22
ZENworks Endpoint Security Client 4.0 User Guide
no
vd
ocx
(e
n)
13
Ma
y 20
09
If you do not have rights to perform a check in, the
Check In
button is greyed out.
The Check In window displays the current state of the check in process. It shows the
management and distribution servers if this is a managed client, the policy type, the last time a
check in was attempted and the last time it succeeded, and the check in status.
3
To perform a manual check in, click the
Manual Check In
button. The information in the Check
In window updates accordingly.
The
Logon
button lets you log into the Policy Distribution Service. For details, see
Section 2.2,
“Logging In to the Endpoint Security Client 4.0,” on page 12
.
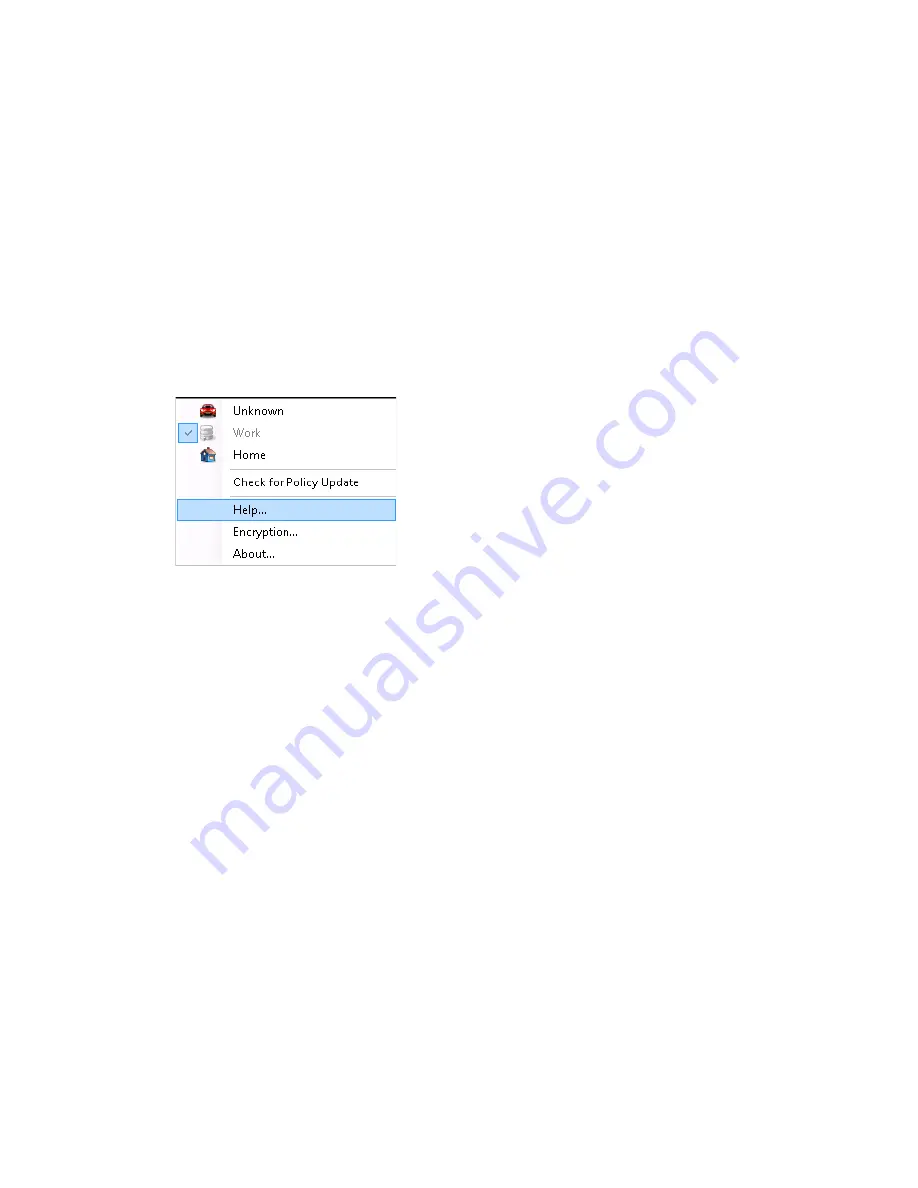
3.5 Viewing Help
1
Right-click the
Endpoint Security Client
icon in the taskbar to display the menu.
2
Click
Help
.
3.6 Overriding a Password
Productivity interruptions that a user might experience because of restrictions to connectivity,
software, or thumb drives are probably caused by the security policy the Endpoint Security Client
4.0 is enforcing. Changing locations or firewall settings usually lifts these restrictions and restores
the interrupted functionality. However, in some cases the restriction could be implemented in such a
way that it affects all locations and firewall settings. When this is the case, the restrictions must be
temporarily lifted to allow productivity.
The Endpoint Security Client 4.0 is equipped with a Password Override feature that temporarily
disables the current security policy to permit the necessary activity. The Security Administrator
distributes a single-use password key only when needed, and should be informed of any problems
with a security policy. After the password key’s time limit has expired (set by the administrator), the
security policy protecting the endpoint is restored. Rebooting the endpoint also restores the security
settings.
To activate the password override:
1
Contact your company's ESM Administrator to get the password key
2
Right-click the
Endpoint Security Client
icon in the taskbar to display the menu, then click
About
, or double-click the
Endpoint Security Client
icon.
Summary of Contents for ZENworks Endpoint Security Client 4.0
Page 4: ...4 ZENworks Endpoint Security Client 4 0 User Guide novdocx en 13 May 2009...
Page 6: ...6 ZENworks Endpoint Security Client 4 0 User Guide novdocx en 13 May 2009...
Page 8: ...8 ZENworks Endpoint Security Client 4 0 User Guide novdocx en 13 May 2009...
Page 14: ...14 ZENworks Endpoint Security Client 4 0 User Guide novdocx en 13 May 2009...



































