Chapter 3 Internet Connection Wizard
User’s Guide
55
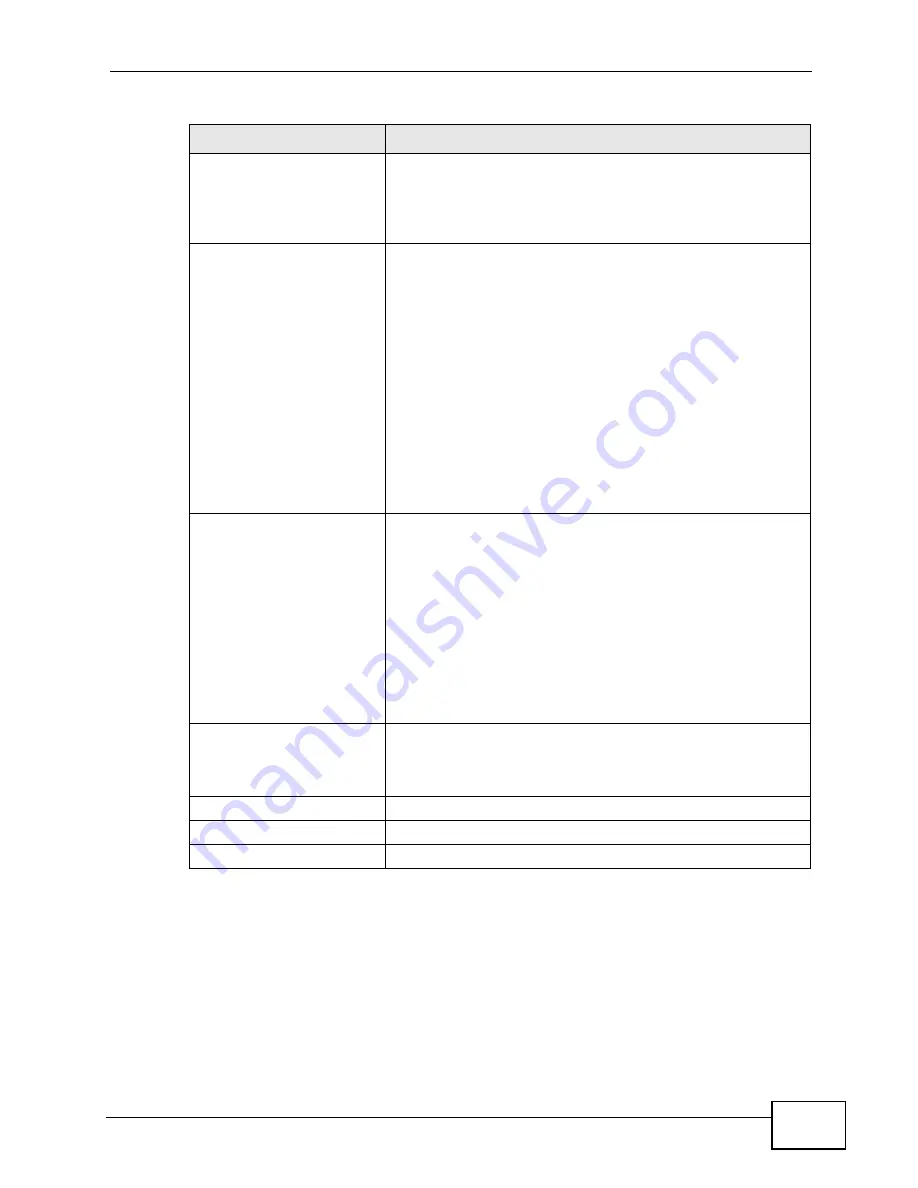
PKM
This field displays the Privacy Key Management version
number. PKM provides security between the WiMAX Device
and the base station. At the time of writing, the WiMAX
Device supports PKMv2 only. See the WiMAX security
appendix for more information.
Authentication
This field displays the user authentication method.
Authentication is the process of confirming the identity of a
mobile station (by means of a username and password, for
example).
Check with your service provider if you are unsure of the
correct setting for your account.
Choose from the following user authentication methods:
• TTLS (Tunnelled Transport Layer Security)
• TLS (Transport Layer Security)
Note: Not all WiMAX Devices support TLS
authentication. Check with your service provider
for details.
TTLS Inner EAP
This field displays the type of secondary authentication
method. Once a secure EAP-TTLS connection is established,
the inner EAP is the protocol used to exchange security
information between the mobile station, the base station and
the AAA server to authenticate the mobile station. See the
WiMAX security appendix for more details. The WiMAX
Device supports the following inner authentication types:
• CHAP (Challenge Handshake Authentication Protocol)
• MSCHAP (Microsoft CHAP)
• MSCHAPV2 (Microsoft CHAP version 2)
• PAP (Password Authentication Protocol)
Certificate
This is the security certificate the WiMAX Device uses to
authenticate the AAA server. Use the TOOLS > Certificates
> Trusted CA screen to import certificates to the WiMAX
Device.
Back
Click to display the previous screen.
Next
Click to proceed to the next screen.
Exit
Click to close the wizard without saving.
Table 11
Internet Connection Wizard > Authentication Settings Screen (continued)
LABEL
DESCRIPTION
Summary of Contents for MAX-306
Page 2: ......
Page 8: ...Safety Warnings User s Guide 8...
Page 10: ...Contents Overview User s Guide 10...
Page 30: ...30...
Page 36: ...Chapter 1 Getting Started User s Guide 36...
Page 46: ...Chapter 2 Introducing the Web Configurator User s Guide 46...
Page 64: ...Chapter 4 VoIP Connection Wizard User s Guide 64...
Page 65: ...65 PART II Basic Screens The Main Screen 40 The Setup Screens 67...
Page 66: ...66...
Page 74: ...74...
Page 88: ...Chapter 6 The LAN Configuration Screens User s Guide 88...
Page 112: ...Chapter 8 The Wi Fi Configuration Screens User s Guide 112...
Page 134: ...Chapter 10 The NAT Configuration Screens User s Guide 134...
Page 146: ...146...
Page 164: ...Chapter 12 The Service Configuration Screens User s Guide 164...
Page 180: ...Chapter 14 The Phone Book Screens User s Guide 180...
Page 182: ...182...
Page 202: ...Chapter 15 The Certificates Screens User s Guide 202...
Page 212: ...Chapter 16 The Firewall Screens User s Guide 212...
Page 226: ...Chapter 18 The Remote Management Screens User s Guide 226...
Page 242: ...Chapter 19 The Logs Screens User s Guide 242...
Page 252: ...Chapter 20 The UPnP Screen User s Guide 252...
Page 265: ...265 PART VI Troubleshooting and Specifications Troubleshooting 267 Product Specifications 275...
Page 266: ...266...
Page 274: ...Chapter 22 Troubleshooting User s Guide 274...
Page 278: ...278...
Page 310: ...Appendix B Setting Up Your Computer s IP Address User s Guide 310...
Page 336: ...Appendix D Pop up Windows JavaScripts and Java Permissions User s Guide 336...
Page 380: ...Appendix F Importing Certificates User s Guide 380...
Page 382: ...Appendix G SIP Passthrough User s Guide 382...
Page 398: ...Appendix J Customer Support User s Guide 398...
Page 405: ...Index User s Guide 405...






























