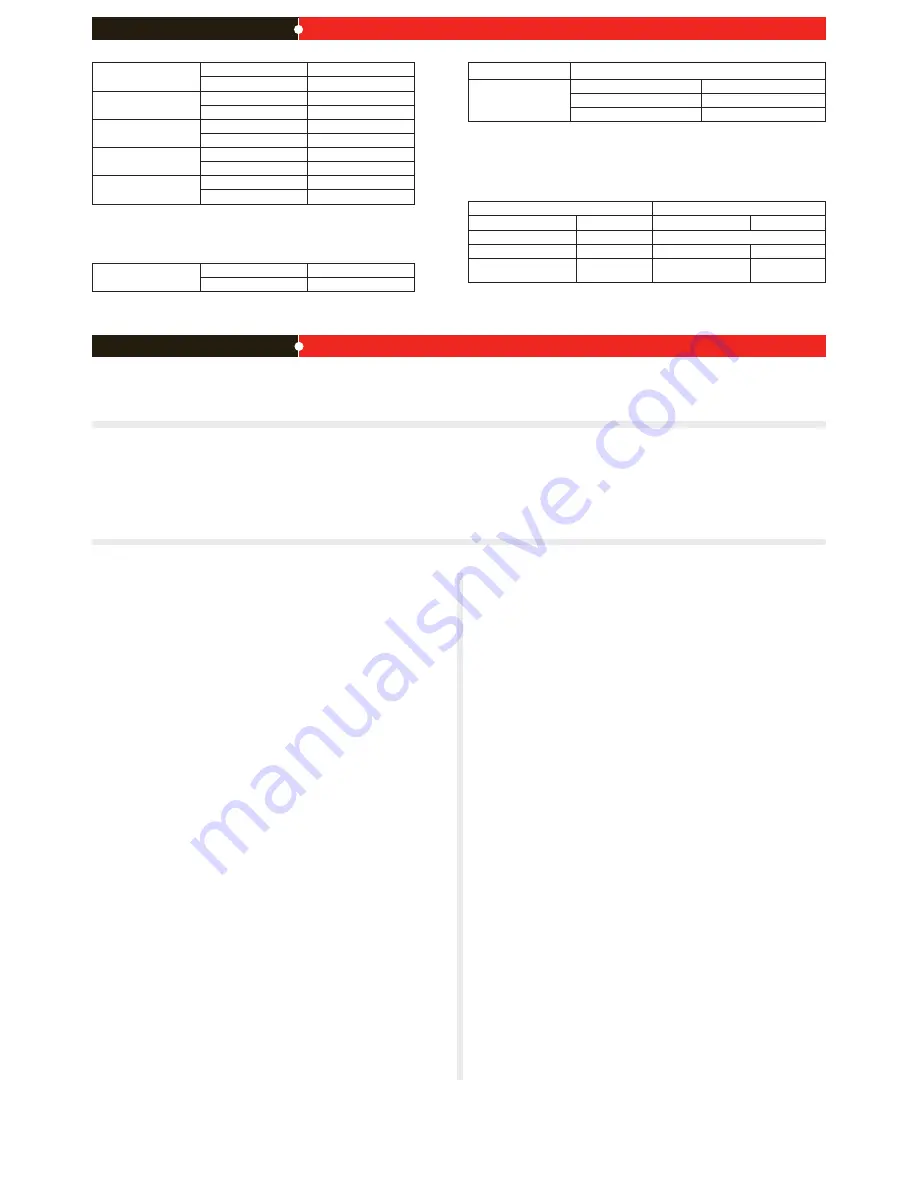
NAT/Route Mode
Port
IP:
____.____.____.____
Netmask:
____.____.____.____
Port
IP:
____.____.____.____
Netmask:
____.____.____.____
Port
IP:
____.____.____.____
Netmask:
____.____.____.____
Port
IP:
____.____.____.____
Netmask:
____.____.____.____
Port
IP:
____.____.____.____
Netmask:
____.____.____.____
The internal interface IP address and netmask must be valid for the internal network.
Transparent mode
Management IP:
IP:
____.____.____.____
Netmask:
____.____.____.____
The management IP address and netmask must be valid for the network from which you will
manage the FortiGate unit.
General settings
Administrator password:
Network Settings:
Default Gateway:
____.____.____.____
Primary DNS Server:
____.____.____.____
Secondary DNS Server:
____.____.____.____
A default gateway is required for the FortiGate unit to route connections to the Internet.
Factory default settings
NAT/Route mode
Transparent mode
Port 1 interface
192.168.1.99
Management IP
0.0.0.0
Port 2 interface
192.168.100.99
Administrative account settings
Port 3 to 10 interface
0.0.0.0
User name
admin
DHCP server on Internal
interface
192.168.1.110
– 192.168.1.210
Password
(none)
To reset the FortiGate unit to the factory defaults, in the CLI type the command
execute factory reset
Web-based Manager
Connect the FortiGate internal interface to a management computer Ethernet interface.
Use a cross-over Ethernet cable to connect the devices directly. Use straight-through
Ethernet cables to connect the devices through a hub or switch.
Configure the management computer to be on the same subnet as the internal interface
of the FortiGate unit. To do this, change the IP address of the management computer to
192.168.1.2 and the netmask to 255.255.255.0.
To access the FortiGate web-based manager, start Internet Explorer and browse to
https://192.168.1.99 (remember to include the “s” in https://).
Type admin in the Name field and select Login.
NAT/Route mode
To change the administrator password
Go to
System > Admin > Administrators
.
Select Change Password for the admin administrator and enter a new password.
To configure interfaces
Go to
System > Network > Interface
.
Select the edit icon for each interface to configure.
Set the addressing mode for the interface. (See the online help for information.)
For manual addressing, enter the IP address and netmask for the interface.
For DHCP addressing, select DHCP and any required settings.
For PPPoE addressing, select PPPoE, and enter the username and password and
any other required settings.
To configure the Primary and Secondary DNS server IP addresses
Go to
System > Network > Options
, enter the Primary and Secondary DNS IP ad-
dresses that you recorded above and select Apply.
To configure a Default Gateway
Go to
Router > Static
and select Edit icon for the static route.
Set Gateway to the Default Gateway IP address you recorded above and select OK.
Transparent mode
To switch from NAT/route mode to transparent mode
Go to
System > Config > Operation Mode
and select Transparent.
Set the Management IP/Netmask to 192.168.1.99/24.
Set a default Gateway and select Apply.
To change the administrator password
Go to
System > Admin > Administrators
.
Select Change Password for the admin administrator and enter a new password.
To change the management interface
Go to
System > Config > Operation Mode
.
Enter the Management IP address and netmask that you recorded above and select
Apply.
To configure the Primary and Secondary DNS server IP addresses
Go to
System > Network > Options
, enter the Primary and Secondary DNS IP ad-
dresses that you recorded above and select Apply.
1.
2.
3.
4.
1.
2.
1.
2.
3.
•
•
•
1.
1.
2.
1.
2.
3.
1.
2.
1.
2.
1.
Command Line Interface
Use the RJ-45 to DB9 serial cable to connect the FortiGate Console port to the man-
agement computer serial port.
Start a terminal emulation program (HyperTerminal) on the management computer. Use
these settings:
Baud Rate (bps) 9600, Data bits 8, Parity None, Stop bits 1, and Flow Control None.
At the Login: prompt, type admin and press Enter twice (no password required).
NAT/Route mode
Configure the FortiGate internal interface.
config system interface
edit internal
set ip <intf_ip>/<netmask_ip>
end
Repeat to configure each interface, for example, to configure the Port 1 interface.
config system interface
edit port1
...
Configure the primary and secondary DNS server IP addresses.
config system dns
set primary <dns-server_ip>
set secondary <dns-server_ip>
end
Configure the default gateway.
config router static
edit 1
set gateway <gateway_ip>
end
Transparent Mode
Change from NAT/Route mode to Transparent mode and configure the Management IP
address.
config system settings
set opmode transparent
set manageip <mng_ip>/<netmask>
set gateway <gateway_ip>
end
Configure the DNS server IP address.
config system dns
set primary <dns-server_ip>
set secondary <dns-server_ip>
end
1.
2.
3.
4.
1.
2.
3.
4.
1.
2.
Collecting Information
Configuring
NAT/Route mode
You would typically use NAT/Route mode when the FortiGate unit is deployed as a gateway
between private and public networks. In its default NAT/Route mode configuration, the unit
functions as a firewall. Firewall policies control communications through the FortiGate unit.
Transparent mode
You would typically use the FortiGate unit in Transparent mode on a private network behind
an existing firewall or behind a router. In its default Transparent mode configuration, the unit
functions as a firewall.
Refer to the Tools and Documentation CD for information on how to control traffic, and how to configure HA, antivirus protection, FortiGuard, Web content filtering, Spam filtering, intrusion
prevention (IPS), and virtual private networking (VPN).
Upgrading to High Encryption
This FortiGate unit has a factory installed low encryption feature set. You can purchase a high encryption upgrade within 90 days of shipment from Fortinet. Fortinet Technical Support can
provide a high encryption license key once you have provided suitable documentation that the necessary export licenses have been granted for your region, and our legal department has
authorized the use of high encryption.
When you receive the high encryption license key, in the CLI, enter the command
exec crypto-license <high-enc-key>
.
Fortinet does not guarantee that the customer will receive a export license upon purchase of the product or license key.






