42
Fingerprint Reader
CAUTION
To protect the fingerprint sensor, be sure to close the cover when not using the fingerprint reader.
We shall not be liable for any loss or damage whatsoever resulting from your Fingerprint device or neglect of Fingerprint
device use, or any data loss resulting from such developments as Fingerprint authentication device malfunctioning.
Fingerprint’s Outline
The conventional security systems use ID/passwords and token devices such as IC cards to authenticate users. Therefore
the passwords and token devices are exposed to the risk of being lost, stolen and hacking.
The Fingerprint authentication method uses user’s fingerprints instead of passwords for security authentication. You can use
your fingerprints to start up your computer and log on Windows.
We recommend you use the Fingerprint Reader in combination with the TPM (Trusted Platform Module) to increase the secu-
rity level of your computer.
To access the online manual
This manual describes Step 2, 3 and the initial part of Step 4.
For further steps, refer to the UPEK Protector Suite QL Help menu.
Click [start] - [All Programs] - [Protector Suite QL] - [Help].
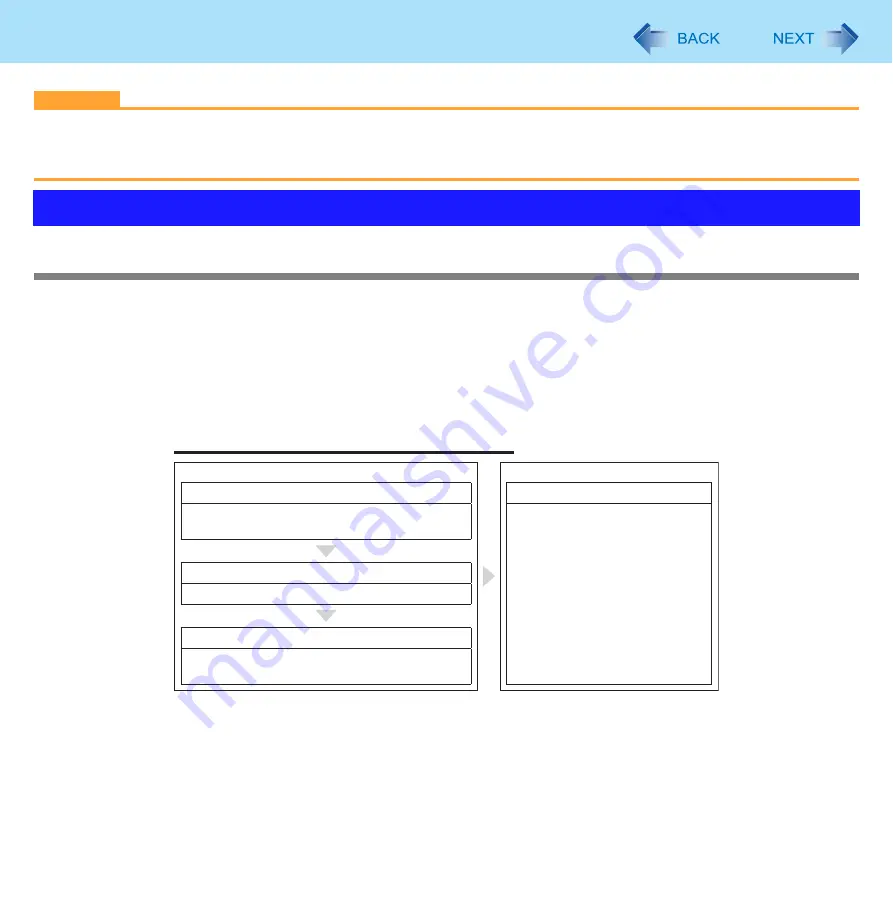
Overview
Recommended Installation Procedure
Performed by the Computer Administrator
Performed by each user
TPM Installation
(
⇒
Installation Manual of TPM)
(If the TPM is not being used, skip this step.)
User Fingerprint Enrollment
User’s Data
• Windows Logon Password
• Fingerprint
• Fingerprint Backup Password
• Power-on Password
Step 2
Step 4
Fingerprint Utility Installation
Step 3
Step 1
TPM Fingerprint Utility Initialization
(If the TPM is not being used, skip this step.)






























