156
Asanté IntraCore 36000 Series
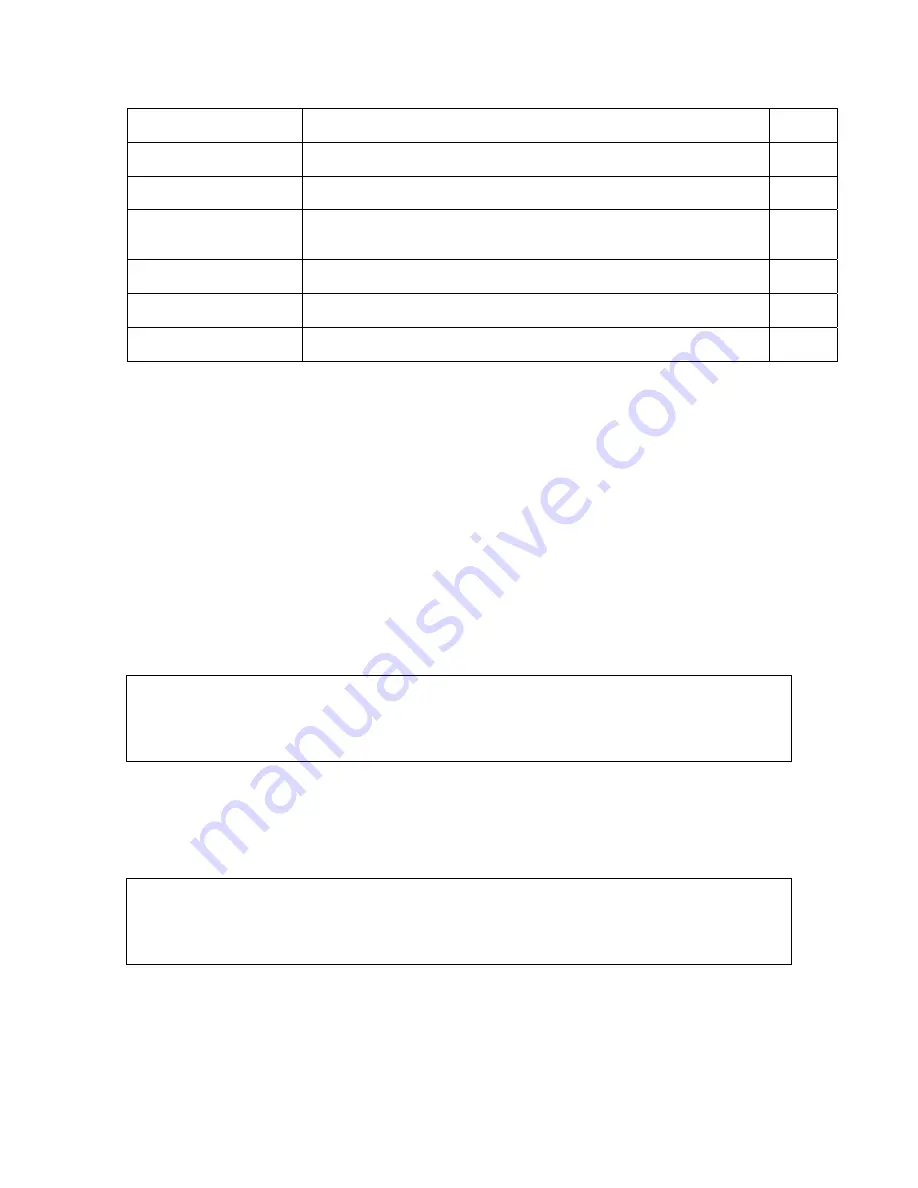
ip ssh crypto zeroize
Clear the host key from RAM
PE
ip ssh save host-key
Saves the host key from RAM to flash memory
PE
disconnect
Terminates a line connection
PE
show ip ssh
Displays the status of the SSH server and the configured values for
authentication timeout and retries
PE
show ssh
Displays the status of current SSH sessions
PE
show public-key
Shows the public key for the specified user or for the host
PE
show users
Shows SSH users, including privilege level and public key type
PE
The SSH server on this switch supports both password and public key authentication. If password
authentication is specified by the SSH client, then the password can be authenticated either locally or via a
RADIUS or remote authentication server, as specified by the
authentication login
command. If
public key authentication is specified by the client, then you must configure authentication keys on both the
client and the switch as described in the following section. Note that regardless of whether you use public
key or password authentication, you still have to generate authentication keys on the switch and enable the
SSH server.
To use the SSH server, complete these steps:
1. Generate a Host Key Pair – Use the ip ssh crypto host-key generate command to create a host
public/private key pair.
2. Provide Host Public Key to Clients – Many SSH client programs automatically import the host public
key during the initial connection setup with the switch. Otherwise, you need to manually create a
known hosts file on the management station and place the host public key in it. An entry for a public
key in the known hosts file would appear similar to the following example:
10.1.0.54 1024 35 15684995401867669259333946775054617325313674890836547254
15020245593199868544358361651999923329781766065830956 10825913212890233
76546801726272571413428762941301196195566782 59566410486957427888146206
5194174677298486546861571773939016477935594230357741309802273708779454524083971
752646358058176716709574804776117
3. Import Client’s Public Key to the Switch – Use the copy tftp public-key command to copy a file
containing the public key for all the SSH client’s granted management access to the switch. (Note
that these clients must be configured locally on the switch using the User Accounts page as
described in section
6.1.1 Configuring User Accounts
.) The clients are subsequently
authenticated using these keys. The current firmware only accepts public key files based on
standard UNIX format as shown in the following example for an RSA Version 1 key:
1024 35 1341081685609893921040944920155425347631641921872958921143173880
0555361616310517759408386863110929123222682851925437460310093718772119969631781
3662774141689851320491172048303392543241016379975923714490119380060902539484084
8271781943722884025331159521348610229029789827213532671316294325328189150453063
93916643 [email protected]
4. Set the Optional Parameters – Set other optional parameters, including the authentication timeout,
the number of retries, and the server key size.
5. Enable SSH Service – Use the ip ssh server command to enable the SSH server on the switch.
6. Configure Challenge-Response Authentication – When an SSH client attempts to contact the switch,
the SSH server uses the host key pair to negotiate a session key and encryption method. Only






























