AVG 9 Internet Security © 2009 C opyright AVG Technologies C Z, s.r.o. All rights reserved.
155
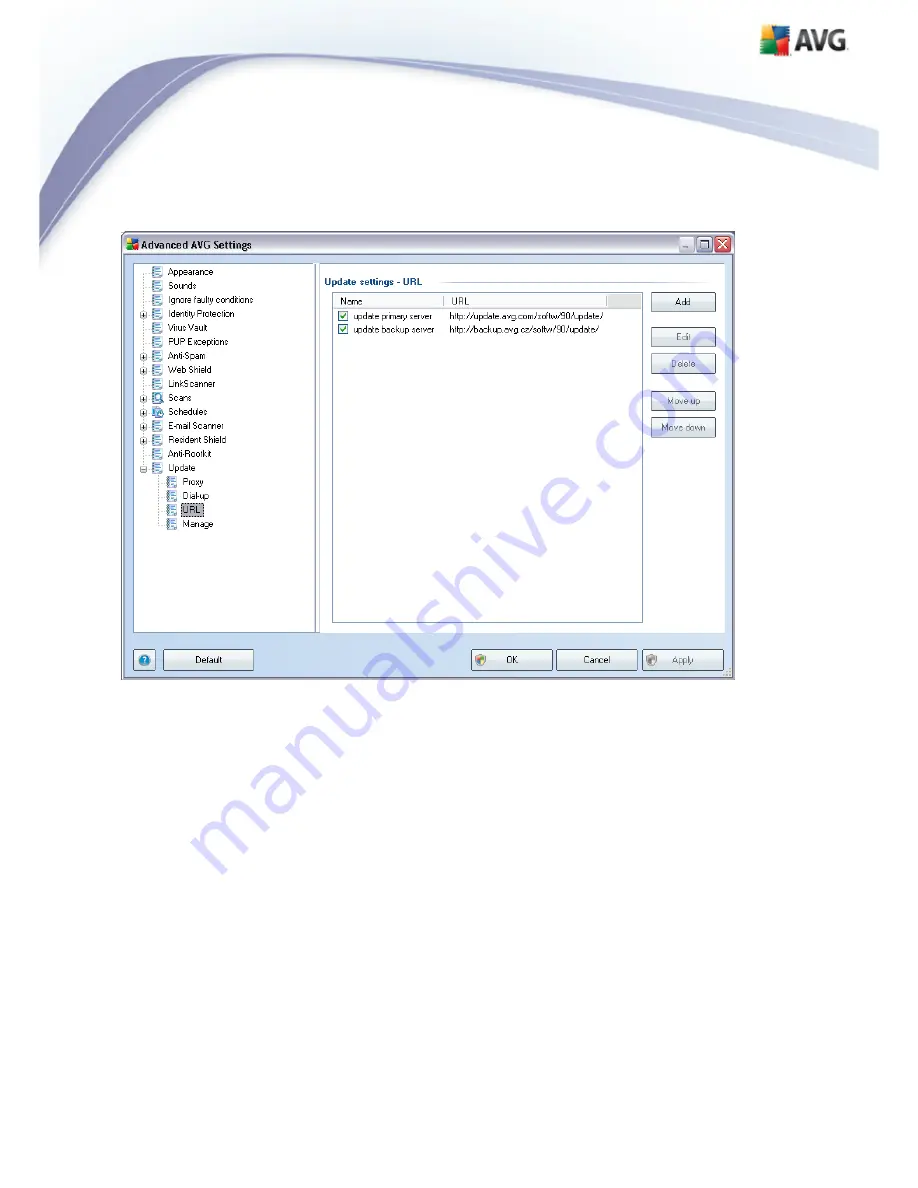
9.15.3. URL
The
URL
dialog offers a list of Internet addresses from which the update files can be
downloaded. The list and its items can be modified using the following control buttons:
·
Add
– opens a dialog where you can specify a new URL to be added to the list
·
Edit
- opens a dialog where you can edit the selected URL parameters
·
Delete
– deletes the selected URL from the list
·
Move Up
– moves the selected URL one position up in the list
·
Move Down
- moves the selected URL one position down in the list






























