6
7
If your network uses encryption, switch to the
Authentication and Security
tab and continue confi guration
under
Setting wireless LAN encryption
.
If your network is not encrypted, click
OK
to accept the settings. To activate the profi le created, switch to
the
Profi les
tab, select the profi le and then click
Activate.
3.2.1.2 Ad-hoc mode
First enter a name for your profi le
(Profi le name)
, e.g. “PROF1”.
If you have selected
version 1
to create the profi le, you must enter the network ID (SSID) of the target
network in the
SSID
fi eld. This is in the wireless LAN settings in your router or access point or you can ask
the person in charge. If you have selected
version 2
, the
SSID
has already been copied automatically from
the network overview.
To reduce the energy consumption, you can run the device in
Power saving mode
. In this mode, certain
functions are deactivated or run at a lower setting if they are not fully used. Select
Constantly Awake Mode
if you want to work at full power all the time.
Select
Ad-hoc
under network type. This mode allows you to connect to other wireless LAN client devices,
e.g. USB sticks, PCI cards or cardbus.
The settings for
TX Power, Preamble, RTS Threshold
and
Fragment Threshold
can be left at the default
settings.
Ad-hoc WLAN
mode allows you to set the standard to be used. This depends on the other devices
used in your network. You can then select either
802.11b
(11Mbps) only: Then this standard only is used;
802.11g
(54Mbps) only: Then this standard only is used; or
802.11b/g
: If this is selected, both standards are
supported. If you are unsure which standards your devices support, you should use the mixed mode. You
must also set the wireless LAN channel used under
Channel
. In Europe, there are 13 channels in the 2.4 GHz
frequency range.
If your network uses encryption, switch to the
Authentication and Security
tab and continue confi guration
under
Setting wireless LAN encryption.
If your network is not encrypted, click
OK
to accept the settings. To activate the profi le created, switch to the
Profi les
tab, select the profi le and then click
Activate
.
3.2.2 Setting the wireless LAN encryption
First, it is important to understand a range of terms. The next section will explain the main terms
used here:
Authentication:
Authentication is a process in which the identity, e.g. of a person is determined based on a
certain characteristic. This can be done by fi ngerprint, password or any other proof of authorisation.
Encryption:
Encryption is a process in which a plain text is transformed into a coded text via an encryption
process (algorithm). One or more codes can be used for this.
It must also be mentioned that each individual encryption process offers one or more authentication options.
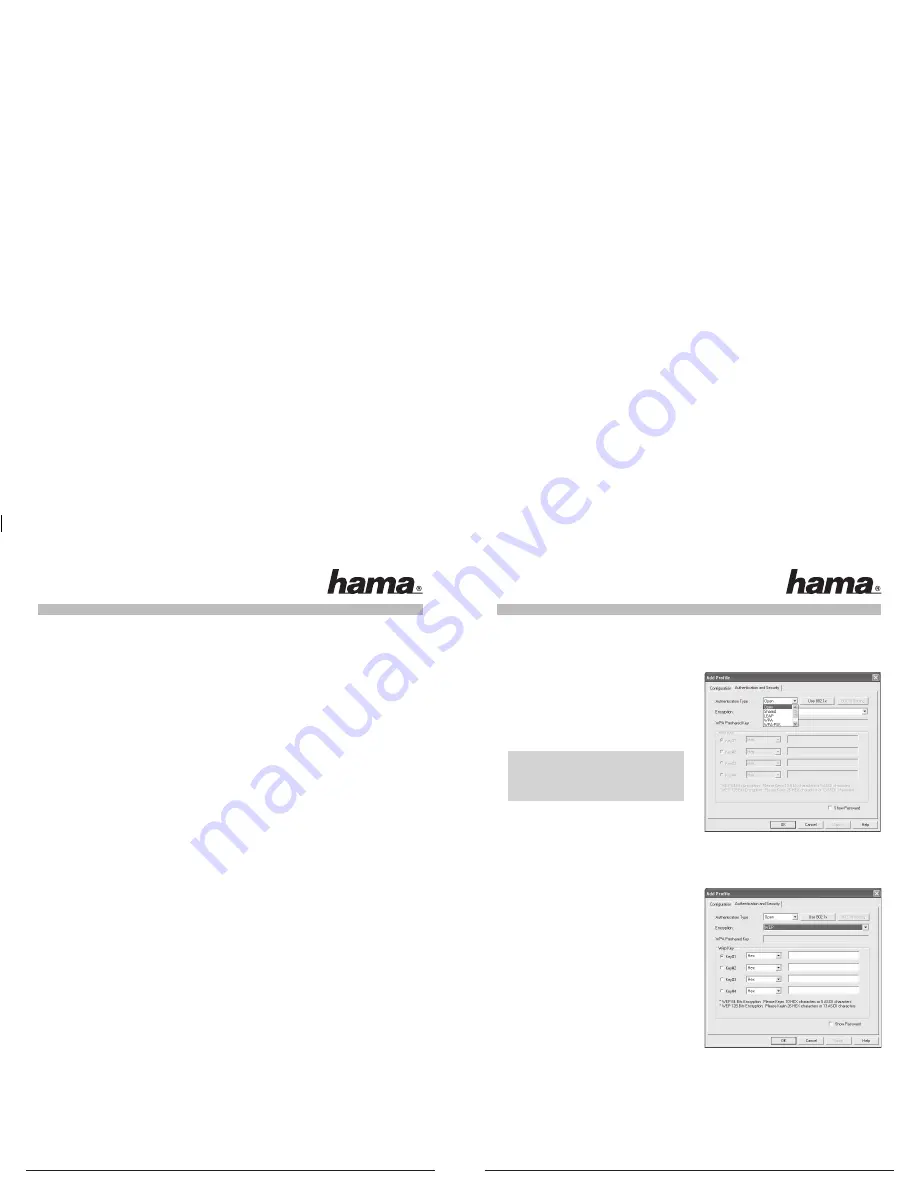
Please switch to the
Authentication and Security
tab.
This device can be used with the following encryption
types:
64 and 128 bit WEP encryption
WPA and WPA2 encryption
Note!!! Encryption is deactivated by default.
However, for security reasons, we recommend
that you always use encryption.
3.2.2.1 WEP encryption
Wired Equivalent Privacy
(WEP)
is a standard encryption algorithm for WLAN. It both controls the access to
the network and guarantees the integrity of the data. This method is considered vulnerable due to a range of
weaknesses.
If you want to use WEP encryption, select
WEP
under
encryption.
Two options are available for the Authentication type
under WEP.
Select
Open
if all clients are to be enabled for WLAN.
Now there is virtually no other authentication.
Select
Shared
if you want to use authentication with the
challenge response process. A shared code is used for
authentication in this method. All WLAN users must know
this code.
All other selection options under Authentication type are
meaningless under WEP.



























