Protected Setup Pages
63
MVP-5200i Modero® ViewPoint® Touch Panel with Intercom - Instruction Manual
Refer to the
EAP Authentication
section on page 136 and the
Using the Site Survey Tool
section on page 30 for further details on
these security options.
EAP-TLS
In the
Wireless Security: Enterprise Mode
popup window (FIG. 62), press the
Security Type
field to select
EAP-TLS.
TLS (Transport Layer Security) was the original standard wireless LAN EAP authentication protocol. TLS requires additional work
during the deployment phase, but provides additional security since even a compromised password is not enough to break into an
EAP-TLS protected wireless network environment.
EAP-TLS security is designed for wireless environments where it is necessary to securely transmit data over a wireless network by
adding an additional level of security protocol via the use of a private key.
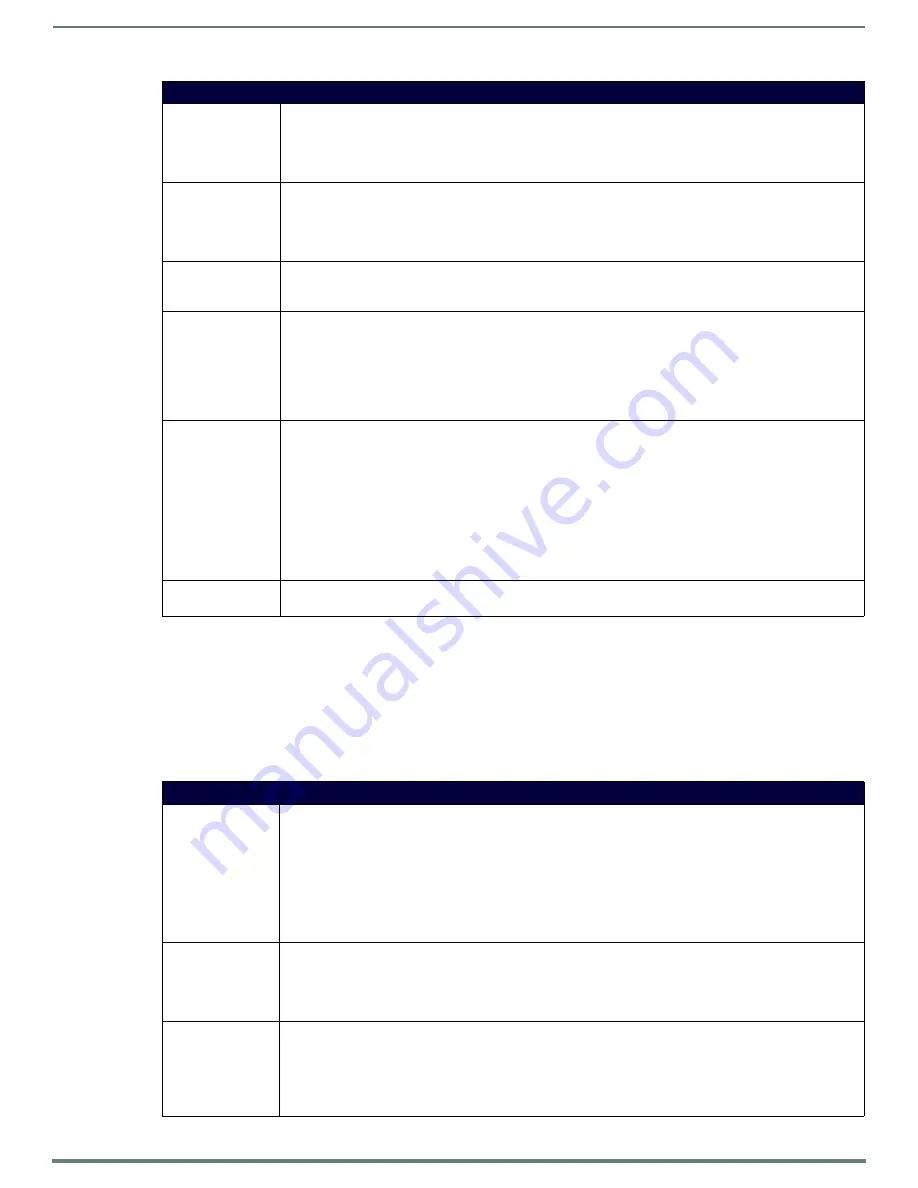
EAP-TTLS (Cont.)
Identity:
Opens an on-screen keyboard. Enter an EAP Identity string (used by the panel to identify itself to an
Authentication (RADIUS) Server).
Note: This information is similar to a username used to login to a secured server or workstation. This works in
tandem with the Password string which is similar to the password entered to gain access to a secured workstation.
Typically, this is in the form of a username such as: [email protected].
Anonymous Identity: Opens an on-screen keyboard. Enter an IT provided alpha-numeric string which (similar to the username) used as
the identity, but that does not represent a real user.
This information is used as a fictitious name which might be seen by sniffer programs during the initial connection
and setup process between the panel and the Radius server. In this way the real identity (username) is protected.
Typically, this is in the form of a fictitious username such as:
Password:
Opens an on-screen keyboard. Enter the network password string specified for the user entered within the
Identity
field (used by the panel to identify itself to an Authentication (RADIUS) Server)
Note: This information is similar to the password entered to gain access to a secured workstation.
Certificate Authority: When pressed, the panel displays an on-screen Certificate Authority (CA) File Location keyboard which allows you
to enter the name of the certificate authority file which is used to validate the server certificate. This field is
optional.
If a server certificate is used, it should first be downloaded into the panel and the
Certificate Authority
field should
then be set to the name of that certificate file. No file path should be used for this setting as all certificates are
stored in a specific directory that the user cannot control or change.
Use the on-screen keyboard’s
Clear
button to completely erase any previously stored network path information.
Inner Authentication
Type:
When pressed, this field cycles through the choices of available Inner Authentication mechanism supported by the
Devicescape Secure Wireless Client:
• EAP-MSCHAPv2
• EAP-GTC
• EAP-OTP
• EAP-MD5
• MSCHAPv2
• MSCHAP
• PAP
• CHAP
Cancel/Save:
• Cancel - discard changes and return to the previous page.
•
Save
- store the new security information, apply changes, and return to the previous page.
EAP-TLS
SSID:
Opens an on-screen keyboard for entering the SSID name used on the target AP. The SSID is a unique name used
by the AP, and is assigned to all panels on that network. An SSID is required by the AP before the panel is permitted
to join the network.
• The SSID is case sensitive and must not exceed 32 characters.
• Make sure this setting is the same for all points in the wireless network.
• With EAP security, the SSID of the AP
must
be entered. If it is left blank, the panel will try to connect to the first
access point detected that supports EAP. However, a successful connection is not guaranteed because the
detected AP may be connected to a RADIUS server, which may not support this EAP type and/or have the proper
user identities configured.
Identity:
Opens an on-screen keyboard for entering an EAP Identity string (used by the panel to identify itself to an
Authentication (RADIUS) Server).
Note: This information is similar to a username used to login to a secured server or workstation. This works in
tandem with the Password string, which is similar to the password entered to gain access to a secured workstation.
Typically, this is in the form of a username such as: [email protected].
Certificate Authority: When pressed, the panel displays an on-screen Certificate Authority (CA) File Location keyboard, for entering the
name of the certificate authority file which is used to validate the server certificate. This field is optional.
If a server certificate is used, it should first be downloaded into the panel and the
Certificate Authority
field should
then be set to the name of that certificate file. No file path should be used for this setting, as all certificates are
stored in a specific directory that the user cannot control or change.
• Use the on-screen keyboard’s
Clear
button to completely erase any previously stored network path information.
















































