ZyXEL G-220 v3 User’s Guide
110
Appendix D Wireless Security
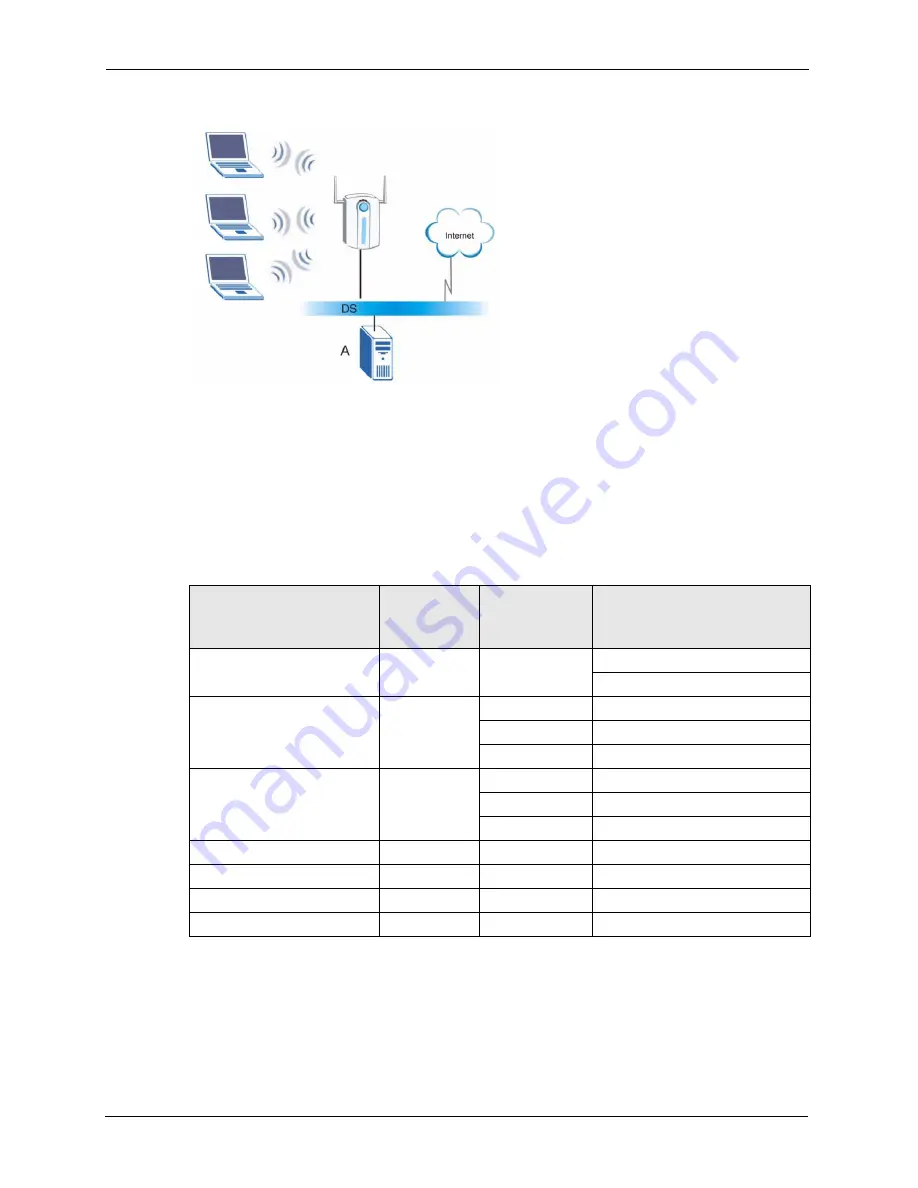
Figure 74
WPA(2) with RADIUS Application Example
Security Parameters Summary
Refer to this table to see what other security parameters you should configure for each
Authentication Method/ key management protocol type. MAC address filters are not
dependent on how you configure these security features.
Table 33
Wireless Security Relational Matrix
AUTHENTICATION
METHOD/ KEY
MANAGEMENT PROTOCOL
ENCRYPTION
METHOD
ENTER
MANUAL KEY
IEEE 802.1X
Open
None
No
Disable
Enable without Dynamic WEP Key
Open
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
Shared
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
WPA
TKIP/AES
No
Enable
WPA-PSK
TKIP/AES
Yes
Disable
WPA2
TKIP/AES
No
Enable
WPA2-PSK
TKIP/AES
Yes
Disable
Summary of Contents for G-220 v3
Page 1: ...ZyXEL G 220 v3 802 11g Wireless USB Adapter User s Guide Version 2 1 0 Edition 1 04 2008...
Page 2: ......
Page 16: ...ZyXEL G 220 v3 User s Guide 16 Table of Contents...
Page 20: ...ZyXEL G 220 v3 User s Guide 20 List of Figures...
Page 22: ...ZyXEL G 220 v3 User s Guide 22 List of Tables...
Page 28: ...ZyXEL G 220 v3 User s Guide 28 Chapter 1 Getting Started...
Page 36: ...ZyXEL G 220 v3 User s Guide 36 Chapter 2 Tutorial...
Page 74: ...ZyXEL G 220 v3 User s Guide 74 Chapter 4 Wireless Station Mode Configuration...
Page 84: ...ZyXEL G 220 v3 User s Guide 84 Chapter 6 Maintenance...
Page 92: ...ZyXEL G 220 v3 User s Guide 92 Appendix B Access Point Mode Setup Example...
Page 104: ...ZyXEL G 220 v3 User s Guide 104 Appendix C Management with Wireless Zero Configuration...
Page 122: ...ZyXEL G 220 v3 User s Guide 122 Appendix E Setting up Your Computer s IP Address...
















































