144
Configuring Switch-Based Authentication
Information About Configuring Switch-Based Authentication
You can also enable the login enhancements feature, which logs both failed and unsuccessful login attempts. Login
enhancements can also be configured to block future login attempts after a set number of unsuccessful attempts
are made.
Password Protection
A simple way of providing terminal access control in your network is to use passwords and assign privilege levels.
Password protection restricts access to a network or network device. Privilege levels define what commands users can
enter after they have logged into a network device.
Default Password and Privilege Level Configuration
Enable Secret Passwords with Encryption
To provide an additional layer of security, particularly for passwords that cross the network or that are stored on a Trivial
File Transfer Protocol (TFTP) server, you can use either the
enable password
or
enable secret
global configuration
commands. Both commands accomplish the same thing; that is, you can establish an encrypted password that users
must enter to access privileged EXEC mode (the default) or any privilege level you specify.
We recommend that you use the
enable secret
command because it uses an improved encryption algorithm.
If you configure the
enable secret
command, it takes precedence over the
enable password
command; the two
commands cannot be in effect simultaneously.
Use the
level
keyword to define a password for a specific privilege level. After you specify the level and set a password,
give the password only to users who need to have access at this level. Use the
privilege level
global configuration
command to specify commands accessible at various levels.
If you enable password encryption, it applies to all passwords including username passwords, authentication key
passwords, the privileged command password, and console and virtual terminal line passwords.
To remove a password and level, use the
no enable password
[
level
level
] or
no enable secret
[
level
level
] global
configuration command. To disable password encryption, use the
no service password-encryption
global configuration
command.
Password Recovery
Any end user with physical access to the switch can recover from a lost password by interrupting the boot process while
the switch is powering on and manually deleting the configuration of the switch.
Press and hold the factory default button when power is applied to the switch. You can release the button once you see
the
password-recovery mechanism is enabled
message. You will be at the boot loader prompt at this point and will be
able to delete the configuration file (which contains the forgotten password).
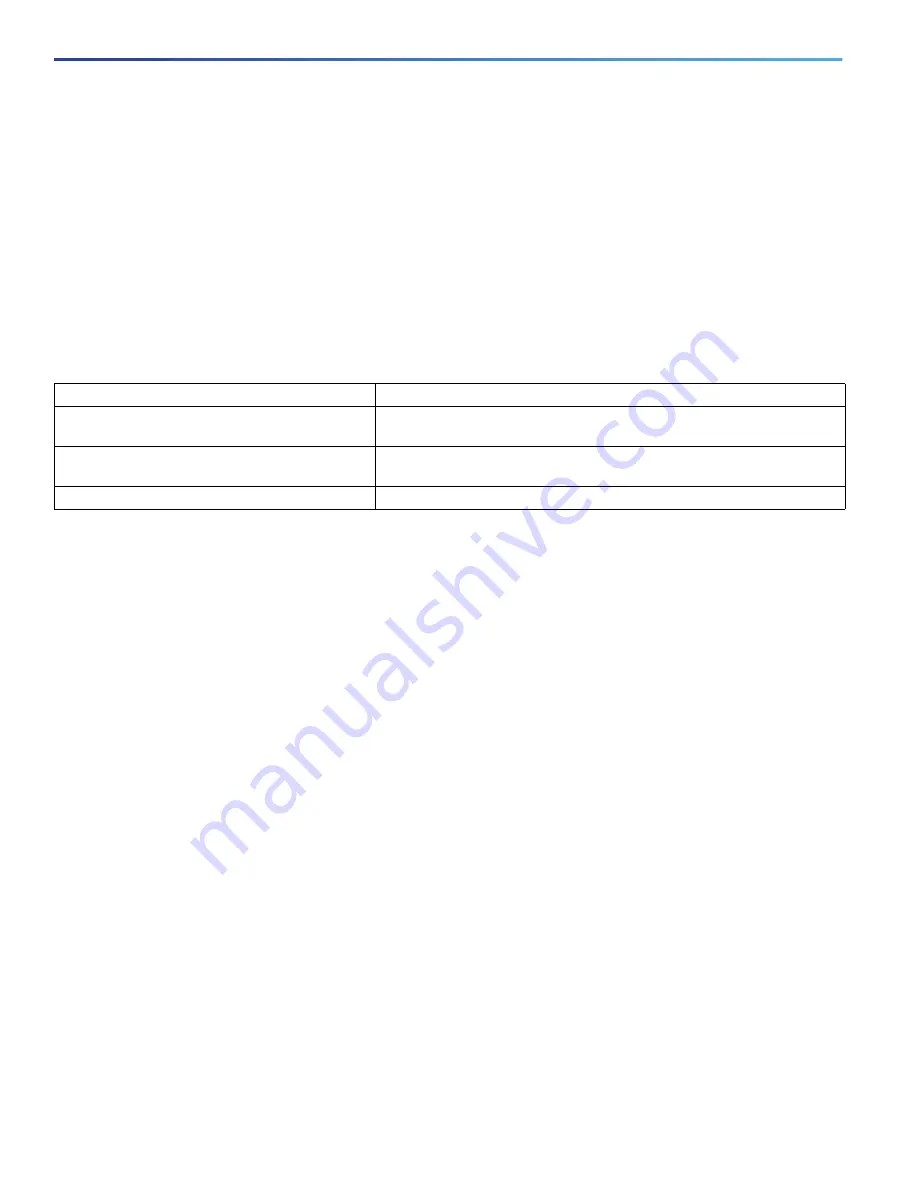
Table 25
Default Password and Privilege Levels
Feature
Default Setting
Enable password and privilege level
No password is defined. The default is level 15 (privileged EXEC level).
The password is not encrypted in the configuration file.
Enable secret password and privilege level
No password is defined. The default is level 15 (privileged EXEC level).
The password is encrypted before it is written to the configuration file.
Line password
No password is defined.
Содержание IE 4000
Страница 12: ...8 Configuration Overview Default Settings After Initial Switch Configuration ...
Страница 52: ...48 Configuring Interfaces Monitoring and Maintaining the Interfaces ...
Страница 108: ...104 Configuring Switch Clusters Additional References ...
Страница 128: ...124 Performing Switch Administration Additional References ...
Страница 130: ...126 Configuring PTP ...
Страница 140: ...136 Configuring CIP Additional References ...
Страница 146: ...142 Configuring SDM Templates Configuration Examples for Configuring SDM Templates ...
Страница 192: ...188 Configuring Switch Based Authentication Additional References ...
Страница 244: ...240 Configuring IEEE 802 1x Port Based Authentication Additional References ...
Страница 274: ...270 Configuring SGT Exchange Protocol over TCP SXP and Layer 3 Transport Configuring Cisco TrustSec Caching ...
Страница 298: ...294 Configuring VLANs Additional References ...
Страница 336: ...332 Configuring STP Additional References ...
Страница 408: ...404 Configuring DHCP Additional References ...
Страница 450: ...446 Configuring IGMP Snooping and MVR Additional References ...
Страница 490: ...486 Configuring SPAN and RSPAN Additional References ...
Страница 502: ...498 Configuring Layer 2 NAT ...
Страница 559: ...555 Configuring Network Security with ACLs How to Configure Network Security with ACLs Creating a Numbered Extended ACL ...
Страница 770: ...766 Configuring IPv6 MLD Snooping Related Documents ...
Страница 930: ...926 Configuring IP Unicast Routing Related Documents ...
Страница 956: ...952 Configuring IPv6 Unicast Routing Configuring IPv6 network 2010 AB8 2 48 network 2010 AB8 3 48 exit address family ...
Страница 976: ...972 Configuring Cisco IOS IP SLAs Operations Additional References ...
Страница 978: ...974 Dying Gasp ...
Страница 990: ...986 Configuring Enhanced Object Tracking Monitoring Enhanced Object Tracking ...
Страница 994: ...990 Configuring MODBUS TCP Displaying MODBUS TCP Information ...
Страница 996: ...992 Ethernet CFM ...
Страница 1030: ...1026 Working with the Cisco IOS File System Configuration Files and Software Images Working with Software Images ...
Страница 1066: ...1062 Using an SD Card SD Card Alarms ...
















































