CHAPTER 6
255
Administration with Web Console
6.9.4
Lists and Templates
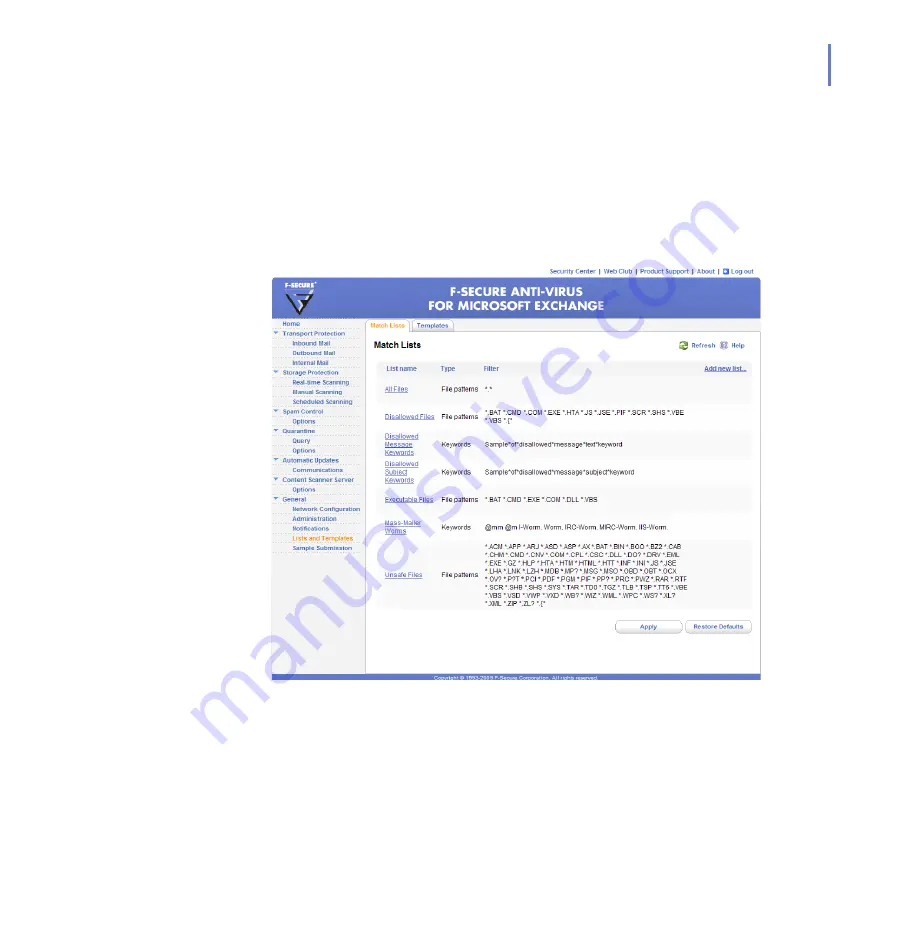
Match Lists are lists of file name patterns, keywords, or e-mail addresses
that can be used with certain product settings.
Message Templates can be used for notification messages.
Match Lists
Summary of Contents for ANTI-VIRUS FOR MICROSOFT EXCHANGE 8.00 -
Page 1: ...F Secure Anti Virus for Microsoft Exchange Administrator s Guide...
Page 9: ...9 ABOUT THIS GUIDE How This Guide Is Organized 10 Conventions Used in F Secure Guides 13...
Page 23: ...23 2 DEPLOYMENT Installation Modes 24 Network Requirements 25 Deployment Scenarios 26...
Page 296: ...296 A APPENDIX Variables in Warning Messages List of Variables 297...
Page 299: ...299 B APPENDIX Services and Processes List of Services and Processes 300...
Page 332: ...332 D APPENDIX Sending E mail Alerts And Reports Overview 333 Solution 333...
Page 349: ......






























