User's Manual
8
Parameter
Description
Transmit Power
●
Select from high, low, and automatic.
●
The higher the transmission power, the farther the
transmission and the higher power consumption.
Cloud Update
Update online.
Delete
Delete the online accessory.
Go to the
Hub
interface, select the accessory from the
list, and then swipe left to delete it.
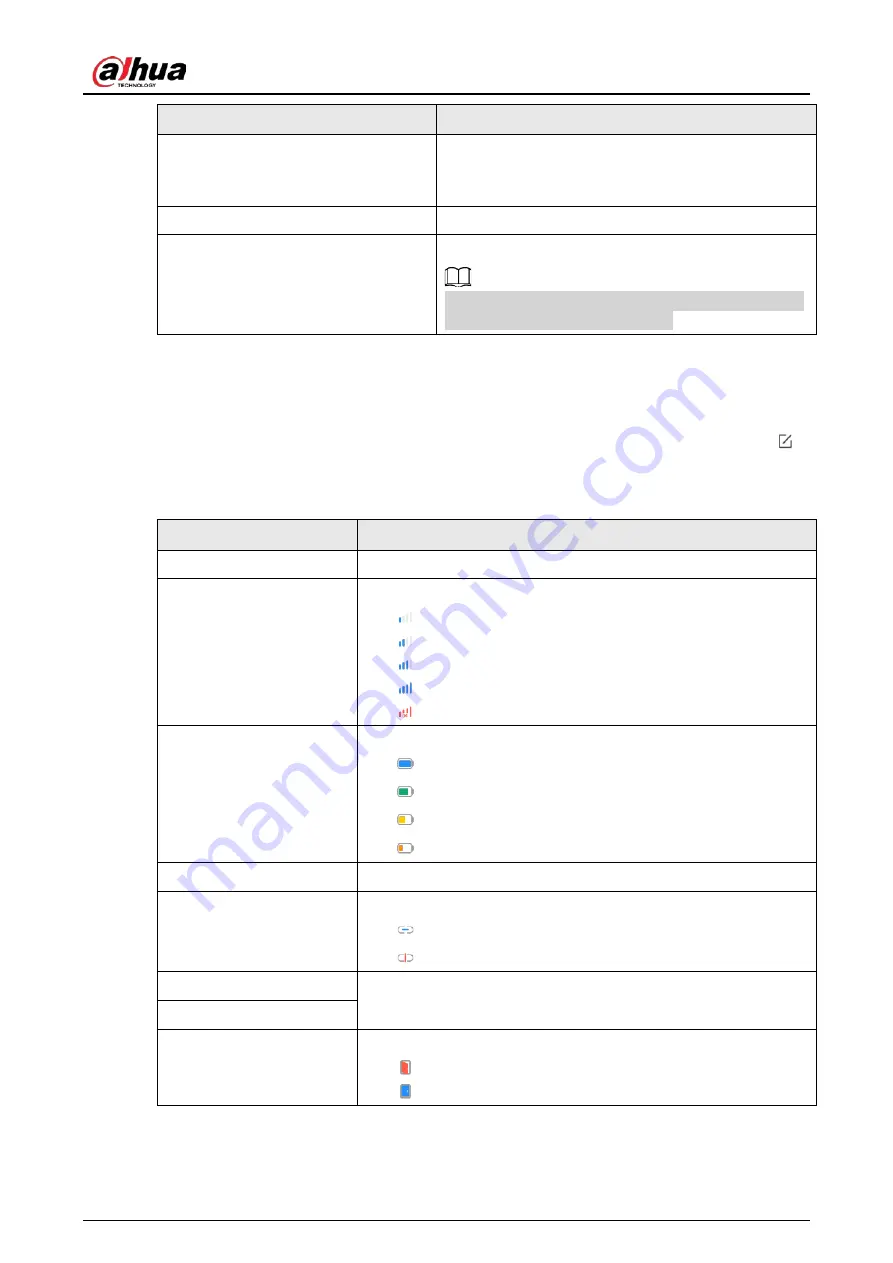
6.2 Viewing Status of the Door Detector
On the
Hub
interface, select the door detector as needed from the accessory list, and then tab
to view the status of the door detector.
Table 6-2 Status
Parameter
Value
Temperature
The temperature of the environment.
Signal Strength
The signal strength between the hub and the door detector.
●
: Ultra low.
●
: Low.
●
: Moderate.
●
: High.
●
: No.
Battery Level
The battery level of the detector.
●
: Fully charged.
●
: Sufficient.
●
: Moderate.
●
: Insufficient.
Anti-tampering Status
Anti-tampering status of the door detector.
Online Status
Online and offline status of the door detector.
●
: Online.
●
: Offline.
Entrance Delay Time
Entrance and exit delay time.
Exit Delay Time
Door Status
Open or close status of the door.
●
: Open.
●
: Close.

















