Chapter 10 Wireless LAN
WRE6606 User’s Guide
57
• Every wireless client in the same wireless network must use security compatible with the AP.
Security stops unauthorized devices from using the wireless network. It can also protect the
information that is sent in the wireless network.
10.3.1 Wireless Security Overview
The following sections introduce different types of wireless security you can set up in the wireless
network.
10.3.1.1 MAC Address List
Every wireless client has a unique identification number, called a MAC address.
1
A MAC address is
usually written using twelve hexadecimal characters
2
; for example, 00A0C5000002 or
00:A0:C5:00:00:02. To get the MAC address for each wireless client, see the appropriate User’s
Guide or other documentation.
You can use the MAC Address List to tell the AP which wireless clients are allowed to use the
wireless network. If a wireless client is allowed to use the wireless network, it still has to have the
correct settings (SSID, channel, and security). If a wireless client is not allowed to use the wireless
network, it does not matter if it has the correct settings.
This type of security does not protect the information that is sent in the wireless network.
Furthermore, there are ways for unauthorized devices to get the MAC address of an authorized
wireless client. Then, they can use that MAC address to use the wireless network.
10.3.1.2 Encryption
Wireless networks can use encryption to protect the information that is sent in the wireless
network. Encryption is like a secret code. If you do not know the secret code, you cannot
understand the message.
For example, if users do not log in to the wireless network, you can choose no authentication, if
users do log on to the wireless network, you can choose
No Security
,
Static WEP
,
WPA-PSK
, or
WPA2-PSK
.
Usually, you should set up the strongest encryption that every wireless client in the wireless
network supports. Suppose the wireless network has two wireless clients. Device A only supports
WEP, and device B supports WEP and WPA-PSK. Therefore, you should set up
Static WEP
in the
wireless network.
1.
Some wireless devices, such as scanners, can detect wireless networks but cannot use wireless networks. These kinds
of wireless devices might not have MAC addresses.
2.
Hexadecimal characters are 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, A, B, C, D, E, and F.
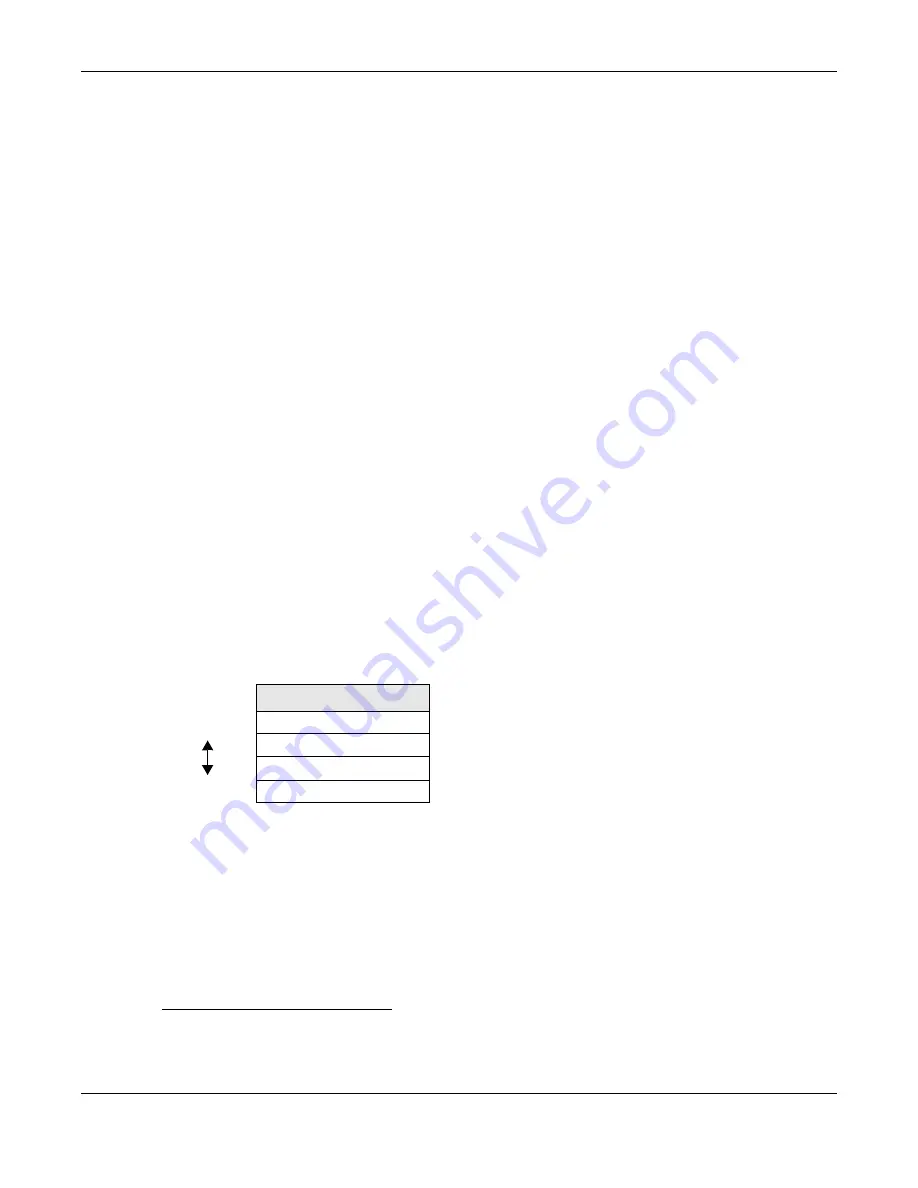
Table 16
Types of Encryption for Each Type of Authentication
NO AUTHENTICATION
Weakest
No Security
Static WEP
WPA-PSK
Strongest
WPA2-PSK
Содержание WRE6606
Страница 8: ...8 PART I User s Guide ...
Страница 53: ...53 PART II Technical Reference ...
Страница 139: ...Appendix C Legal Information WRE6606 User s Guide 139 Environmental Product Declaration ...
















































