52
Chapter 6: The Administrative Functions in the Wireless Network Monitor
Security Monitor
Wireless-G Business PCI Adapter with RangeBooster
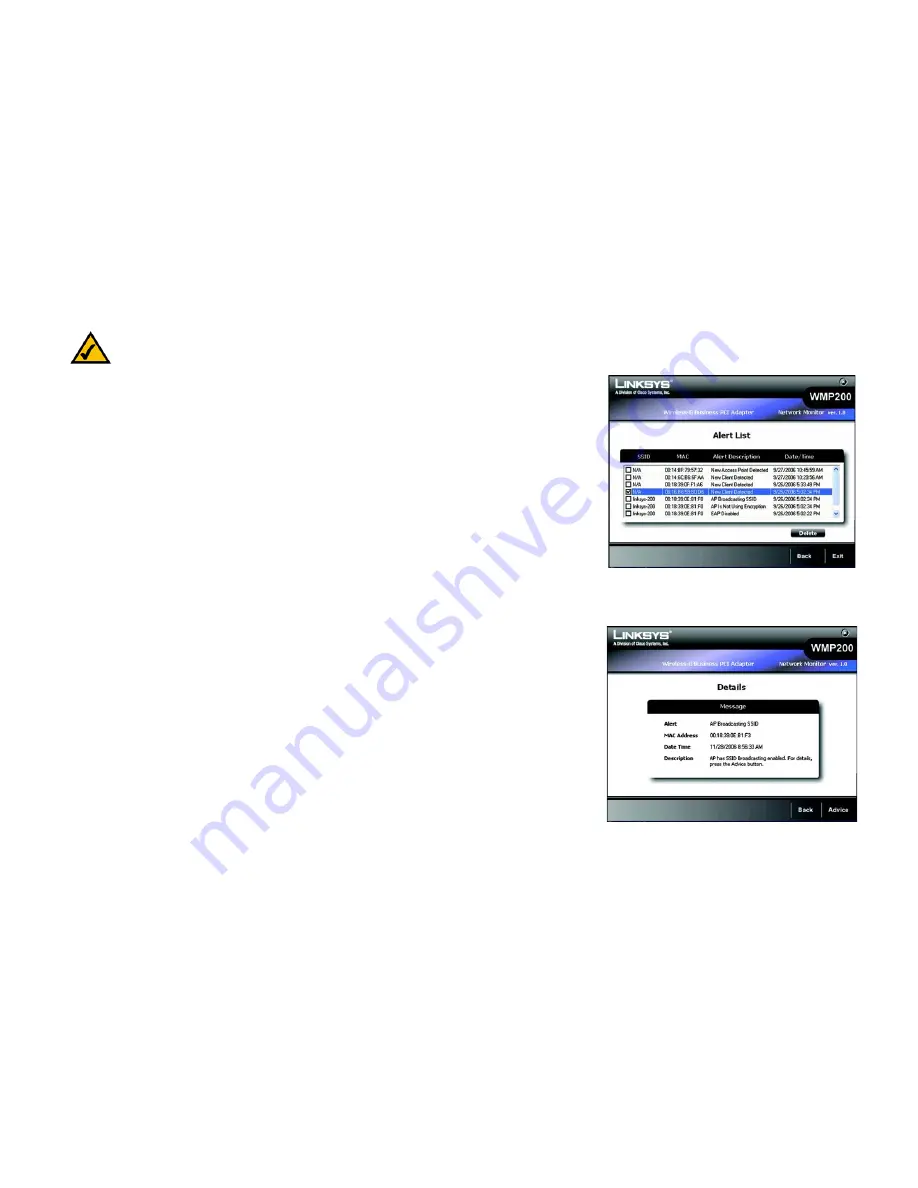
Alert List
The
Alert List
screen shows the list of the alert activities within your monitored wireless networks.
SSID
- This shows the SSID (network name) of your wireless network.
MAC
- This shows the MAC Address of the wireless client or access point that was detected.
Alert Description
- This shows brief descriptions of the alert activities. The alert system will alert you when new
access points or wireless clients are detected, or if other policy violations or attacks are detected.
Date/Time
- This indicates the date/time that an alert activity happened.
Delete
- Select an item, then click this button to delete the item.
Click
Back
to go to the previous screen or
Exit
to go to the main menu.
Alert Details
The
Details
screen
shows the detailed message of each alert event.
Message
- This indicates the description of the event.
MAC Address
- This shows the MAC Address of the wireless client or Access Point that performed the action.
Date/Time
- This shows the Date/Time of the alert.
Description
- This shows the detailed description of the event.
You may click the
Advice
button to view the advice message,
Back
to go back to the previous screen, or
Exit
to
go back to the main menu.
NOTE:
You will be alerted when an Access Point is detected, if you enable po-up.
Figure 6-17: Alert Details
Figure 6-16: Security Monitor - Alert List
Summary of Contents for WMP200
Page 92: ...84 Appendix H Regulatory Information Wireless G Business PCI Adapter with RangeBooster...
Page 93: ...85 Appendix H Regulatory Information Wireless G Business PCI Adapter with RangeBooster...
Page 94: ...86 Appendix H Regulatory Information Wireless G Business PCI Adapter with RangeBooster...