295
Figure 313 RADIUS packet format
The following describes the fields of a RADIUS packet:
•
The Code field (1 byte long) indicates the type of the RADIUS packet.
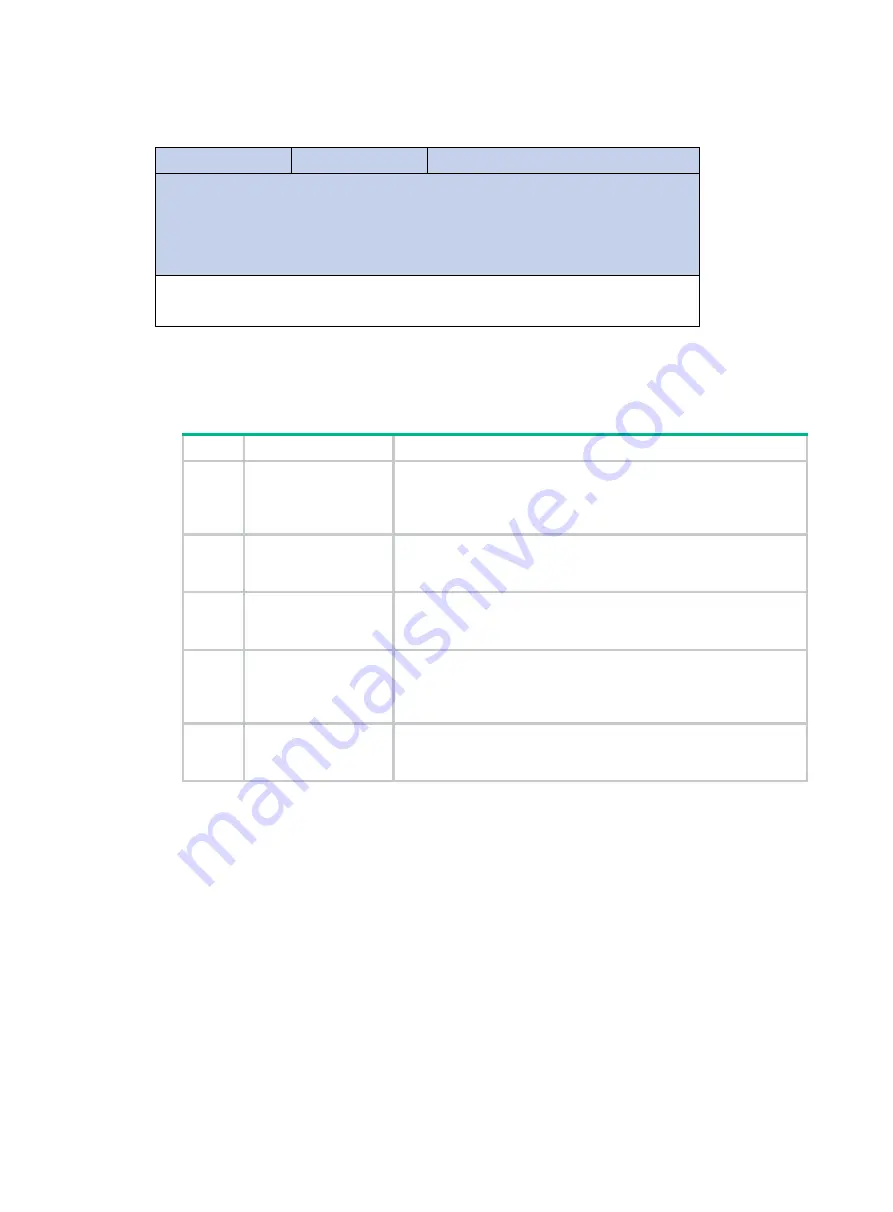
Table 105 Main values of the Code field
Code Packet
type
Description
1 Access-Request
From the client to the server. A packet of this type carries user
information for the server to authenticate the user. It must contain
the User-Name attribute and can optionally contain the attributes of
NAS-IP-Address, User-Password, and NAS-Port.
2 Access-Accept
From the server to the client. If all attribute values carried in the
Access-Request are acceptable, the authentication succeeds, and
the server sends an Access-Accept response.
3 Access-Reject
From the server to the client. If any attribute value carried in the
Access-Request is unacceptable, the authentication fails, and the
server sends an Access-Reject response.
4 Accounting-Request
From the client to the server. A packet of this type carries user
information for the server to start or stop accounting for the user.
The Acct-Status-Type attribute in the packet indicates whether to
start or stop accounting.
5 Accounting-Response
From the server to the client. The server sends a packet of this type
to notify the client that it has received the Accounting-Request and
has successfully recorded the accounting information.
•
The Identifier field (1 byte long) is used to match request packets and response packets and to
detect duplicate request packets. Request and response packets of the same type have the
same identifier.
•
The Length field (2 bytes long) indicates the length of the entire packet, including the Code,
Identifier, Length, Authenticator, and Attribute fields. Bytes beyond this length are considered
padding and are neglected upon reception. If the length of a received packet is less than this
length, the packet is dropped. The value of this field is in the range 20 to 4096.
•
The Authenticator field (16 bytes long) is used to authenticate replies from the RADIUS server
and to encrypt user passwords. There are two types of authenticators: request authenticator
and response authenticator.
•
The Attributes field, variable in length, carries the specific authentication, authorization, and
accounting information that defines the configuration details of the request or response. This
field may contain multiple attributes, each with three sub-fields:
{
Type
—(1 byte long) Type of the attribute. It is in the range 1 to 255. Commonly used
attributes for RADIUS authentication, authorization and accounting are listed in
.
Code
Attributes
Identifier
0
7
Length
Authenticator
7
15
31
Summary of Contents for FlexNetwork NJ5000
Page 12: ...x Index 440 ...
Page 39: ...27 Figure 16 Configuration complete ...
Page 67: ...55 Figure 47 Displaying the speed settings of ports ...
Page 78: ...66 Figure 59 Loopback test result ...
Page 158: ...146 Figure 156 Creating a static MAC address entry ...
Page 183: ...171 Figure 171 Configuring MSTP globally on Switch D ...
Page 243: ...231 Figure 237 IPv6 active route table ...
















































