SIEMENS 5881 Broadband Internet Router
User’s Guide
Chapter 6 Security Setup
NAT
SIEMENS
50
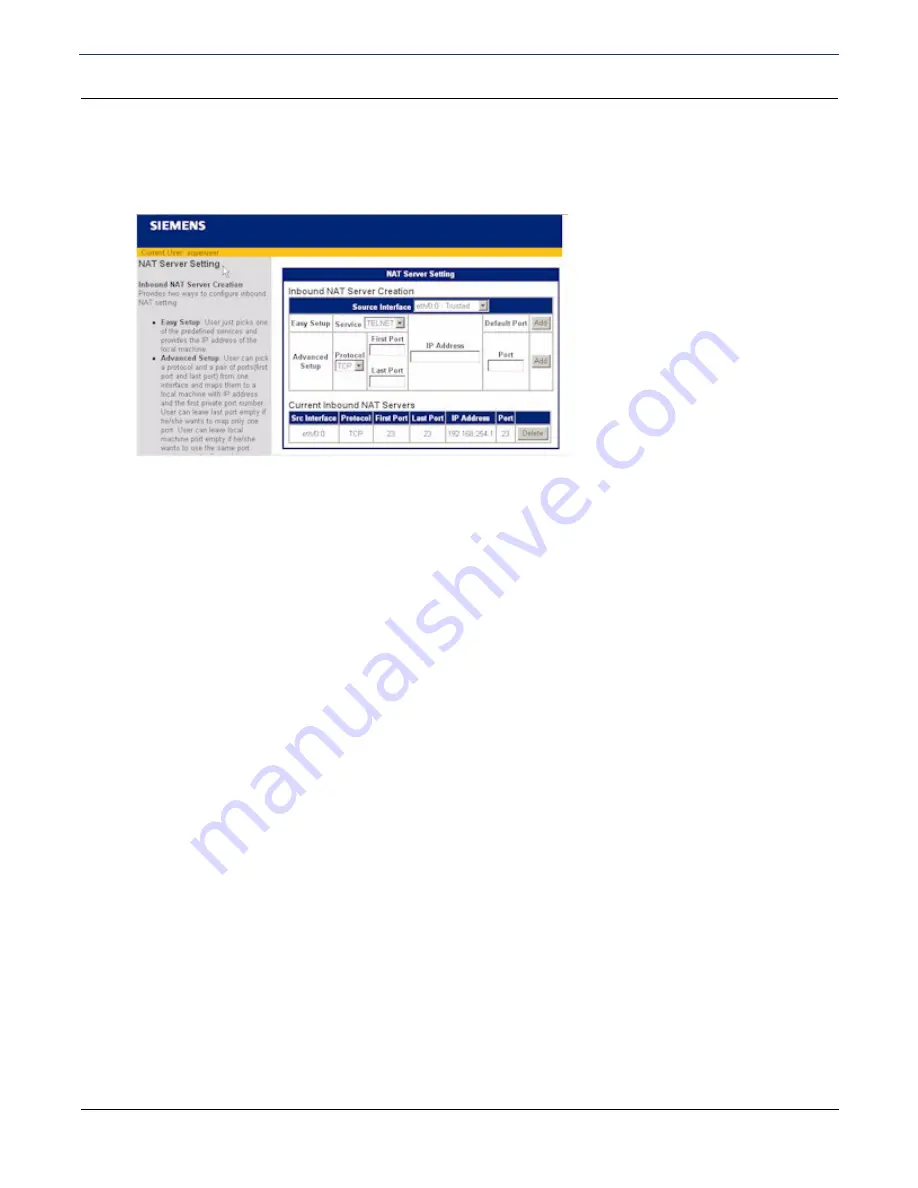
Configure the NAT Server
To configure NAT for inbound traffic:
1. Click
NAT Server
on the left navigation pane. This displays the NAT Server Settings page.
2. Select the interface you want to configure from the
Source Interface
drop-down menu.
3. Do one of the following:
•
Select the network service you are configuring from the
Service
drop-down menu for Easy Setup.
This
configures NAT to support the most common network services.
•
For Advanced Setup, select a protocol from the
Protocol
drop-down menu and specify a
First Port #
to
assign a port number for the protocol to use. To assign a range of port numbers,
specify a
Last Port #
as well.
4. Enter the IP address of the local machine in
IP Address
.
5. Do one of the following to enter port
Information for the selected service:
•
Click
Add
next to
Default Port #
to use the default port for the specified service.
•
Enter the port number on the local machine you want the specified service to use in
Port #
, and click
Add
. Leave this field blank if you want the local machine to use the same port number as the WAN.






























