ZyWALL 5 User’s Guide
Chapter 15 Certificates
273
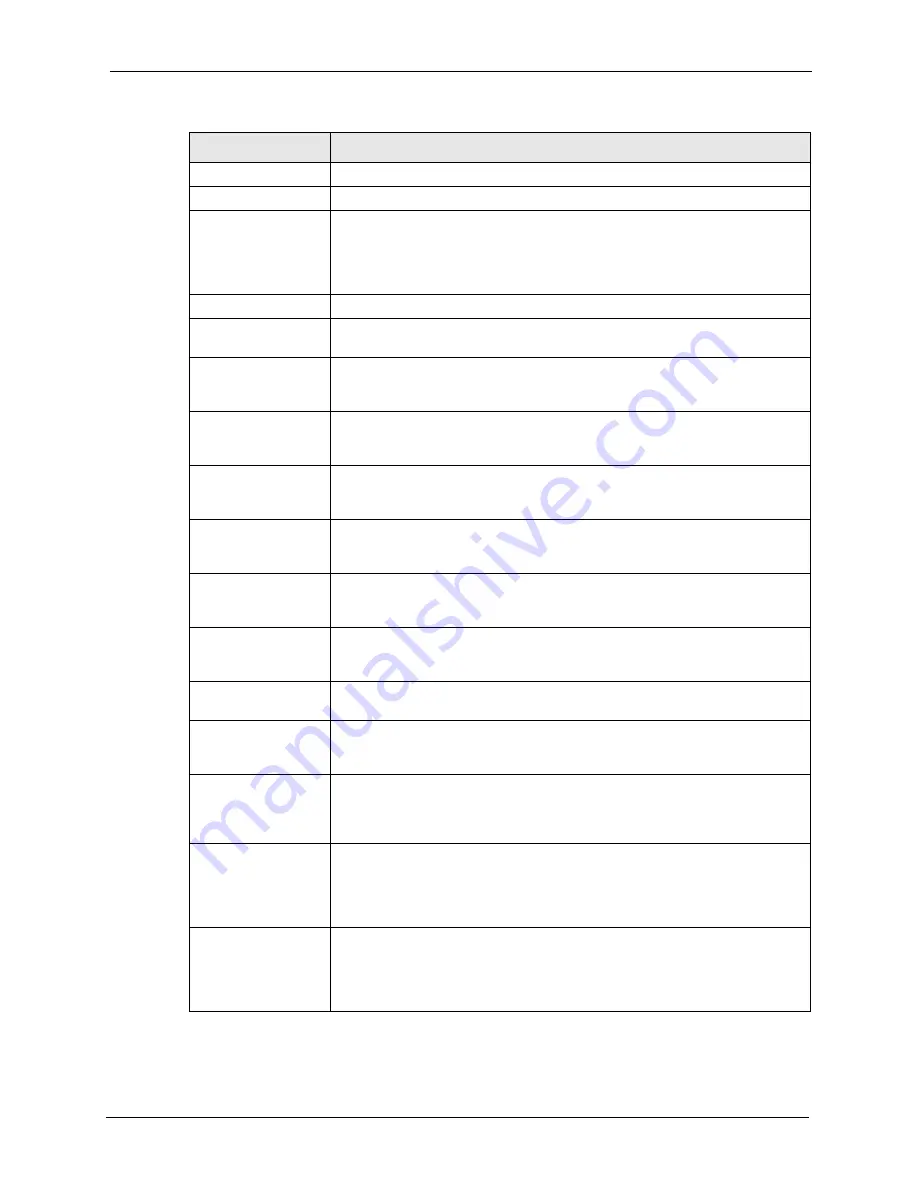
Refresh
Click
Refresh
to display the certification path.
Certificate Information These read-only fields display detailed information about the certificate.
Type
This field displays general information about the certificate. With trusted remote
host certificates, this field always displays CA-signed. The ZyWALL is the
Certification Authority that signed the certificate. X.509 means that this
certificate was created and signed according to the ITU-T X.509
recommendation that defines the formats for public-key certificates.
Version
This field displays the X.509 version number.
Serial Number
This field displays the certificate’s identification number given by the device that
created the certificate.
Subject
This field displays information that identifies the owner of the certificate, such
as Common Name (CN), Organizational Unit (OU), Organization (O) and
Country (C).
Issuer
This field displays identifying information about the default self-signed
certificate on the ZyWALL that the ZyWALL uses to sign the trusted remote
host certificates.
Signature Algorithm
This field displays the type of algorithm that the ZyWALL used to sign the
certificate, which is rsa-pkcs1-sha1 (RSA public-private key encryption
algorithm and the SHA1 hash algorithm).
Valid From
This field displays the date that the certificate becomes applicable. The text
displays in red and includes a Not Yet Valid! message if the certificate has not
yet become applicable.
Valid To
This field displays the date that the certificate expires. The text displays in red
and includes an Expiring! or Expired! message if the certificate is about to
expire or has already expired.
Key Algorithm
This field displays the type of algorithm that was used to generate the
certificate’s key pair (the ZyWALL uses RSA encryption) and the length of the
key set in bits (1024 bits for example).
Subject Alternative
Name
This field displays the certificate’s owner‘s IP address (IP), domain name (DNS)
or e-mail address (EMAIL).
Key Usage
This field displays for what functions the certificate’s key can be used. For
example, “DigitalSignature” means that the key can be used to sign certificates
and “KeyEncipherment” means that the key can be used to encrypt text.
Basic Constraint
This field displays general information about the certificate. For example,
Subject Type=CA means that this is a certification authority’s certificate and
“Path Length Constraint=1” means that there can only be one certification
authority in the certificate’s path.
MD5 Fingerprint
This is the certificate’s message digest that the ZyWALL calculated using the
MD5 algorithm. You cannot use this value to verify that this is the remote host’s
actual certificate because the ZyWALL has signed the certificate; thus causing
this value to be different from that of the remote hosts actual certificate. See
for how to verify a remote host’s certificate.
SHA1 Fingerprint
This is the certificate’s message digest that the ZyWALL calculated using the
SHA1 algorithm. You cannot use this value to verify that this is the remote
host’s actual certificate because the ZyWALL has signed the certificate; thus
causing this value to be different from that of the remote hosts actual certificate.
See
for how to verify a remote host’s certificate.
Table 86
Trusted Remote Host Details (continued)
LABEL
DESCRIPTION
Summary of Contents for ZyXEL ZyWALL 5
Page 1: ...ZyWALL 5 Internet Security Appliance User s Guide Version 3 64 3 2005 ...
Page 2: ......
Page 26: ...ZyWALL 5 User s Guide 24 ...
Page 44: ...ZyWALL 5 User s Guide 42 ...
Page 86: ...ZyWALL 5 User s Guide 84 Chapter 3 Wizard Setup ...
Page 96: ...ZyWALL 5 User s Guide 94 Chapter 4 LAN Screens ...
Page 102: ...ZyWALL 5 User s Guide 100 Chapter 5 Bridge Screens ...
Page 130: ...ZyWALL 5 User s Guide 128 Chapter 7 WAN Screens Figure 45 WAN PPPoE Encapsulation ...
Page 138: ...ZyWALL 5 User s Guide 136 Chapter 7 WAN Screens Figure 50 Dial Backup Setup ...
Page 144: ...ZyWALL 5 User s Guide 142 Chapter 7 WAN Screens ...
Page 152: ...ZyWALL 5 User s Guide 150 Chapter 8 DMZ Screens ...
Page 179: ...ZyWALL 5 User s Guide Chapter 10 Firewall Screens 177 Figure 73 My Service Rule Configuration ...
Page 220: ...ZyWALL 5 User s Guide 218 Chapter 13 Introduction to IPSec ...
Page 238: ...ZyWALL 5 User s Guide 236 Chapter 14 VPN Screens Figure 110 VPN Rules IKE Network Policy Edit ...
Page 261: ...ZyWALL 5 User s Guide Chapter 15 Certificates 259 Figure 122 My Certificate Details ...
Page 280: ...ZyWALL 5 User s Guide 278 Chapter 16 Authentication Server Figure 133 Local User Database ...
Page 317: ...ZyWALL 5 User s Guide Chapter 19 Bandwidth Management 315 ...
Page 318: ...ZyWALL 5 User s Guide 316 Chapter 19 Bandwidth Management ...
Page 352: ...ZyWALL 5 User s Guide 350 Chapter 21 Remote Management ...
Page 366: ...ZyWALL 5 User s Guide 364 Chapter 23 Logs Screens Figure 188 Log Settings ...
Page 389: ...ZyWALL 5 User s Guide Chapter 24 Maintenance 387 Figure 210 Restart Screen ...
Page 390: ...ZyWALL 5 User s Guide 388 Chapter 24 Maintenance ...
Page 416: ...ZyWALL 5 User s Guide 414 Chapter 27 WAN and Dial Backup Setup ...
Page 432: ...ZyWALL 5 User s Guide 430 Chapter 30 DMZ Setup ...
Page 492: ...ZyWALL 5 User s Guide 490 Chapter 37 System Information Diagnosis ...
Page 508: ...ZyWALL 5 User s Guide 506 Chapter 38 Firmware and Configuration File Maintenance ...
Page 520: ...ZyWALL 5 User s Guide 518 Chapter 40 Remote Management ...
Page 536: ...ZyWALL 5 User s Guide 534 Chapter 42 Troubleshooting Figure 343 Java Sun ...
Page 564: ...ZyWALL 5 User s Guide 562 Appendix C IP Subnetting ...
Page 570: ...ZyWALL 5 User s Guide 568 Appendix E PPTP ...
Page 571: ...ZyWALL 5 User s Guide 569 ...
Page 572: ...ZyWALL 5 User s Guide 570 ...
Page 590: ...ZyWALL 5 User s Guide 588 Appendix G Triangle Route ...
Page 620: ...ZyWALL 5 User s Guide 618 Appendix J Importing Certificates ...
Page 622: ...ZyWALL 5 User s Guide 620 Appendix K Command Interpreter ...
Page 628: ...ZyWALL 5 User s Guide 626 Appendix L Firewall Commands ...
Page 632: ...ZyWALL 5 User s Guide 630 Appendix M NetBIOS Filter Commands ...
Page 638: ...ZyWALL 5 User s Guide 636 Appendix O Brute Force Password Guessing Protection ...
Page 660: ...ZyWALL 5 User s Guide 658 Appendix Q Log Descriptions ...








































