1-82
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Clientless SSL VPN
Optimizing Clientless SSL VPN Performance
Detailed Steps
Disabling Content Rewrite
You might not want some applications and web resources, for example, public websites, to go through
the ASA. The ASA therefore lets you create rewrite rules that let users browse certain sites and
applications without going through the ASA. This is similar to split-tunneling in an IPsec VPN
connection.
Using Proxy Bypass
You can configure the ASA to use proxy bypass when applications and web resources work better with
the special content rewriting this feature provides. Proxy bypass is an alternative method of content
rewriting that makes minimal changes to the original content. It is often useful with custom web
applications.
You can use this command multiple times. The order in which you configure entries is unimportant. The
interface and path mask or interface and port uniquely identify a proxy bypass rule.
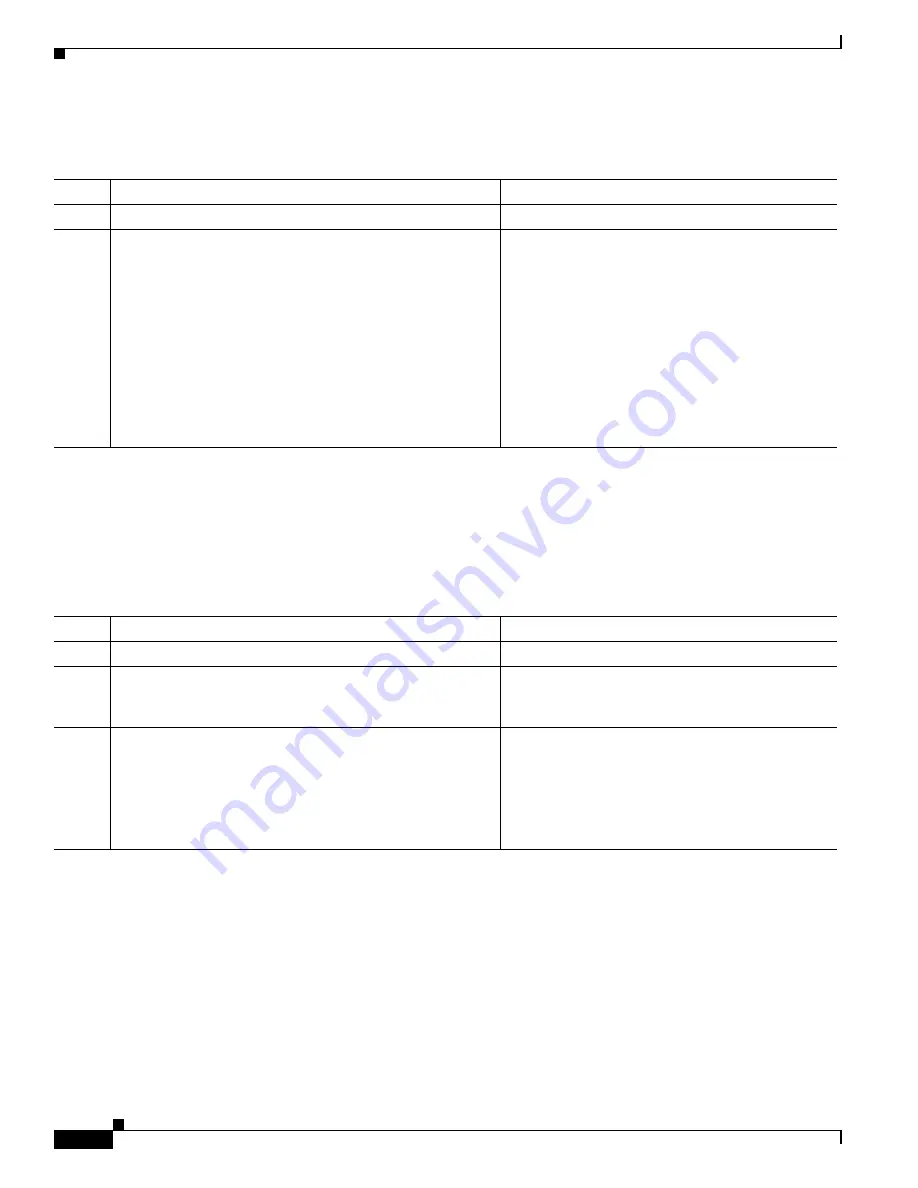
Command
Purpose
Step 1
crypto ca import
Imports a certificate.
Step 2
ava-trustpoint
Example:t
hostname(config)#
crypto ca import mytrustpoint
pkcs12 mypassphrase
Enter the base 64 encoded PKCS12.
End with the word “quit” on a line by itself.
[ PKCS12 data omitted ]
quit
INFO: Import PKCS12 operation completed
successfully.
hostname(config)#
webvpn
hostname(config)#
java-trustpoint mytrustpoint
Employs a certificate.
Shows the creation of a trustpoint named
mytrustpoint and its assignment to signing Java
objects
Command
Purpose
Step 1
webvpn
Switches to webvpn configuration mode.
Step 2
rewrite
Specifies applications and resources to access
outside a clientless SSLN VPN tunnel. You can use
this command multiple times.
Step 3
disable
Used in combination with the rewrite command. The
order number of rules is important because the
security appliance searches rewrite rules by order
number, starting with the lowest, and applies the
first rule that matches.
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......






























