic directly in the policy map.
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......






























