ZyWALL 5 User’s Guide
Chapter 14 VPN Screens
239
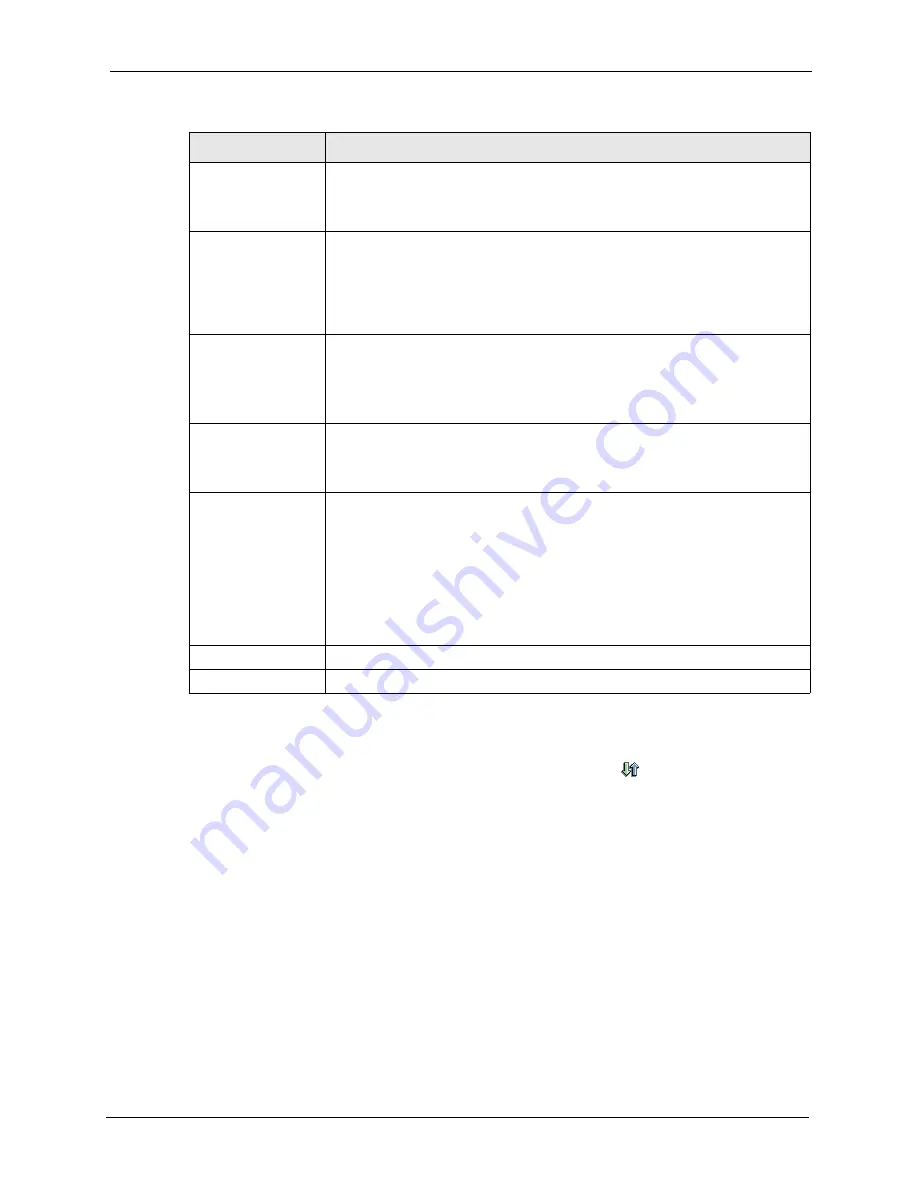
14.12.2.1 Associating a Network Policy to a Gateway Policy
To associate a network policy to a gateway rule, click the move (
) icon in the
VPN Rules
(IKE)
screen. A screen displays as shown below.
Authentication
Algorithm
MD5
(Message Digest 5) and
SHA1
(Secure Hash Algorithm) are hash
algorithms used to authenticate packet data. The
SHA1
algorithm is generally
considered stronger than
MD5
, but is slower. Select
MD5
for minimal security
and
SHA-1
for maximum security.
SA Life Time
(Seconds)
Define the length of time before an IKE SA automatically renegotiates in this
field. The minimum value is 180 seconds.
A short SA Life Time increases security by forcing the two VPN gateways to
update the encryption and authentication keys. However, every time the VPN
tunnel renegotiates, all users accessing remote resources are temporarily
disconnected.
Perfect Forward
Secret (PFS)
Perfect Forward Secret (PFS) is disabled (
NONE
) by default in phase 2 IPSec
SA setup. This allows faster IPSec setup, but is not so secure.
Select
DH1
or
DH2
to enable PFS.
DH1
refers to Diffie-Hellman Group 1 a 768
bit random number.
DH2
refers to Diffie-Hellman Group 2 a 1024 bit (1Kb)
random number (more secure, yet slower).
Enable Replay
Detection
As a VPN setup is processing intensive, the system is vulnerable to Denial of
Service (DOS) attacks. The IPSec receiver can detect and reject old or duplicate
packets to protect against replay attacks. Enable replay detection by selecting
this check box.
Enable Multiple
Proposal
Select this check box to allow the ZyWALL to use any of its phase 1 or phase 2
encryption and authentication algorithms when negotiating an IPSec SA.
When you enable multiple proposals, the ZyWALL allows the remote IPSec
router to select which encryption and authentication algorithms to use for the
VPN tunnel, even if they are less secure than the ones you configure for the
VPN rule.
Clear this check box to have the ZyWALL use only the phase 1 or phase 2
encryption and authentication algorithms configured below when negotiating an
IPSec SA.
Apply
Click
Apply
to save the changes.
Cancel
Click
Cancel
to discard all changes and return to the main VPN screen.
Table 69
VPN Rules (IKE): Network Policy Edit (continued)
LABEL
DESCRIPTION
Содержание ZyXEL ZyWALL 5
Страница 1: ...ZyWALL 5 Internet Security Appliance User s Guide Version 3 64 3 2005 ...
Страница 2: ......
Страница 26: ...ZyWALL 5 User s Guide 24 ...
Страница 44: ...ZyWALL 5 User s Guide 42 ...
Страница 86: ...ZyWALL 5 User s Guide 84 Chapter 3 Wizard Setup ...
Страница 96: ...ZyWALL 5 User s Guide 94 Chapter 4 LAN Screens ...
Страница 102: ...ZyWALL 5 User s Guide 100 Chapter 5 Bridge Screens ...
Страница 130: ...ZyWALL 5 User s Guide 128 Chapter 7 WAN Screens Figure 45 WAN PPPoE Encapsulation ...
Страница 138: ...ZyWALL 5 User s Guide 136 Chapter 7 WAN Screens Figure 50 Dial Backup Setup ...
Страница 144: ...ZyWALL 5 User s Guide 142 Chapter 7 WAN Screens ...
Страница 152: ...ZyWALL 5 User s Guide 150 Chapter 8 DMZ Screens ...
Страница 174: ...ZyWALL 5 User s Guide 172 Chapter 10 Firewall Screens Figure 68 Creating Editing A Firewall Rule ...
Страница 179: ...ZyWALL 5 User s Guide Chapter 10 Firewall Screens 177 Figure 73 My Service Rule Configuration ...
Страница 220: ...ZyWALL 5 User s Guide 218 Chapter 13 Introduction to IPSec ...
Страница 238: ...ZyWALL 5 User s Guide 236 Chapter 14 VPN Screens Figure 110 VPN Rules IKE Network Policy Edit ...
Страница 261: ...ZyWALL 5 User s Guide Chapter 15 Certificates 259 Figure 122 My Certificate Details ...
Страница 280: ...ZyWALL 5 User s Guide 278 Chapter 16 Authentication Server Figure 133 Local User Database ...
Страница 317: ...ZyWALL 5 User s Guide Chapter 19 Bandwidth Management 315 ...
Страница 318: ...ZyWALL 5 User s Guide 316 Chapter 19 Bandwidth Management ...
Страница 352: ...ZyWALL 5 User s Guide 350 Chapter 21 Remote Management ...
Страница 366: ...ZyWALL 5 User s Guide 364 Chapter 23 Logs Screens Figure 188 Log Settings ...
Страница 389: ...ZyWALL 5 User s Guide Chapter 24 Maintenance 387 Figure 210 Restart Screen ...
Страница 390: ...ZyWALL 5 User s Guide 388 Chapter 24 Maintenance ...
Страница 416: ...ZyWALL 5 User s Guide 414 Chapter 27 WAN and Dial Backup Setup ...
Страница 432: ...ZyWALL 5 User s Guide 430 Chapter 30 DMZ Setup ...
Страница 492: ...ZyWALL 5 User s Guide 490 Chapter 37 System Information Diagnosis ...
Страница 508: ...ZyWALL 5 User s Guide 506 Chapter 38 Firmware and Configuration File Maintenance ...
Страница 520: ...ZyWALL 5 User s Guide 518 Chapter 40 Remote Management ...
Страница 536: ...ZyWALL 5 User s Guide 534 Chapter 42 Troubleshooting Figure 343 Java Sun ...
Страница 564: ...ZyWALL 5 User s Guide 562 Appendix C IP Subnetting ...
Страница 570: ...ZyWALL 5 User s Guide 568 Appendix E PPTP ...
Страница 571: ...ZyWALL 5 User s Guide 569 ...
Страница 572: ...ZyWALL 5 User s Guide 570 ...
Страница 590: ...ZyWALL 5 User s Guide 588 Appendix G Triangle Route ...
Страница 620: ...ZyWALL 5 User s Guide 618 Appendix J Importing Certificates ...
Страница 622: ...ZyWALL 5 User s Guide 620 Appendix K Command Interpreter ...
Страница 628: ...ZyWALL 5 User s Guide 626 Appendix L Firewall Commands ...
Страница 632: ...ZyWALL 5 User s Guide 630 Appendix M NetBIOS Filter Commands ...
Страница 638: ...ZyWALL 5 User s Guide 636 Appendix O Brute Force Password Guessing Protection ...
Страница 660: ...ZyWALL 5 User s Guide 658 Appendix Q Log Descriptions ...






























