DWS-3160 Series Gigabit Ethernet Unified Switch Web UI Reference Guide
351
Neighbor Client MAC
The Ethernet address of client station.
RSSI
Received Signal Strength Indication, this is an indicator of the signal strength
relative to the neighbor and may give an idea of the neighbor's distance from the
managed AP. The range is from 1 to 100, where 1 is the weakest signal strength.
Channel
The managed AP channel the client frame was received on, which may be different
than the operating channel for this radio.
Discovery Reason
Indicate one or more discovery methods for the neighbor client. One or more of the
following values may be displayed:
•
RF
- The client was reported from an RF scan on the radio. Note that client
stations are difficult to detect via RF scan, the other methods are more
common for client neighbor detection.
•
Probe Request
- The managed AP received a probe request from the client.
•
Associated to Managed AP
- This neighbor client is associated to another
managed AP.
•
Associated to this AP
- The client is associated to this managed AP on the
displayed radio.
•
Associated to Peer AP
- The client is associated to an AP managed by a peer
switch.
•
Ad Hoc Rogue
- The client was detected as part of an Ad Hoc network.
Age
Indicate the time since this client was last reported from an RF scan on the radio.
Click the Neighbor Client MAC hyperlink to see the detail information about Detected Clients.
Click the
Delete All Neighbors
to remove all the neighbor entries.
Enter a page number and click the
Go
button to navigate to a specific page when multiple pages exist.
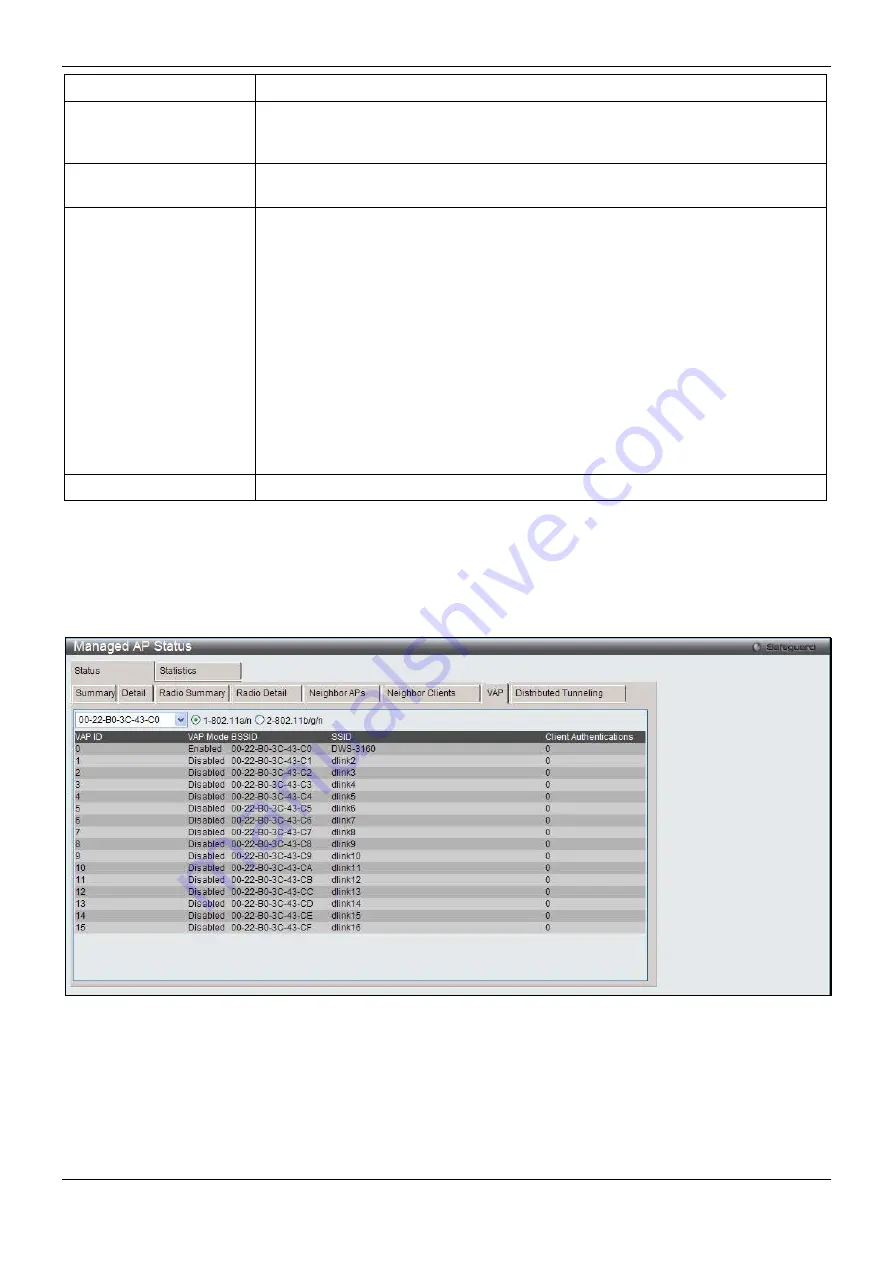
After clicking the
VAP
tab under the
Status
tab, the following page will appear:
Figure 2-19 Managed AP Status – VAP window
Use the drop down menu to select AP’s MAC address and use the radio button to select a radio to view the details
about VAPs on that radio.
After clicking the
Distributed Tunneling
tab under the
Status
tab, the following page will appear:






























