Chapter 3 DXi3500 and DXi5500 Remote Management
Configuration
Quantum DXi3500 and DXi5500 User’s Guide
75
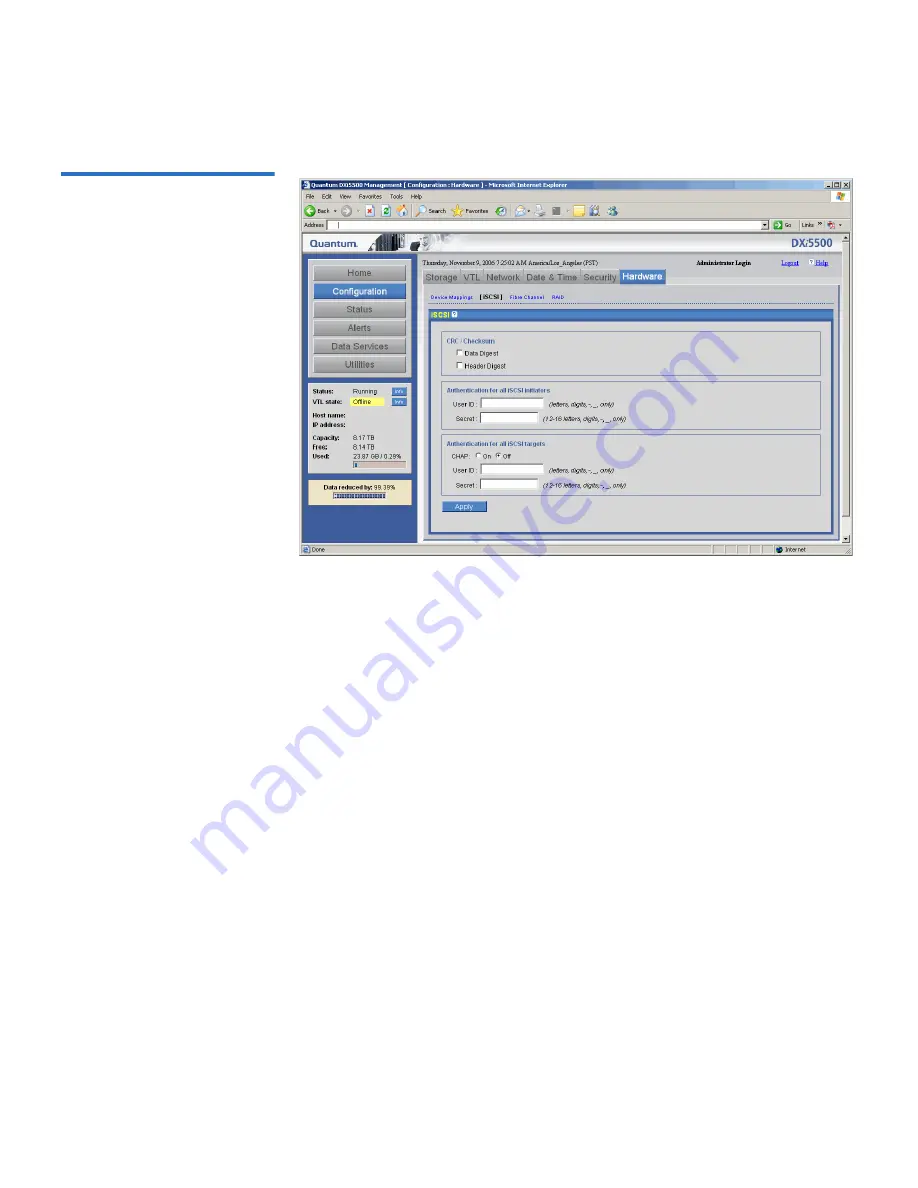
Figure 41 iSCSI Configuration
Page
Configure the following iSCSI settings as desired:
•
CRC/Checksum -
Cyclic Redundancy Check
is a common technique for
detecting data transmission errors. Messages are divided into
predetermined lengths that are divided by a fixed divisor. According
to the calculation, the remainder number is appended onto and sent
with the message. When the message is received, the computer
recalculates the remainder and compares it to the transmitted
remainder. If the numbers do not match, an error is detected.
•
Authentication for all iSCSI initiators -
Authentication for iSCSI
initiators is the process of identifying an initiator based on a
username and password. If you want to authenticate the iSCSI
initiators, enter a
User Name
and
Password
for the initiator.
•
Authentication for all iSCSI targets
:
•
CHAP -
Challenge Handshake Authentication Protocol
is an
authentication type in which the authentication agent (typically a
network server) sends the client program a random value that is
used only once and an ID value. Both the sender and peer share a
predefined secret. The peer concatenates the random value (or
nonce), the ID and the secret and calculates a one-way hash using
MD5. The hash value is sent to the authenticator, which in turn
builds that same string on its side, calculates the MD5 sum itself
and compares the result with the value received from the peer. If
















































