Network Address Translation Overview
▀ NAT Feature Overview
▄ Cisco ASR 5000 Series Product Overview
OL-22938-02
In the Firewall-and-NAT policy configuration, the NAT policy must be enabled. Once NAT is enabled for a subscriber,
the NAT IP address to be used is chosen from the NAT IP pools/NAT IP pool groups specified in matching access rules
configured in the Firewall-and-NAT policy.
The Firewall-and-NAT policy used for a subscriber can be changed either from the command line interface, or through
dynamic update of policy name in Diameter and RADIUS messages. In both the cases, NAT status on the active call
remains unchanged.
The Firewall-and-NAT policy to be used for a subscriber can be configured in:
ECS Rulebase: The default Firewall-and-NAT policy configured in the ECS rulebase has the least priority. If
there is no policy configured in the APN/subscriber template, and/or no policy to use is received from the
AAA/OCS, only then the default policy configured in the ECS rulebase is used.
APN/Subscriber Template: The Firewall-and-NAT policy configured in the APN/subscriber template overrides
the default policy configured in the ECS rulebase. To use the default policy configured in the ECS rulebase, in
the APN/subscriber configuration, the command to use the default rulebase policy must be configured.
AAA/OCS: The Firewall-and-NAT policy to be used can come from the AAA server or the OCS. If the policy
comes from the AAA/OCS, it will override the policy configured in the APN/subscriber template and/or the
ECS rulebase.
Important:
The Firewall-and-NAT policy received from the AAA and OCS have the same priority. Whichever
comes latest, either from AAA/OCS, is applied.
The Firewall-and-NAT policy to use can also be received from RADIUS during authentication.
Disabling NAT Policy
Important:
By default, NAT processing for subscribers is disabled.
NAT processing for subscribers is disabled in the following cases:
If the AAA/OCS sends the SN-Firewall-Policy AVP with the string ―disable‖, the locally configured Firewall-
and-NAT policy does not get applied.
If the SN-Firewall-Policy AVP is received with the string ―NULL‖, the existing Firewall-and-NAT policy will
continue.
If the SN-Firewall-Policy AVP is received with a name that is not configured locally, the subscriber session is
terminated.
Updating Firewall-and-NAT Policy in Mid-session
The Firewall-and-NAT policy can be updated mid-session provided the policy was enabled during call setup.
Содержание ASR 5000 Series
Страница 1: ......
Страница 26: ......
Страница 48: ...New In Release 10 0 SCM Features Cisco ASR 5000 Series Product Overview OL 22938 02 ...
Страница 50: ......
Страница 58: ......
Страница 67: ...Product Service and Feature Licenses Default Licenses Cisco ASR 5000 Series Product Overview OL 22938 02 ...
Страница 68: ......
Страница 126: ......
Страница 138: ......
Страница 146: ......
Страница 218: ......
Страница 236: ......
Страница 356: ......
Страница 374: ......
Страница 422: ......
Страница 496: ......
Страница 572: ......
Страница 654: ......
Страница 700: ......
Страница 726: ......
Страница 784: ......
Страница 816: ......
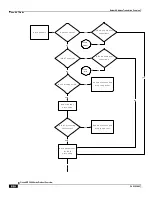
Страница 839: ...Network Address Translation Overview How NAT Works Cisco ASR 5000 Series Product Overview OL 22938 02 ...
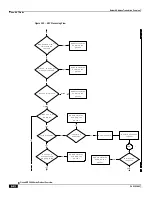
Страница 841: ...Network Address Translation Overview How NAT Works Cisco ASR 5000 Series Product Overview OL 22938 02 ...
Страница 844: ......
Страница 906: ......
Страница 926: ......
Страница 942: ......
Страница 943: ...Cisco ASR 5000 Series Product Overview OL 22938 02 Chapter 30 Technical Specifications ...
Страница 966: ......
Страница 967: ...Cisco ASR 5000 Series Product Overview OL 22938 02 Chapter 31 Safety Electrical and Environmental Certifications ...
Страница 972: ......