Chapter 12 VoIP Trunking
P-2602HWLNI User’s Guide
212
Other settings controlled by the auto attendant include a time limit to decide whether you want
to forward a call from the ZyXEL Device or call the phone directly connected to the ZyXEL
Device. When you call into your ZyXEL Device you can request to forward a call to another
phone number simply by dialing that number. If you don’t dial any number within a specified
time limit (for example 5 seconds) then the phone directly connected to the ZyXEL Device
rings. It also controls the time limit you have between dialing digits of a phone number.
12.2.2 Peer Call Authentication
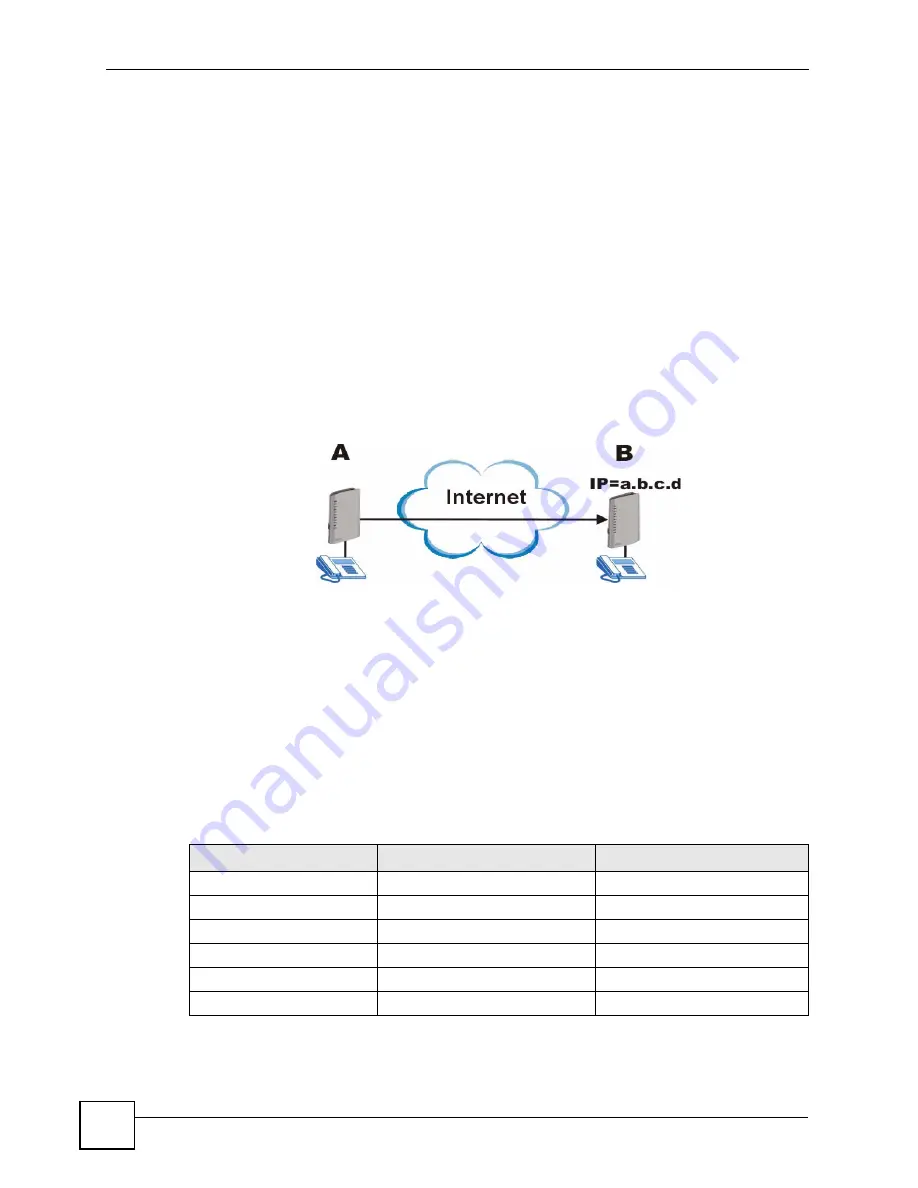
VoIP devices can make peer calls to each other by using the IP address instead of a SIP
number to establish a call. The advantage of this is that you do not need to pay a VoIP service
provider. VoIP devices that connect using an IP address are referred to here as peer devices. A
local peer device is where the VoIP call originates and a remote peer device is where the VoIP
call ends. In the following figure, local peer device (
A
) connects to a remote peer device (
B
)
via the IP address of
B
.
Figure 119
Peer Devices Connecting
A peer-to-peer call doesn’t require any authentication, however, authentication is required
when you request the remote peer device to forward a call. The remote peer device has a list of
accounts, each consisting of a username and password, which are allowed to use the remote
peer device to forward calls. These accounts make up an incoming
authentication list.
The local peer device has a corresponding list of outgoing
authentication
accounts. These
accounts consist of the IP address of a remote peer device, the port number to communicate
over as well as a username and password to use for authentication. An outgoing authentication
account must match an incoming authentication account’s username and password in order for
the remote device to forward calls. The following table shows example entries for incoming
and outgoing authentication. The bolded entries must match in order for authentication
between two peer devices to occur.
Table 80
Matching Incoming and Outgoing Authentication
ACCOUNT DETAILS
LOCAL PEER DEVICE
REMOTE PEER DEVICE
Outgoing Authentication
Username
localDeviceA
localDeviceB
Password
passwordA
passwordB
Incoming Authentication
Username
userone
localDeviceA
Password
userpassword
passwordA
Summary of Contents for P-2602HWLNI
Page 2: ......
Page 7: ...Safety Warnings P 2602HWLNI User s Guide 7...
Page 8: ...Safety Warnings P 2602HWLNI User s Guide 8...
Page 24: ...Table of Contents P 2602HWLNI User s Guide 24...
Page 32: ...List of Figures P 2602HWLNI User s Guide 32...
Page 38: ...List of Tables P 2602HWLNI User s Guide 38...
Page 39: ...39 PART I Introduction Introducing the ZyXEL Device 41 Introducing the Web Configurator 49...
Page 40: ...40...
Page 60: ...Chapter 2 Introducing the Web Configurator P 2602HWLNI User s Guide 60...
Page 62: ...62...
Page 86: ...Chapter 5 Bandwidth Management Wizard P 2602HWLNI User s Guide 86...
Page 98: ...Chapter 6 Status Screens P 2602HWLNI User s Guide 98...
Page 100: ...100...
Page 154: ...Chapter 9 Wireless LAN P 2602HWLNI User s Guide 154...
Page 166: ...Chapter 10 Network Address Translation NAT Screens P 2602HWLNI User s Guide 166...
Page 167: ...167 PART IV VoIP Voice 169 VoIP Trunking 211 Phone Usage 227...
Page 168: ...168...
Page 226: ...Chapter 12 VoIP Trunking P 2602HWLNI User s Guide 226...
Page 230: ...Chapter 13 Phone Usage P 2602HWLNI User s Guide 230...
Page 232: ...232...
Page 264: ...Chapter 15 Firewall Configuration P 2602HWLNI User s Guide 264...
Page 268: ...Chapter 16 Content Filtering P 2602HWLNI User s Guide 268...
Page 274: ...Chapter 17 Introduction to IPSec P 2602HWLNI User s Guide 274...
Page 309: ...Chapter 19 Certificates P 2602HWLNI User s Guide 309 Figure 173 My Certificate Details...
Page 320: ...Chapter 19 Certificates P 2602HWLNI User s Guide 320 Figure 181 Trusted Remote Host Details...
Page 326: ...326...
Page 330: ...Chapter 20 Static Route P 2602HWLNI User s Guide 330...
Page 338: ...Chapter 21 Bandwidth Management P 2602HWLNI User s Guide 338...
Page 342: ...Chapter 22 Dynamic DNS Setup P 2602HWLNI User s Guide 342...
Page 360: ...Chapter 23 Remote Management Configuration P 2602HWLNI User s Guide 360...
Page 372: ...Chapter 24 Universal Plug and Play UPnP P 2602HWLNI User s Guide 372...
Page 374: ...374...
Page 380: ...Chapter 25 System P 2602HWLNI User s Guide 380...
Page 406: ...Chapter 28 Troubleshooting P 2602HWLNI User s Guide 406...
Page 422: ...Chapter 30 Diagnostic P 2602HWLNI User s Guide 422...
Page 432: ...Chapter 31 Product Specifications P 2602HWLNI User s Guide 432...
Page 434: ...434...
Page 446: ...Appendix A Setting up Your Computer s IP Address P 2602HWLNI User s Guide 446...
Page 482: ...Appendix F Legal Information P 2602HWLNI User s Guide 482...
Page 488: ...Appendix G Customer Support P 2602HWLNI User s Guide 488...






























