DGS-3048 Gigabit Ethernet Switch Manual
Trusted Host
Go to the
Security
folder and click on the
Trusted Host
link; the following window will appear.
.
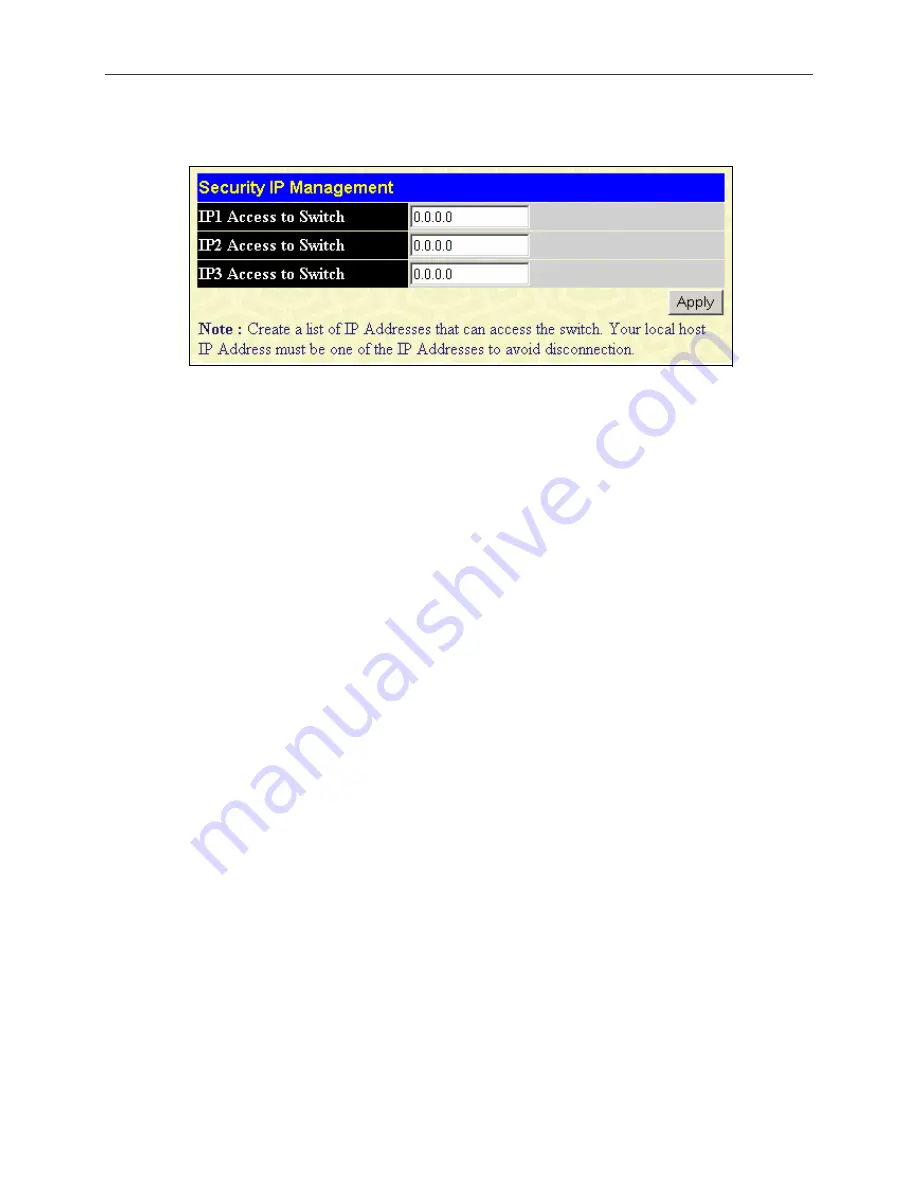
Figure 10- 9.Security IP Management Window
Use security IP management to permit remote stations to manage the Switch. If you choose to define one or more
designated management stations, only the chosen stations, as defined by IP address, will be allowed management privilege
through the web manager or Telnet session. To define a management station IP setting, type in the IP address and click the
Apply
button.
Access Authentication Control
The / RADIUS commands let you secure access to the Switch using the / / RADIUS protocols.
When a user logs in to the Switch or tries to access the administrator level privilege, he or she is prompted for a password. If
/ RADIUS authentication is enabled on the Switch, it will contact a / RADIUS server to verify the
user. If the user is verified, he or she is granted access to the Switch.
There are currently three versions of the TACACS security protocol, each a separate entity. The Switch's software supports
the following versions of TACACS:
•
(Terminal Access Controller Access Control System plus
) - Provides detailed access control for
authentication for network devices. is facilitated through Authentication commands via one or more
centralized servers. The protocol encrypts all traffic between the Switch and the daemon,
using the TCP protocol to ensure reliable delivery
In order for the / RADIUS security function to work properly, a / RADIUS server must be
configured on a device other than the Switch, called an Authentication Server Host and it must include usernames and
passwords for authentication. When the user is prompted by the Switch to enter usernames and passwords for authentication,
the Switch contacts the / RADIUS server to verify, and the server will respond with one of three messages:
•
The server verifies the username and password, and the user is granted normal user privileges on the Switch.
•
The server will not accept the username and password and the user is denied access to the Switch.
•
The server doesn't respond to the verification query. At this point, the Switch receives the timeout from the server
and then moves to the next method of verification configured in the method list.
The Switch has four built-in
Authentication Server Groups
, one for each of the and RADIUS protocols. These
built-in Authentication Server Groups are used to authenticate users trying to access the Switch. The users will set
Authentication Server Hosts
in a preferable order in the built-in Authentication Server Groups and when a user tries to gain
access to the Switch, the Switch will ask the first Authentication Server Hosts for authentication. If no authentication is
made, the second server host in the list will be queried, and so on. The built-in Authentication Server Groups can only have
hosts that are running the specified protocol. For example, the TACACS Authentication Server Groups can only have
TACACS Authentication Server Hosts.
The administrator for the Switch may set up six different authentication techniques per user-defined method list (
/ RADIUS / local / none) for authentication. These techniques will be listed in an order preferable, and defined by the user
for normal user authentication on the Switch, and may contain up to eight authentication techniques. When a user attempts
to access the Switch, the Switch will select the first technique listed for authentication. If the first technique goes through its
Authentication Server Hosts and no authentication is returned, the Switch will then go to the next technique listed in the
server group for authentication, until the authentication has been verified or denied, or the list is exhausted.
86
Содержание D DGS-3048 DGS-3048
Страница 1: ...D Link DGS 3048 Managed 48 Port Gigabit Ethernet Switch Manual ...
Страница 2: ......
Страница 29: ...DGS 3048 Gigabit Ethernet Switch Manual Figure 6 1 Enter Network Password Dialog Box 17 ...
Страница 146: ......
Страница 147: ......






























