Chapter 5 Wireless
B222s User’s Guide
60
5.7.2.4 Encryption
Wireless networks can use encryption to protect the information that is sent in the wireless
network. Encryption is like a secret code. If you do not know the secret code, you cannot
understand the message.
The types of encryption you can choose depend on the type of authentication. (See
Section 5.7.2.3
on page 59
for information about this.)
For example, if the wireless network has a RADIUS server, you can choose WPA or WPA2. If users
do not log in to the wireless network, you can choose no encryption, Static WEP, WPA-PSK, or
WPA2-PSK.
Usually, you should set up the strongest encryption that every device in the wireless network
supports. For example, suppose you have a wireless network with the LTE Device and you do not
have a RADIUS server. Therefore, there is no authentication. Suppose the wireless network has two
devices. Device A only supports WEP, and device B supports WEP and WPA. Therefore, you should
set up Static WEP in the wireless network.
Note: It is recommended that wireless networks use WPA-PSK, WPA, or stronger
encryption. The other types of encryption are better than none at all, but it is still
possible for unauthorized wireless devices to figure out the original information
pretty quickly.
When you select WPA2 or WPA2-PSK in your LTE Device, you can also select an option (WPA
compatible) to support WPA as well. In this case, if some of the devices support WPA and some
support WPA2, you should set up WPA2-PSK or WPA2 (depending on the type of wireless network
login) and select the WPA compatible option in the LTE Device.
Many types of encryption use a key to protect the information in the wireless network. The longer
the key, the stronger the encryption. Every device in the wireless network must have the same key.
5.7.3 Signal Problems
Because wireless networks are radio networks, their signals are subject to limitations of distance,
interference and absorption.
Problems with distance occur when the two radios are too far apart. Problems with interference
occur when other radio waves interrupt the data signal. Interference may come from other radio
transmissions, such as military or air traffic control communications, or from machines that are
coincidental emitters such as electric motors or microwaves. Problems with absorption occur when
physical objects (such as thick walls) are between the two radios, muffling the signal.
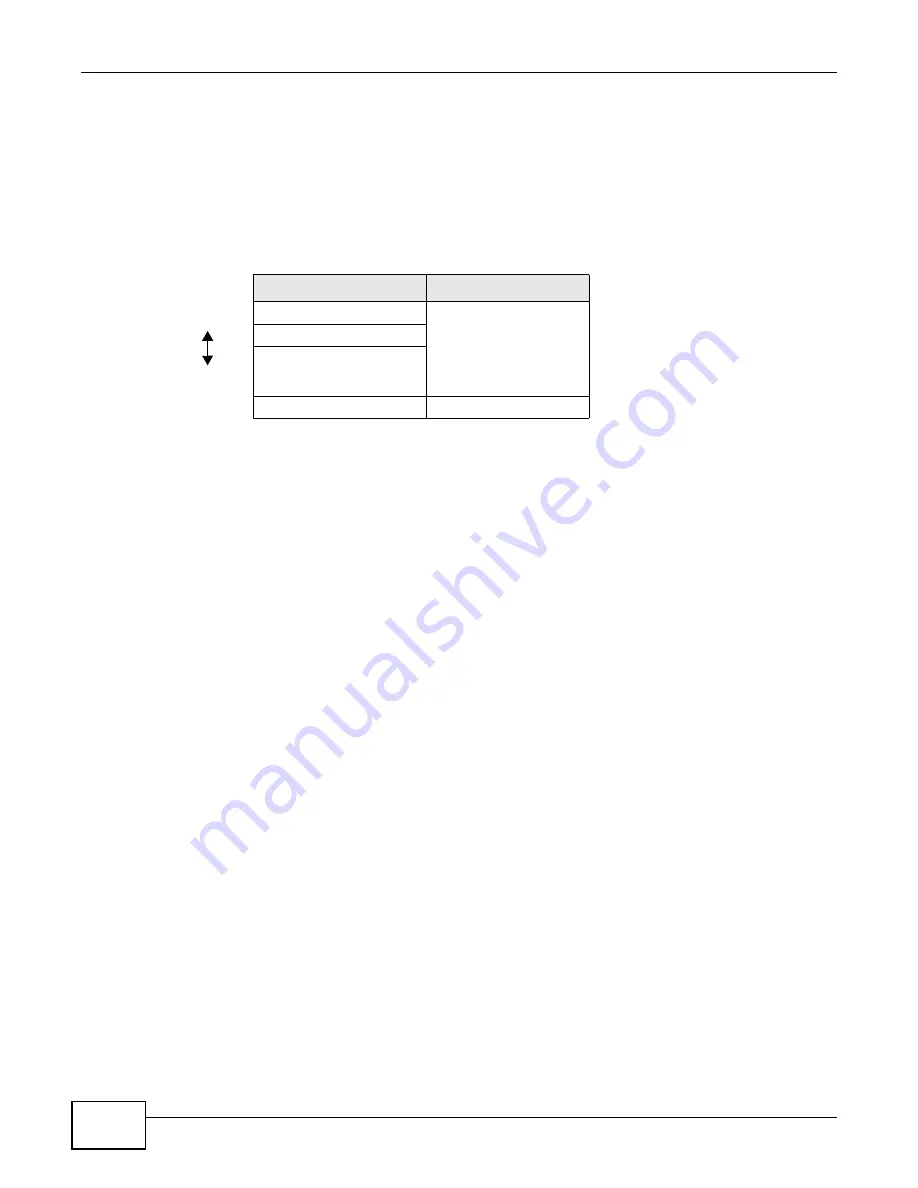
Table 18
Types of Encryption for Each Type of Authentication
NO AUTHENTICATION
RADIUS SERVER
Weakest
No Security
WPA
Static WEP
WPA-PSK
Strongest
WPA2-PSK
WPA2
Summary of Contents for B222s
Page 4: ...Contents Overview B222s User s Guide 4 ...
Page 12: ...Table of Contents B222s User s Guide 12 ...
Page 13: ...13 PART I User s Guide ...
Page 14: ...14 ...
Page 28: ...28 ...
Page 78: ...Chapter 7 Routing B222s User s Guide 78 ...
Page 82: ...Chapter 8 DNS Route B222s User s Guide 82 ...
Page 102: ...Chapter 10 Network Address Translation NAT B222s User s Guide 102 ...
Page 114: ...Chapter 12 Firewall B222s User s Guide 114 ...
Page 120: ...Chapter 14 Parental Control B222s User s Guide 120 ...
Page 125: ...Chapter 15 VoIP B222s User s Guide 125 ...
Page 144: ...Chapter 15 VoIP B222s User s Guide 144 ...
Page 154: ...Chapter 17 Traffic Status B222s User s Guide 154 ...
Page 156: ...Chapter 18 User Account B222s User s Guide 156 ...
Page 170: ...Chapter 24 Backup Restore B222s User s Guide 170 ...
Page 172: ...Chapter 25 Diagnostic B222s User s Guide 172 ...
Page 218: ...Appendix B Setting Up Your Computer s IP Address B222s User s Guide 218 ...
Page 228: ...Appendix C Pop up Windows JavaScript and Java Permissions B222s User s Guide 228 ...
Page 252: ...Appendix E Common Services B222s User s Guide 252 ...
















































